 Windows users are advised to be on their guard, after a new malware campaign was spammed out posing as an email from UPS.
Windows users are advised to be on their guard, after a new malware campaign was spammed out posing as an email from UPS.
Of course malware being distributed disguised as notifications from delivery firms like UPS, Fedex and DHL are nothing new – but that’s never going to stop criminals from using the technique to trick unsuspecting computer users into clicking on attachments.
After all, if it’s working for them why should they change their tactics?
Here is an example of a typical email that has been spammed out in the last 24 hours, with an infected Word Document attached.
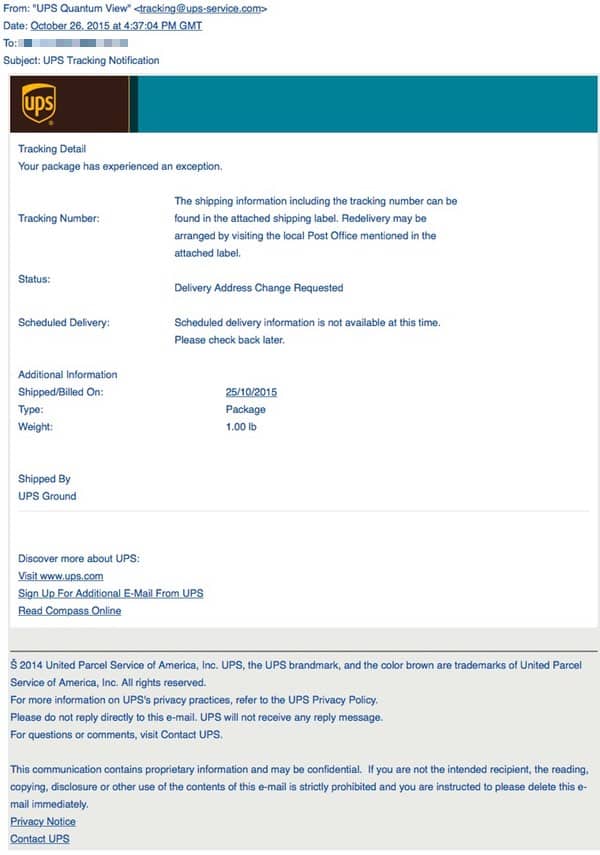
Part of the email, which has the subject line “UPS Tracking Notification”, reads in part:
Tracking Detail
Your package has experienced an exception.
Tracking Number:
The shipping information including the tracking number can be found in the attached shipping label. Redelivery may be arranged by visiting the local Post Office mentioned in the attached label.Status:
Delivery Address Change Requested
Simply receiving the email won’t infect your computer, but if you open the .DOC file attached then your system could be put at risk from a Trojan horse embedded as an OLE object, which in turn attempts to download further malicious code onto your PC.
Of course, you are more likely to fall for this social engineering trick if you regularly use UPS, or are expecting a parcel to be delivered. But even if you don’t, it’s easy to imagine how many people wouldn’t think twice about clicking on an attachment in what appears at first glance to be a legitimate communication.
The important thing is to learn to *always* be wary of opening unsolicited attachments, as they could be designed to infect your computer.
You can see what some security products are detecting the malware as in this VirusTotal report. Hopefully more products will be adding identification of the malware in the coming hours.


The real story here is why does Word, which is supposed to be a word processor, need features that can exploited like this? One of these days users will get over their infatuation with these geegaws and demand that software producers stick to basics. Only then will it be possible to lock this stuff down.
Hello, Graham. I also wrote a post this week based on the same subject I hope you will take the time to read it and leave a comment. Here is the link. Dan-L
http://jobsover50.ca/email-scams-and-hoaxes-past-present-and-future/
When I have a shred of doubt, I look at the headers.
It would be good if all logistic companies conform to a dual-factor notification, ie: email and SMS or boycott these mediums and use their own developed app.
Your email can easily be obtained by some dodgy mailing list or a breach out of your control. Your mobile no can also suffer from the same consequences.
However, to receive such Tracking notifications, which should entail a unique ID and consignment no: sent as a message to both your email/mob would be harder to spoof.