
Domino’s has fixed a security issue in its Android app that hackers could have exploited to order free pizza.
Paul Price, a security consultant from the United Kingdom, first came across the bug while playing around with Domino’s Android app. Price is familiar with Domino’s ordering process, and he wanted to see how the app randomly generates a £10 voucher code on certain orders.
What Price found instead made the voucher code utterly meaningless.
“After sifting through the app’s source code I notice that the code is generated server side via an API call. I fire up a proxy (Burp) to monitor the web traffic between my phone and the Domino’s API server and run through the order process. Something immediately catches my eye… The Domino’s app itself was processing payments client side via a payment gateway.”
Generally, payments are processed on the server side to prevent bad actors from manipulating the specific parameters of a transaction. Payments can be processed on the client side, but they must be done so correctly.
That was not the case with Domino’s app.
When Price tried to place an order with a fake Visa credit card number, Domino’s denied the order. However, it did return the following response via its payment gateway, which is known as DashCash:

Using that response as reference, Price changed the <reason> attribute to “1” and the <status> attribute value to “ACCEPTED,” which signifies to DataCash that the transaction has been successfully completed.
This time, Price’s order went through without a hitch.
![]()
He called Domino’s to confirm his order. Sure enough, they said they were preparing his pizza and that it would be delivered in 20 minutes.
Fortunately, Price is an honest guy.
“The pizza arrives and I tell the delivery driver there must of been a mistake with the order as I never entered any card details and wanted to pay with cash. He happily leaves with £26 and my conscience is clean.”
This isn’t the first security issue the famed pizza maker has come across.
Back in March of 2009, Domino’s offered up 11,000 pizzas to customers at no cost due to a website glitch.
More recently, in 2014, the chain refused to pay a ransom fee of US $40,000 after attackers made off with nearly 650,000 customers’ records.
The pizza chain has confirmed that it patched the bug discovered by Price relatively quickly.
Looking ahead, we can only hope that companies will follow Domino’s example by accepting responsibility for flaws such as these and by issuing a fix without too much of a delay.



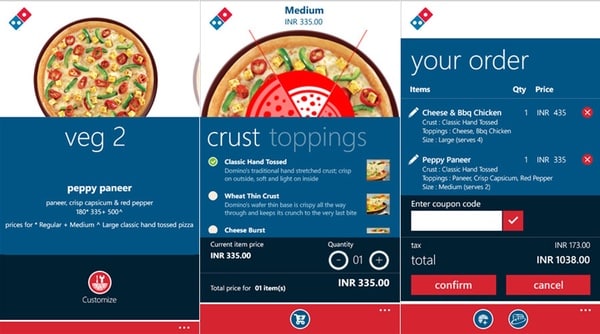
Why the interface is look like windows phone instead of android app?
' … was processing payments client side …'
You know what this really comes down to? Not sanitising user input. Even if a developer has never heard of this concept it should be obvious. Perhaps it is so obvious that many people miss it?
"must of been" must have been a mistake the copy editors missed.