Attendees to the 25th annual DEF CON hacking conference discovered weak spots in electronic voting machines that attackers could abuse in future compromises.
For their first-ever Voting Machine Hacking Village, DEF CON’s organizers purchased 30 electronic voting machines off eBay and left them to the mercy of attendees’ hacking skills. Not all of the computer-powered ballot boxes still service voters in today’s U.S. elections. But some do.
That makes the outcome of the Hacking Village all the more concerning.
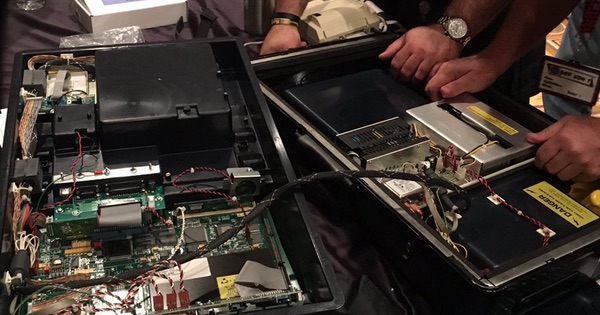
Within 90 minutes, security researchers began uncovering chinks in the machines’ armor. Some physically broke into the machines with screwdrivers and discovered ports that attackers could leverage to infect the machines with malware. Others searched for admin passwords on Google to see what hidden features they could unlock. One even Rick-Rolled their target machine.
The WinVote is now the newest music playing device in the village! #DEFCON #votingvillage pic.twitter.com/litn3YhaOX
— DEF CON VotingVillage (@VotingVillageDC) July 29, 2017
Perhaps the most significant intrusion came from security researcher Carsten Schurmann, who obtained remote access via RDP to a WinVote machine by exploiting the unit’s poor Wi-Fi security along with a Microsoft vulnerability.
https://twitter.com/bobmcmillan/status/891020884688764928
Jeff Braun, who specializes in digital security in Washington DC, told The Register that the Hacking Village’s results point to important shortcomings in the United States’ voting infrastructure:
“Without question, our voting systems are weak and susceptible. Thanks to the contributions of the hacker community today, we’ve uncovered even more about exactly how. The scary thing is we also know that our foreign adversaries – including Russia, North Korea, Iran – possess the capabilities to hack them too, in the process undermining principles of democracy and threatening our national security.”
Still, not everything is doom and gloom.
According to CyberScout’s Eric Hodge, counties can avoid many physical threats posed to electronic ballot boxes if they “store machines, set them up, [and] always have someone keeping an eye on machines,” reports The Hill.
As for over-the-air vulnerabilities, DEF CON is seeking to set up an entire voting network at its next conference to determine if, for example, a remote hacker can abuse a flaw to change votes. (Those in attendance at DEF CON 25 didn’t succeed in achieving this level of interference.) They can then report those vulnerabilities to the Federal Election Commission and/or to individual states, who will hopefully take the flaws to heart and use them to better secure voting machines.
The United States doesn’t need a repeat of its 2016 election. It needs better voting machine security. And it looks like DEF CON attendees are leading the way in bringing about that change.



Basically this story proves nothing. There were a small number of machines that "Possibly" could be affected, but only if the machines were left alone after set up, and everyone put on blindfolds.
Considering there is ZERO evidence any voting machines were compromised in 2016, this and many other articles are tabloid fodder. A false narrative, by leftist who refuse accept the election outcome this past Nov.
Furthermore, the only funny business was actually perpetrated by leftist election Official's who have in many cases been prosecuted already. Not to mention the many Case's of people voting illegally. And yes, I can offer proof. It's not hard. But leftist prefer to denied reality by acting like the three monkeys.
I was with you till this …
The United States doesn't need a repeat of its 2016 election.
Voted for Clinton did we?
This would have more than marginal significance if:
1. the machines were current issue and maintained to current firmware and software levels. The security of used equipment from eBay says little about current equipment.
2. There were successful hacks on equipment with no WiFi or with WiFi disabled and all access doors locked and covered with undamaged tamper evident seals.
Diebold Accuvote TSX machines used in Ohio ca. 2002 – 2008 were deployed that way. Only power and headphone sockets were exposed during election operations. That left open the possibility for corrupt manipulation before voting officials opened the machines for use, including by election officials. Consequently, a good deal depended on election process controls and county board of election officials – as is the case with every election system, whether it uses machines or not. The paper by Feldman, Halterman, and Felton ("Security Analysis of the Diebold AccuVote-TS Voting Machine"), available at https://www.usenix.org/legacy/events/evt07/tech/full_papers/feldman/feldman_html/index.html, discusses the security of these machines, and its considerable faults, in detail.
The problem with all these machines, as well as Internet voting, is that they claim to be solutions to a largely nonexistent problem. In fact, the only problem they solve is the one the broadcast newsreaders have if election results are not available for the 10 PM news show. These systems make the election less transparent, by interposing "magic" between voters and ballots and between ballots and their tallying, makes the overall process less trustworthy. As a result, they increase the credibility of those who cry out about fraudulent elections, and by doing so undermine acceptance of democratically elected officials.
The solution is not to improve them but to dismiss them entirely, accepting that that will delay results by enough that they won't make the 10 PM news and may even not make the morning papers; both may have to find other news to report.