I’ve received an email, apparently from a PR agency based in San Francisco.
The PR agency is real, with real clients, and real offices.
But the email is bogus.
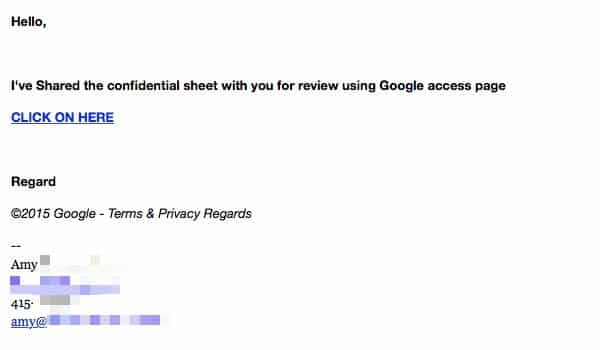
Hello,
I’ve Shared the confidential sheet with you for review using Google access page
CLICK ON HERE
Regard
©2015 Google – Terms & Privacy Regards
I’ve obscured the PR agency’s name and contact details to protect the innocent, because I’m fairly sure that they weren’t responsible for sending it.
Would you click on the link?
I guess the bad guys behind this particular attack give the game away a little by making such a poor job of their grammar, but there’s no doubt that some people will be so intrigued by the idea of a “confidential sheet” that they will click first and think later.
But if you took a second to hover your mouse, over the clickable link in the email you would find that it doesn’t really take you to a file on Google Drive, but instead to a phishing page designed to steal your credentials.
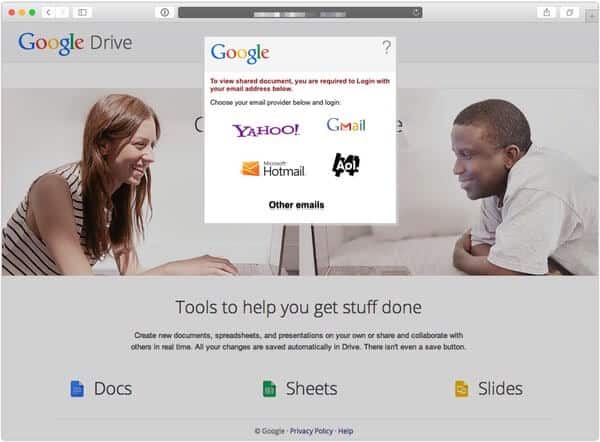
And not just your Google username and password. Oh no, these guys would quite like it if you handed over your AOL, Hotmail (don’t they know it’s called Outlook now?), or Yahoo password too.
Always take care about what you click on. It might be someone trying to steal your passwords.



It seems that yes, I would click on it. How else could I respond here? Of course, it is probable (slight suspicion) that 'this' is the mail that you refer to in this post. In which case, I can't say I would click on it.
Now that I've pointed that out (some would find the above stupid, absurd and any number of other negative things but being able to find amusement in everything does make things so much more enjoyable), I'll just say that yes some would click on it. I don't know why though, aside from being woefully naive. I wouldn't be surprised (though I have no evidence to confirm one way or another) if the poor grammar and spelling doesn't actually harm their scheme (maybe it intrigues some people?). Certainly some would continue with it, just like some inadvertently help someone steal their identity.
I'd probably click on the link precisely to see the scam inside. Best I can figure, nothing can happen if you're fully aware of how phishing scams work. As long as you don't proceed any further, you're safe. Even if it hides a downloadable executable, you still have to run it to get infected.
I had the same problem from the opposite angle the other day – an entirely genuine email from a household-name company I pay an annual service subscription to, which I sat and looked at for several minutes, thinking it was spam. It was sent from a generic company address ( sort of thing), had a subject header along the lines of "Important information about your account", and the text of the email was "Please open the attached PDF to read an important announcement about your service." It turned out to be entirely genuine, but for a company that not only communicates with me online but holds payment details and personal data on me to send out genuine mails that appeared to have been almost deliberately designed to make you think it was spam seems indefensible in this day and age. The recipient certainly needs to be careful, and clicking without thinking is always a recipe for disaster: but it would be easier to spot the scams if companies would take a bit more thought and care about the emails they send to their customers/contacts.
Whenever in doubt, I immediately look at the headers to see where an email originated from, specially when I'm not expecting any correspondences from companies/organisations I'm affiliated with.
Hypothetically if 10000 phishing emails are distributed, a good sum that receive it are likely to follow the white rabbit and land themselves in trouble.
That’s what the scammers aim for, the carelessness or misunderstanding of these few so they can prey on.
No, I wouldn't fall for it. The following red flags don't make it through my mental filters:
1. I don't know the sender. (I probably wouldn't even open the message.)
2. The article doesn't mention the subject line of the email, but that's also a key indicator. If it said anything about a "confidential sheet", or any other suspicious freebee, I probably would label it junk without opening it.
3. Even if I opened it, it says "Hello". If the sender doesn't address me by name, that's another red flag…and I'm probably not interested anyway.
4. The email’s English language syntax is broken: "Shared", "Regard", no punctuation. Never a good sign.
5. No one says click "ON" here…unless English is not their first language. Another red flag.
6. It asks me to click on a link (from a sender I don't know and trust). Nope.
7. I always inspect links in emails before I click on them. This one would fail.
8. Even if I got to the phony web page through a momentary lapse of reason, the login method is so obviously phishulous as to be comical.
9. The girl on the webpage has bad hair…eewww… (OK, not really…but still…)
Most of the places I would go online that require a login are places for which I've already set my own bookmarks. Even from senders I trust (financial, medical, other product and service providers), their email links are often loaded with tracking info. Sometimes I trust them (…Graham’s GCHQ newsletter, for example), but more often I use my own trusted bookmarks.
Social engineering relies on psychological manipulation of folks who too easily engage in "the willing suspension of disbelief". That's why there are epidemics of political majorities. A skeptical, educated public cannot be easily conned or scammed. That's one reason why I appreciate articles like this one.
The main client I use (pine) isn't one you access via a browser, so the temptation to follow a link is greatly reduced. Also, it tells me the actual domain name as well as the name it claims to be.
And ladysolly is far too canny to click on random links.
Now that is a long trip down memory lane; pine. I haven't seen any reference to it in at least 15 years (although I thought of it a year ago or so but only momentarily). It is – if I recall – based on pico and I hate modifier keys (I'm on the vi side of the vi / emacs fence and as far from the fence as is possible) so obviously I don't use it (although I have in the past) but it is a nice memory nonetheless. I still use lynx every so often, though. It is amazing how powerful and useful TUIs can be even to this day.
Did you send a reply back to the real agency letting them know? If so what was the response?