In November 2011, it was announced that “Operation Ghost Click”, a two-year joint investigation by the FBI and Estonian law enforcement, had resulted in the arrest and charging of six Estonian men and one Russian.
In November 2011, it was announced that “Operation Ghost Click”, a two-year joint investigation by the FBI and Estonian law enforcement, had resulted in the arrest and charging of six Estonian men and one Russian.
The men were charged in connection with DNS Changer – a sophisticated money-making malware campaign that had recruited over four million computers in approximately 100 countries into a botnet.
The Estonian men were arrested and taken into custody by the Estonian Police, while the United States sought their extradition.
In subsequent hearings, prosecutors claimed that the gang earned $24.2 million through criminal activities, and that a Seychelles-registered company operated by alleged mastermind Vladimir Tsastsin received at least $16.37 million.
Tsastsin has had something of a history with organised crime, having previously been found guilty of credit card fraud, document forgery, and money laundering, as detailed by this Washington Post article by Brian Krebs from 2008.
Today, over two years later, an Estonian court has acquitted four of the men – including Tsastsin – saying that the charges against them have not been proven.
The problem appears to have been the lack of specific victims produced by prosecutors.
There were smiles on the faces of Tsatstin, Timur Geraassimenko, Dmitri Jegorov and Konstantin Poltev, as they were told of the court’s decision at the Harju County Court in Estonia.

For now the men remain remanded by the Estonian authorities, while a decision is made as to if they should be extradited to America to face prosecutors there.
Two others who were arrested back in 2011, Anton Ivanov and Valeri Aleksejev, have already been extradited to the United States, and are going through the legal process there.
What was DNS Changer?
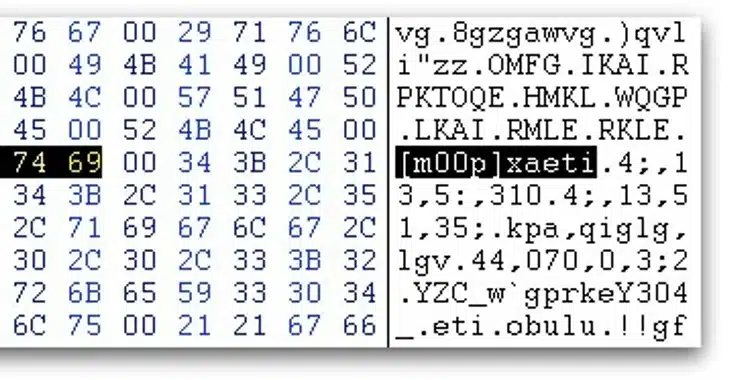
Operating under the company name “Rove Digital”, the cybercriminals behind the DNS Changer click fraud malware campaign used a collection of rogue DNS servers to display alternative adverts and redirect millions of infected PCs and Macs to unconnected webpages, earning them money in the process. In addition, the malware attempted to block attempts by users to update their anti-virus software.
Affected computers included ones belonging to individual, business and government agencies such as NASA.
The FBI ultimately seized control of the rogue servers and made them safe, and launched a public awareness campaign to encourage affected users to check if their DNS settings had been meddled with and – if so – fix them.