
Marcus Hutchins, aka MalwareTech, the British security researcher who was credited with stopping the hard-hitting WannaCry ransomware worm that hit the UK’s NHS hard earlier this year, has been arrested in Las Vegas.
News that the 23-year-old, who found WannaCry’s hidden “kill switch”, had been detained by the US authorities as he attempted to return from the DEF CON hacking conference in Las Vegas came as a complete shock to the computer security industry.
In May, MalwareTech was portrayed as an “accidental hero” who determined that the WannaCry malware was connecting to an unregistered domain. He chose to register the domain, and WannaCry – fortuitously – stopped spreading.
MalwareTech received the praise of the National Cyber Security Centre (NCSC), part of the UK’s GCHQ intelligence agency, for his part in tackling WannaCry’s spread around the world.
The media went crazy, wanting to identify the young man who had saved the NHS, and it didn’t take long for them to name him as Marcus Hutchins, a young researcher based in South West England, working for a Los Angeles-based threat intelligence firm.
Hutchins made clear on social media that he was unhappy to be identified, seeming to prefer to work anonymously and arguing that his identity being made public could put him and loved ones in danger from the online criminals he worked against.
However, over time, Hutchins seems to have accepted that his fate – making multiple media appearances and seemingly growing to enjoy the spotlight and his new-found fame.
Now, Hutchins finds himself in the unwanted glare of the world again.
The Department of Justice has announced that it has charged Hutchins “for his role in creating and distributing the Kronos banking Trojan” – malware designed to drain online bank accounts.
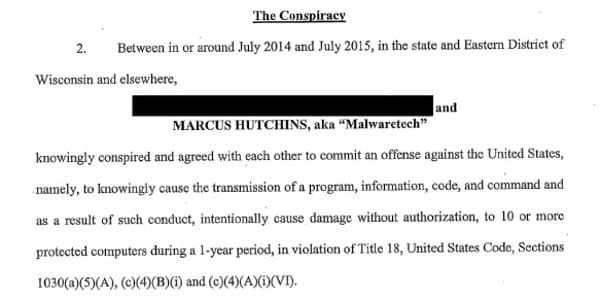
In the indictment, Hutchins is charged with one count of conspiracy to commit computer fraud and abuse, three counts of distributing and advertising an electronic communication interception device, one count of endeavouring to intercept electronic communications, and one count of attempting to access a computer without authorisation.
The six-count indictment against Hutchins was filed on July 12, 2017, but only made public upon his arrest as he was preparing to leave Las Vegas to return to the UK.
The charges relate to alleged conduct occurring between July 2014 and July 2015, and further charges appear to involve the activities of another (as yet unnamed) individual.
The FBI says that it has been investigating the Kronos malware case for the last two years, but things appear to have sped up recently with the shutdown of the dark web marketplace AlphaBay in early July, where Kronos was allegedly listed and sold.
Of course, it’s right to presume that Hutchins is innocent unless later proven guilty. There is lots of speculation taking place online, and some amateur sleuths are hunting for “evidence” to support their suspicions one way or another.
Regardless of whether you are guilty or innocent, being held by law enforcement in a foreign country must be a chilling experience for any young man and his family.
What I can say is that if Hutchins is innocent, there will undoubtedly be many questions asked as to how the FBI could have got things so wrong, and the risk that damage will be done to the relationship between the computer security community and law enforcement.
If, on the other hand, Hutchins is found to be guilty…
Well… it’ll be one of the largest falls from hero to zero that the cybersecurity industry has ever seen. And we’ll all question what on earth he was thinking when he got on that plane to the United States.



I'm firmly of the opinion the FBI/DOJ has massively cocked up. As we know, it's really difficult to confidently attribute malware to a part of the world, let alone an individual coder. I'd be surprised if the FBI got it right and I would love to see the evidence that they are basing this on. Nothing about his profile suggests he could be a blackhat – he has apparently given away a $10k bug bounty in the past. Why would he want to make money in such a risky way when he had a decent job working for the good guys and after the WannaCry publicity (wanted or not) an exemplary public profile in the industry? One of the more unusual stories in a while – I'm just waiting for John McAfee to come out and offer to defend him for free…
What if the U.S. Gov't is behind the crypto-malware attacks? It's not like the U.S. intel community hasn't sold crack in the getto to fund off the books operations. How many cryto-malware arrests have there been? There's been hundreds of millions, maybe more, paid in bitcoin an like no arrests. Oddly, U.S. Gov't agencies never seem to be impacted by crypto-malware.
I don't trust the U.S. Gov't and certainly don't trust the U.S. intel agencies.
Interesting points, perhaps bordering onto tinfoil hat territory for me but interesting nonetheless. I have no evidence either way for sure but it's a persuasive argument. I will say that the US Government and their various agencies have not *admitted* to being hit with crypto-malware. I don't know what US law would require them to disclose, but it seems to fall on the side of the Government/big industries more often that not. I bet they would hush it up and/or try to get the NSA to break the encryption if they could.
Can't see how you could make a blanket statement that all US federal agencies never seem to be impacted by crypto-malware. One example, the US federal Office of Personnel Management (OPM) had a very public breach and subsequent remediation assistance from Cylance. See:
https://www.cylance.com/en_us/about/news—press/congressional-report-concludes-cylanceprotect-played-a-pivotal-role-in-discovering-stopping-and-remediating-malware-that-caused-opm-data-breach.html
"if Hutchins is innocent, there will undoubtedly be many questions asked as to how the FBI could have got things so wrong"
Nah! The FBI are always getting things wrong (911), but their remit is such that they can never be legally liable. Like the CIA and the NSA, they can never be brought to justice, because they are answerable to no one. I suspect, if you were able to see the truth about these 3-letter agencies' activities, you would shudder in revulsion and wonder how on earth these organisations have come to wield so much power.
Revenues from drug importation and distribution have been declining recently, so domestic US intelligence agencies are increasingly turning to ransomware to make up the deficit in untraceable funding. They were no doubt none too happy with young Mr. Hutchins after he shut down WannaCry. They may ultimately let him go home with a good scare and a grossly enlarged sphincter, but this serves as an example of what happens when one doesn't fully account for the actual interests at play in so-called "organized crime".
Hang on – you're suggesting that US intelligence agencies wrote WannaCry?
Nice conspiracy theory, but I can't take it seriously.
Actually it's more their style to have lifted it from someone who will never talk because of being paid off, and/or threatened with imprisonment, or because of having a total lack of metabolic activity. Creativity is not a hallmark of government agencies.
If you said anything other than what you did, Graham, you might be silenced and none of us want that, I hope. Pragmatism is how we all get along, isn't it?
BTW, I really enjoy the podcasts – they are informative and great fun!
Thanks for saying you enjoy the podcasts. Listen carefully to the next one, as I’ll give you a wave. :)
Redacted copy of the charging documents is in the link below. It appears that the FBI is charging Marcus with creating Kronos, and with an unnamed defendant the advertising, selling, and ultimately receiving of profits from the sale of Kronos. The docs focus a lot on the other defendant, but fingers Marcus as the sole creator of Kronos.
http://docs.ismgcorp.com/files/images_articles/kronos-indictment-redacted11july2017.pdf
I'll wager serious money the redacted defendant has been offered a deal in exchange for fingering Hutchins. The common term for this kind of arrangement is "playing ball".
I'm sure this is the case, however, just saying it's Hutchins that was the mastermind doesn't count for much without evidence to support the claim.
There is, of course, a whole grey area between guilty and innocent, in which he did write some of the code that ended up being used in Kronos. He did complain once on Twitter that this has happened to some of his code (but didn't mention what malware it was). Moreover, writing malware itself isn't illegal (Rapid7 will be glad of that!), and I think the question here is if he wrote some code, did he knowingly do so to help cyber criminals (possibly in exchange for money)?
You can also be a hero while having done something stupid when you were young.