 Earlier today I reported how users of file sync and share services like Dropbox and Box.com could have their sensitive information exposed to Google advertisers.
Earlier today I reported how users of file sync and share services like Dropbox and Box.com could have their sensitive information exposed to Google advertisers.
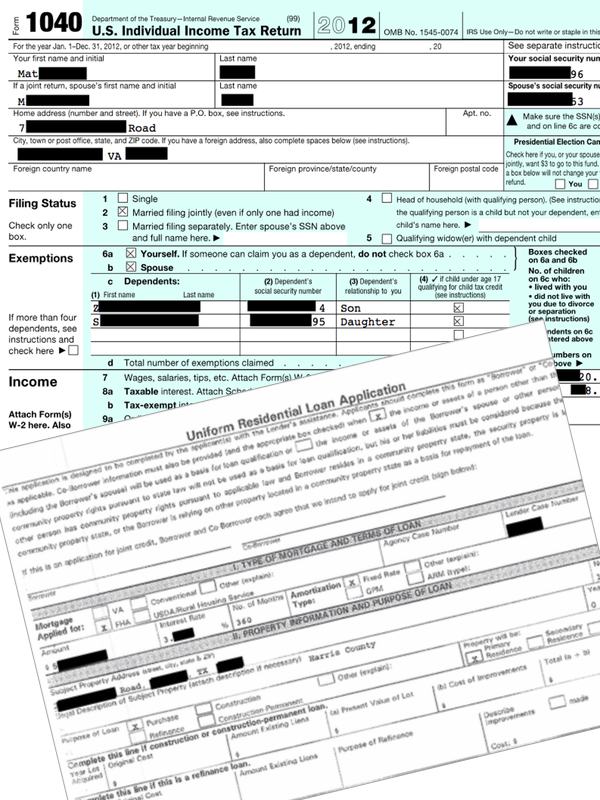
Dropbox was contacted yesterday by the media, investigating the claims being made by Intralinks – a file sharing and collaboration service for enterprises – after it revealed that it had stumbled across individuals’ mortgage applications and income tax returns that should surely have remained private on Dropbox.
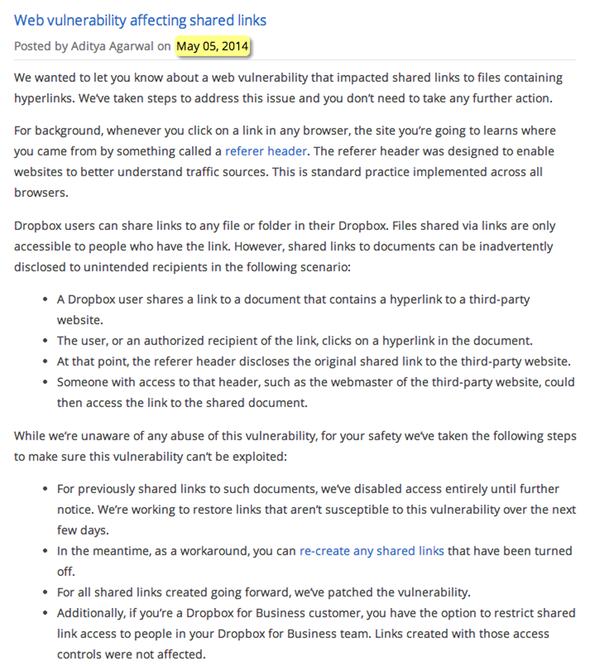
Dropbox responded last night with a blog post saying it was addressing the vulnerability and that it was “unaware of any abuse of this vulnerability”.
Well, clearly – despite Dropbox’s protestations – users’s data *was* exposed, otherwise files like this and this wouldn’t have fallen into the hands of unauthorised parties.
But what worries me most is this.
Intralinks tells me that it privately informed Dropbox that data was being leaked via the shared link vulnerability in late November 2013. That’s over five months ago.
At the time, this was the response that Dropbox offered:
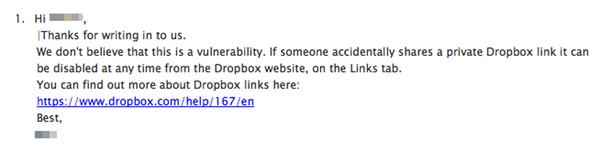
Thanks for writing in to us.
We don’t believe that this is a vulnerability. If someone accidentally shares a private Dropbox link it can be disabled at any time from the Dropbox website, on the Links tab.
For months, nothing happened.
In short, Dropbox dropped the ball.
It was only when Intralinks decided internet users needed to be warned of the potential risks, and got in touch with me and BBC News, that Dropbox stirred into action.
Here is the blog post that Dropbox published last night:
Even then, Dropbox are only responding to the hyperlink disclosure vulnerability, *not* the Google Adwords-related issue I describe in my blog post.
I think it’s a pretty sad state of affairs that months can pass, and the BBC has to be called in, before a service like Dropbox takes seriously a security concern impacting the privacy of its users.
PS. Meanwhile, has anybody heard any comment at all from Box.com who were affected by similar issues? I mean, at least Dropbox said and did *something*.
(Although in fairness to Box.com, at least their free version offers the option of more secure sharing than Dropbox’s free edition allows.)
Further reading:
- Your Sensitive Information Could Be at Risk: File Sync and Share Security Issue
- Dropbox users leak tax returns, mortgage applications and more


Dropbox is a consumer service that's largely free. Users of free services are showing less and less interest in privacy and security, of course those same users are also loading up their quotas with corporate and confidential data. So, can you blame dropbox for not really caring about what its users care so little about? To the average dropbox user, this data leak is complicated and difficult to understand and their in their minds its something only an elite hacker could pull off.
There is nothing to 'pull off'.
IF you paste a secret thing in the google search, OF COURSE this gets logged.
Its the same 'vulnerability' when someone sends an email to the wrong person.
Regarding the Referrer thing – I have seen links to much worse places in the Referer – private internal business systems and stuff. Some of which actually can be opened too. For many years now.
This is just some competitor of Dropbox screaming that the sky is falling about things that people who do care about this have known for 15 years.
The 'Google Adwords-related issue' isn't a vulnerability in Dropbox; it's the user's fault for publicly sharing a private link.
Other services require users to authenticate themselves before accessing shared links. Why not Dropbox?
That would make sharing more complicated for a service which appears to be designed as a quick way of sharing material rather than a secure method of transferring documents. Dropbox could make this more prominent on their website rather than hiding the warning at the bottom of the page in the "For our advanced users" section. https://www.dropbox.com/help/167/en