A new report details how a D-Link webcam can be converted into a network backdoor, thereby highlighting general concerns with Internet of Things (IoT) devices.

In a blog post, Vectra Threat Labs explains that cracking an IoT device provides attackers with only so much benefit because IoT gadgets themselves tend to possess very little CPU and RAM.
That being said, attackers who instead want to use the devices to create a persistent network backdoor might be in luck, according to Vectra’s chief security officer Gunter Ollmann:
“Devices that can be easily attached to the network and remotely controlled or managed via the Internet tend to be soft targets. The design of circuit boards, chipsets, and the requirement for software updates combined in to a simple and environmentally reliable package limits design options. It doesn’t help that many of the popular ‘small footprint’ operating systems popularly used for mass-produced network devices are poorly secured themselves.”
In an effort to demonstrate viability of that threat vector, the Vectra Threat Labs team purchased a D-Link webcam for $30, cracked open the case, and used flashrom to dump the content. This process revealed a u-boot and a Linux kernel and image.
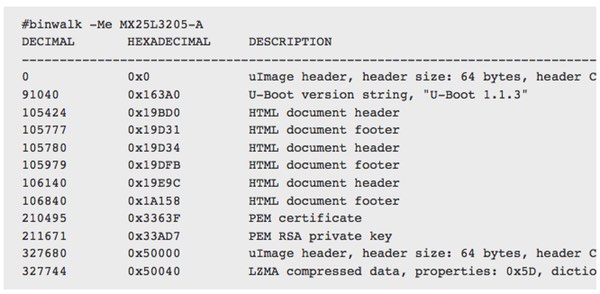
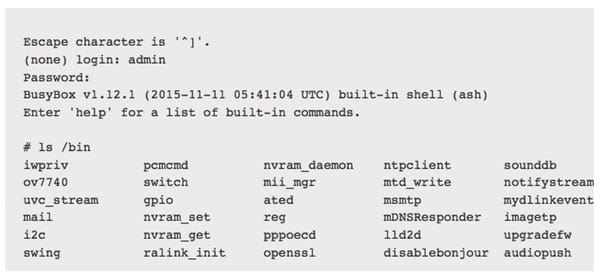
After analyzing the Linux image filesystem, the researchers came across /bin/upgradefw, which relies on a few checks to verify that the flash image is valid. The team ultimately used that binary to add a backdoor by adding an additional service to the Linux system. Here the team created a connect-back Socks proxy, which can be created via srelay and netcat in the startup script or a callback backdoor with a shell using netcat and busybox.
“Using the telnetd / busybox / netcat we can bring back a telnet socket to an outside host to have remote persistence to the webcam. With the webcam acting as a proxy, the attacker can now send control traffic into the network to advance his attack, and likewise use the webcam to siphon out stolen data.”
Ultimately, Vectra itself admits that the flaw does not constitute a major security issue with D-Link’s webcam. This in part might be attributed to the fact that an attacker requires physical access to the webcam according to Paco Hope, principal consultant with Cigital, in an interview with SCMagazine:
“It is clear that D-Link only anticipated trivial corruption of the software like a failing flash RAM storage part or corruption on the network – it did not anticipate malicious software inserted either directly through a physical attack or through man-in-the-middle attacks over the internet. Putting persistent malware into a device when one has physical access to it is not novel or remarkable. The fact that our ecosystems are full of so many easily compromised devices and we have no idea which ones are trustworthy is the key problem.”
Going forward, Hope recommends that organizations isolate devices like D-Link webcams and the EZCast TV streamer, which was recently cracked itself by Check Point researchers, on their own dedicated network segments.
In the meantime, researchers need to continue to raise awareness about IoT security weaknesses so that manufacturers and developers begin to incorporate security into the design stage of their devices.


'In a blog post, Vectra Threat Labs explains that cracking an IoT device provides attackers with only so much benefit because IoT gadgets themselves tend to possess very little CPU and RAM.'
Understand I'm exhausted and can barely keep my eyes open (and won't be here long as such) but when I read 'cracking' and then 'IoT' my tired head transposed 'cracking' to 'crack' and 'IoT' to 'pot' and therefore crackpot (albeit as two words instead of one; whether that is a pot full of crack or a crackpot is up to what your habits are)… Who the crackpot would be I don't know because that's all I could process at the time. Of course, one could argue that I'm a crackpot but that's another story entirely.
I most certainly will not be doing anything requiring thinking (which in practise means I won't be doing anything …) at all for a while. At least I still have my sense of humour.