Vulnerability broker Zerodium says it is now offering up to $2.5 million for zero-day remote exploits which would allow attackers to infect a remote Android smartphone with malware, with no user interaction required.
Zerodium is not offering the considerable reward because it wants to make the Android operating system a safer environment. Instead it believes it can make a handsome profit by selling such an exploit to the likes of intelligence agencies and law enforcement bodies.
Whereas the likes of Apple, Google, and Microsoft offer bug bounties for details of vulnerabilities in their software and then work on improving their code to protect their userbase, Zerodium offers ways to crack into devices to whoever is prepared to stump up the cash.
I suspect that the majority of Zerodium’s customers are not software manufacturers, but governments and intelligence agencies who use use the zero-day exploits to spy on suspected criminals, terrorists, persons of interest, and foreign nations.
And those types of customers have a vested interested in the likes of Apple, Microsoft, and Google not patching the bugs. After all, once a zero-day vulnerability is fixed its value reduces considerably.
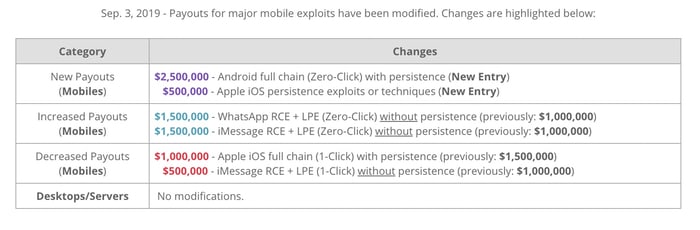
What I find interesting is that Zerodium’s offer up to $2.5 million for a “full chain (Zero-Click) with persistence” exploit is actually greater than the equivalent no user interaction exploit for iOS (for which a paltry $2 million is offered).
In fact, citing “market trends”, the controversial vulnerability broker has actually decreased some of its payouts for iOS exploits. For instance, the maximum an iOS full chain exploit that provides persistence and requires only one click from the victim is now worth up to $1 million, rather than the previous $1.5 million.
Thankfully, not all vulnerability researchers are purely driven by maximising the amount of money they can make from their discovery. Many feel passionately about the importance of privacy, and would be revolted by the thought that an oppressive government could use it to spy upon its citizens
We only have Zerodium’s word for it that they would ever give such a large amount of money to someone who came up with a way of remotely compromising a fully-patched Android device without the user having to make a single click. But it’s hard not to believe that there are plenty of governments and intelligence agencies who would pay handsomely for just such a tool.
Further reading: There’s an interesting thread on Twitter by The Grugq as to why he believes Android exploits are commanding higher prices than those for iOS.