Thousands of Twitter users are finding that their accounts have been tweeting out malicious links without their permission, pointing to a fake anti-virus attack.
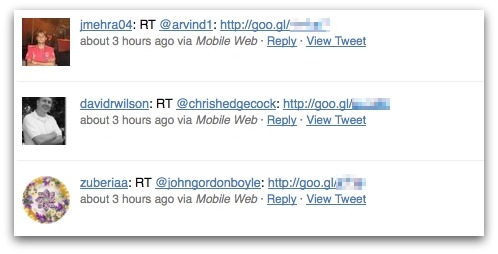
A quick search on the popular micro-blogging network finds many tweets from users containing no message other than a goo.gl shortened link (Google’s equivalent to bit.ly or tinyurl), which itself points to a URL ending with “m28sx.html”.
Although most affected Twitter users appear to be oblivious to what has occured, a few have noticed the messages, and suspected a security breach.

If you make the mistake of clicking on one of the malicious goo.gl links you are ultimately taken to a website which attempts to scare you into believing that you have a virus problem on your computer. You are then frightened into installing malicious code on your PC, and asked to pay money to disinfect your systems.
Sophos is adding detection of the malware as Troj/FakeAV-CMG. Sophos’s Live Protection technology has been protecting customers against the Ukranian URL hosting the malware since January 12th.
Interestingly, all of the offending Twitter messages examined by Sophos so far claim to have been posted by “Mobile Web” (Twitter’s “lite” interface for generic mobile phone users) rather than users’ normal clients such as Tweetdeck or Twitter for iPhone.
What isn’t yet clear is how the Twitter users found their accounts compromised in this way. The natural suspicion would be that their usernames and passwords have been stolen. It certainly would be a sensible precaution for users who have found their Twitter accounts unexpectedly posting goo.gl links to change their passwords immediately.
Remember, you should never use the same password on multiple websites.
Earlier this week Sophos published its 2011 Security Threat Report, revealing a sharp rise in the number of cybercriminal attacks taking place via social networks.
![]() Download the Sophos Security Threat Report 2011
Download the Sophos Security Threat Report 2011
Update: Del Harvey of Twitter’s security team has confirmed the problem, and reports that the site is removing the dangerous links and resetting the passwords of compromised accounts.
We're working to remove the malware links and reset passwords on compromised accounts.
— Del Harvey (@delbius) January 20, 2011

