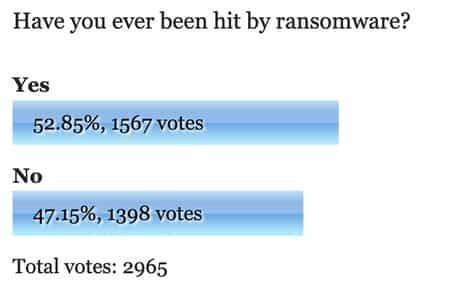
 Boffins at security firm Bromium have discovered that the CryptoDefense malware has been spread via boobytrapped webpages, in an attempt to make more money for its creators.
Boffins at security firm Bromium have discovered that the CryptoDefense malware has been spread via boobytrapped webpages, in an attempt to make more money for its creators.
CryptoDefense is less well-known than its fellow ransomware CryptoLocker, but is no less unpleasant – encrypting documents, source code and SSL certificates on victim’s computers and demanding that a Bitcoin ransom be paid in order to recover the data being held hostage.
The first most users know that they have a problem is when they find a file on their Windows desktop called HOW_TO_DECRYPT:

All files including videos, photos and documents on your computer are encrypted by CryptoDefense Software.
Encryption was produced using a unique public key RSA-20148 generated for this computer. To decrypt files you need to obtain the private key.
The single copy of the private key, which will allow you to decrypt the files, located on a secret server on the internet; the server will destroy the key after a month. After that, nobody and never will be able to restore files.
In order to decrypt the files, open your personal page on the site [URL LINK] and follow the instructions.
Visiting the link contained in the message takes you to a webpage that encourages you to pay up (once you have defeated the CAPTCHA test):

But, if you dawdle and don’t cough up enough Bitcoins in time – you might find the price has gone up:

I can’t encourage you to pay the criminals if you are unlucky enough to be hit by this malware. After all, you are only encouraging them to launch future attacks and there’s no guarantee that they will actually give you access back to your files, rather than raise their ransom demand even further.
If you were sensible enough to have a secure, uncompromised backup of your important data then you might be wiser to wipe your computer clean and restore from that.
According to Bromium’s researchers, the ransomware is being distributed by attackers via Java drive-by downloads.
What that means is that the gang behind CryptoDefense are trying to increase their potential pool of victims by not just spamming out their malware as email attachments, but also planting malicious code on websites to exploit vulnerabilities in Java in order to silently infect visiting computers.
For a detailed analysis of CryptoDefense and its methods of infection, check out Bromium’s blog post on the subject.
 Once again, as if you needed another reason, CryptoDefense reminds you that it’s worth considering whether you really *need* Java on your computer.
Once again, as if you needed another reason, CryptoDefense reminds you that it’s worth considering whether you really *need* Java on your computer.
The truth is that cybercriminals love Java. Java is multi-platform, which means it can be run on different computers, regardless of their operating system. Because of this, it’s not unusual to see attackers use Java as part of their attack before serving up an OS-specific payload.
So, here are your options:
1) If you still *really* need Java, apply all available security patches as soon as you can.
2) Deinstall Java entirely. Chances are that if you don’t think that you need Java, you don’t need it.
3) The half-way house. Turn off Java in your web browser, thus prevent the most common vector for Java-based malware attacks. There is an article on the Naked Security website explaining how to do this for the most popular browsers. Of course, if you go this route you should still apply any Java security updates.
Depending on where you work, options 2 and 3 may be difficult for you to follow. A sizeable number of businesses still rely on archaic code which requires Java to properly work. If that’s the case for you, it may be best to have a different browser for surfing the web than the one you need to run that creaky old Java-based app that your IT team wrote in 2003.
Java is getting a bad name for security, so it’s no surprise that more and more people are keen to permanently remove it off their computers rather than risk being hit by a malware attack.
Earlier this year, Bromium discovered that hackers were infecting computers as unsuspecting users were watching YouTube videos – again via a Java exploit.
Get the message?
You’re crazy to use Java. Crazier not to patch it.
Does your workplace require you to have Java installed? Leave a comment below and tell us what you think about still using Java in 2014…


Hey Graham. Yes, our workplace requires we have java. One of the applications is our time keeping software. We are actually forced to use the version 6 flavor because we haven't updated to it's latest version as of yet. But we do have plans to do this in the coming months. So we can only use what our third party vendors support when it's a java dependent software unfortunately.
EMET5.0 technical preview from Microsoft gives you options to limit Java plug-in execution to specific zones. To quote Microsoft "… you can configure EMET to prevent Microsoft Word from loading the Adobe Flash Player plug-in, or, with the support of security zones, you can use EMET to prevent Internet Explorer from loading the Java plug-in on an Internet Zone website while continuing to allow Java on Intranet Zone websites." If they iron out the bugs (my limited testing found it EMET caused a lot more weird behaviour / crashes on shutdown etc than EMET 4) – but this could be a useful option for corporates who need to run java for internal applications.
If you use Bromium you don't have to patch…or at least don't have to rush to patch. Br isolates all execution when visiting internet sites that may or may not contain exploits including Java exploits. Any exploit simply infects a micro virtual machine and is discarded as soon as the user closes the page or changes sites. Very cool.
I wonder what this world would be like if other professions had to endure the sabotage of their tools like those of us in the IT industry.
It would be … ehm, is it actually possible ? I would hope not but yet the cynic in me has always shown to be correct… One can hope that I'm wrong here. Either way, I guess another problem with IT is that CEOs and those who make decisions are beyond ignorant with security (and computing in general).
A long time friend of mine and I were joking about this with regular expressions, not too long ago. Basically, the idea is that CEO (and those making decisions) want to replace server with "the cloud" (which to me is a stupid notion in the beginning: server farms, among other things) and then expect it to be owned, configured and secured in the same way (we were just communicating it via regular expressions). That's only one example. And that's not even considering budget. It's scary when it risks not just the company's assets, its customers but also the entire world!
As for Java, it is unfortunate, the problems it has. The cross-platform is a blessing but also a curse. Used properly it is fine but abuse is always going to be there (and that's just like the Internet: never designed with security in mind + not foreseeing things [nothing is perfect] and hence revisions, obsoleting RFCs, etc.).
I would suggest the single, most significant reason that Java is so capable of these types of things (causing security problems) is it has a huge API covering so many things (graphics, {de,}serialisation, networking – servers included, multithreading, random numbers, …) combined with the cross platform capability (through virtualisation). That's also a blessing and a curse.
Lastly, it is even more unfortunate that Oracle took over Sun Microsystems. Because sure, Sun was not perfect (what company is?) but Oracle has a much worse record and it shows: they take the rights to Java, update old source code to refer to Oracle owning it with no reference to Sun (which to me is disgraceful… at least give the proper credit to the original authors, even if you must add to it that it now is owned by Oracle) and then – this even worse as hard as it is to fathom – go after companies that use its once open API (referring to Google and.. Android [?]). I have no idea how open it is now but all of Oracle's stunts are rather shameful. I still hope to …. that they did not touch Solaris. But I suspect largely they have and having fond memories of it, I cannot get myself to check, out of the fear of that I am right (I probably am and I wish I wasn't). I had to check for some reason. Indeed, rest in peace, SunOS and Solaris…
Thanks for the update Graham. Is the latest version of Java 7 patched against this attack?
Probably but it doesn't matter…another attack is right behind it. The java attack surface is so vast, ever changing and used by virtually everyone the bad guys will forever have a field day.
Our company too relies heavily on Java as our clients use it prolifically. Why, may I ask, to anyone that might know, is Java still being used? Are there alternatives that could be suggested, or is Java so "embedded" in the code in cyberspace that there's no "going back" or "moving along"?
Best Regards All,
AJ Lebeau
Network Administrator
JAVA = Just Another Virus Application… java has always been sieveware, calling it crap is mean to crap, it is just one of many lousy tools used by inept programmers.
Java is easy to secure, never install the sieveware in the first place.
I am a novice. If I don't have java I can't see half of the videos on the www. Is there an alternative?
Are you sure you don't mean JavaScript rather than Java?
Java and JavaScript are not the same thing. Yes, it's dumb that they have such similar names…