Remember the Heartbleed and POODLE vulnerabilities that were found in the OpenSSL cryptographic library back in 2014? Well, a serious new vulnerability has been uncovered that strikes at the very heart of encryption, and help attackers steal confidential information.
And, it is estimated, that 33% of all HTTPS servers are at risk.
The first hints that there was a serious problem in OpenSSL arose last week, when advance notice was given that a couple of high severity bugs would be patched today.
At the time, details of the nature of the security problem fixed by the new version of OpenSSL was shrouded in mystery but now, thanks to drownattack.com, we know.
DROWN stands for Decrypting RSA using Obsolete and Weakened eNcryption, and it provides a way for attackers to decrypt HTTPS communications from servers that are still supporting SSLv2.
The problem is that many sysadmins did not think that still supporting the outdated SSLv2 protocol on their servers was a problem, because modern client software simply didn’t use it.
But it seems the mere existence of SSLv2 could help attackers to crack a connection’s encryption, and initiate what is effectively a man-in-the-middle attack.
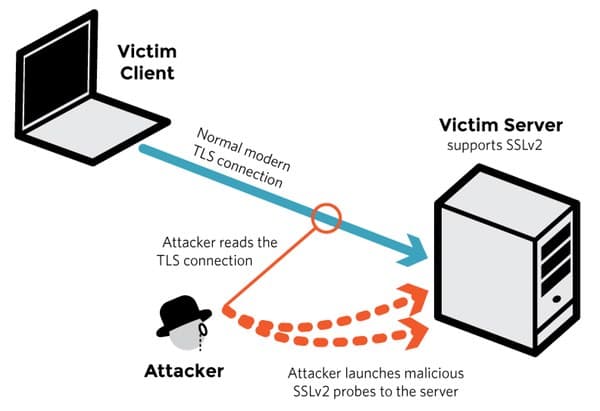
According to the researchers, a server is vulnerable to the DROWN vulnerability (also known as CVE-2016-0800) if:
- It allows SSLv2 connections. This is surprisingly common, due to misconfiguration and inappropriate default settings. Our measurements show that 17% of HTTPS servers still allow SSLv2 connections.
or:
- Its private key is used on any other server that allows SSLv2 connections, even for another protocol. Many companies reuse the same certificate and key on their web and email servers, for instance. In this case, if the email server supports SSLv2 and the web server does not, an attacker can take advantage of the email server to break TLS connections to the web server. When taking key reuse into account, an additional 16% of HTTPS servers are vulnerable, putting 33% of HTTPS servers at risk.
The researchers – who have published a detailed technical paper and a more digestible FAQ – say that they have been able to execute a special form of the DROWN attack in under a minute on a single PC.

Now that details of the attack are public it wouldn’t be a surprise if malicious actors attempt to exploit it in the wild. No doubt there will also be some security researchers who will be curious to experiment with it too…
The bad news for users is that there is nothing they should be doing to expedite a fix, other than put pressure on companies (the DROWN attack page lists major sites that are vulnerable such as Yahoo, BuzzFeed, Flickr, Samsung, Alibaba and Weibo) that they should disable SSLv2, and ensure that private keys are not used anywhere with server software that allows SSLv2 connections.
If you want to check whether a particular site is vulnerable, the researchers have helpfully provided an online tool.
For further information, check out the DROWN attack webpage or consult the good write-up by cryptographer Matthew Green.
This article originally appeared on the HEAT Security blog.