 The most common passwords revealed in the notorious Ashley Madison hack are generally consistent with non-cheating users’ weak password security.
The most common passwords revealed in the notorious Ashley Madison hack are generally consistent with non-cheating users’ weak password security.
Last week, a password-cracking group known as CynoSure Prime published a blog post in which it revealed that it had successfully cracked 11.2 million Ashley Madison’s users’ passwords and that it could break an additional 4 million.
The group explains that it was able to crack the bcrypt hashes used to protect the users’ passwords via a roundabout method: attacking Ashley Madison’s insecure implementation of the MD5 cryptographic hash function, which included the storing of passwords within the hashes themselves.
Keith Collins of Quartz has since had an opportunity to examine the work of CynoSure Prime.
Of the 11.2 million passwords leaked online, the most common choice among them was “123456” at over 120,000 individual users. Some of the other most common permutations included “12345”, “password”, “DEFAULT”, “qwerty”, and “abc123”.
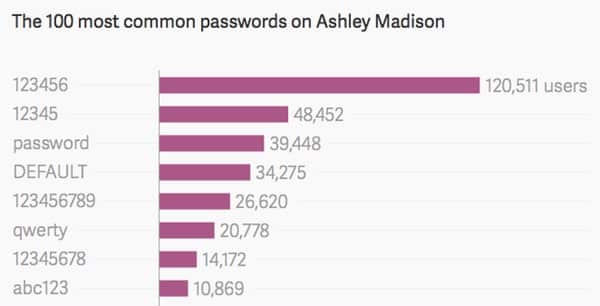
These leaked passwords are for the most part consistent with SplashData’s list of the most common passwords for 2014.
In that compilation of some 3.3 million passwords that were posted online by hackers, “123456” and “password” held the first and second spots, respectively. These were followed by the likes of “12345”, “12345678”, “qwerty”, “baseball”, “football”, and “dragon”.
Unfortunately, those password choices are not unique for 2014.
According to an article published by the Wall Street Journal, those passwords have been in preferred circulation among users for the past couple of years despite the growing number of high-profile hacks and data breaches.
Since at least 2011, “123456” and “password” have held the first and second spots, whereas others such as “111111” and “dragon” have consistently held places in the top 10.
Given the persistence of these permutations, it would appear that online users, including those wishing to pursue an affair, have been putting themselves at risk for years by continuing to choose weak, easily guessable passwords.
“Psswords based on simple patterns on your keyboard remain popular despite how weak they are,” Morgan Slain, CEO of SplashData, told PRWeb. “Any password using numbers alone should be avoided, especially sequences. As more websites require stronger passwords or combinations of letters and numbers, longer keyboard patterns are becoming common passwords, and they are still not secure.”
Given the nature in which threats are evolving in today’s insecure world, it would behoove users to consider using a Password Manager such as LastPass, 1Password, KeePass or Dashlane that can automatically generate and remember strong passwords for their online accounts.
Further reading:- Ashley Madison's leaked database available for download - read this first
- Ashley Madison blackmailers now sending threats via US postal system
- Here's what an Ashley Madison blackmail letter looks like
- Now it's Ashley Madison wives who are receiving blackmail letters
- 'Bring me the head of the AC/DC-loving Ashley Madison hacker'
- Suicide and Ashley Madison
- Ashley Madison: Betting site offers odds on who will be exposed
- 'Yes. I was a member of the Ashley Madison website. But I wasn’t there to cheat on anyone'
- Ashley Madison hack could expose 37 million 'cheating dirtbags'
- No Ashley Madison, you weren't burgled by terrorists
- Ashley Madison users warned of password risk
- Cracked Ashley Madison passwords consistent with years of poor security
- Post-hack, Ashley Madison offers members full and free account deletion
- Don't judge Ashley Madison users too quickly, their accounts may be fake
- Just who is joining the Ashley Madison website?
- Fembots land Ashley Madison in hot water with the FTC
- Ashley Madison's marketing department clearly didn't get the memo
- Ashley Madison: Further thoughts on its aftermath
- Ashley Madison hack claims another victim: Its CEO
- Ashley Madison slammed with $1.6 million fine for devastating data breach


Why was salting passwords such a foreign concept to these clowns?