Security researchers at Kaspersky have released a free decryption tool that promises to recover files for organisations hit by the Yanlouwang ransomware, meaning they don’t have to pay the ransom.
The boffins at the Russian security outfit say that they found a vulnerability in Yanlouwang’s encryption algorithm which means that it is possible for companies to decrypt and recover files without giving in to their extortionists.
Yanlouwang, which is named after a Chinese deity, first emerged in late 2021 – encrypting files in highly-targeted attacks against organisations, and exfiltrating data from networks.
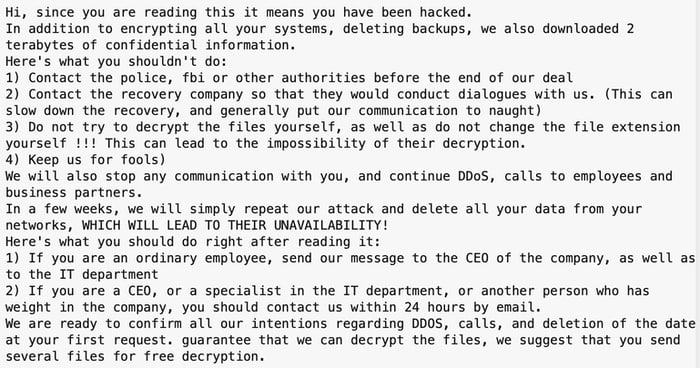
In a ransom note left for its victims, the Yanlouwang ransomware told companies not to contact law enforcement agencies or attempt to decrypt their data themselves, threatening to launch denial-of-service attacks, contact business partners, and breach systems once more in order to delete all data.
Kaspersky says that its decryption tool requires access to at least one of your original files.
Of course, Kaspersky’s free decryption tool may get you your files back but it doesn’t prevent them having been stolen, and potentially offered for sale to other criminals or published on the web.
Furthermore, recovering access to your data doesn’t plug any security holes that the attackers may have exploited in the first place to infiltrate your business.
With Russian’s invasion of Ukraine, and heightened geo-political tensions, Kaspersky has undoubtedly been having problems convincing businesses to trust its security software. But if you find yourself with your data scrambled by ransomware, I wouldn’t blame you for seeking help wherever you can find it.
Download Kaspersy’s decryption tool here.
It should go without saying, but doesn’t, that you should back up your important data (even if encrypted) before running any decryption tool.