
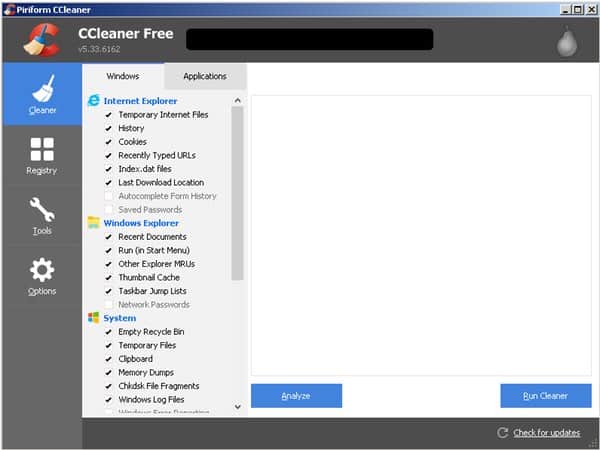
CCleaner is a popular Windows utility used by many millions of internet users to remove cookies, wiped browsing histories, and clean-up temporary internet files where malware might be lurking.
It’s the kind of tool that many tech-savvy Windows users rely upon to speed up and optimise their PCs.
It’s not the sort of program that they expect to introduce malware onto their systems. But unfortunately, that’s precisely what appears to have occurred.
Because CCleaner has suffered a “security incident” which saw users updated with a legitimate digitally-signed version of the software which opened a malicious backdoor.
The scale of the potential threat cannot be underestimated. Last year, CCleaner was boasting that it had been downloaded in total over two billion times, and was seeing five million additional users per week.
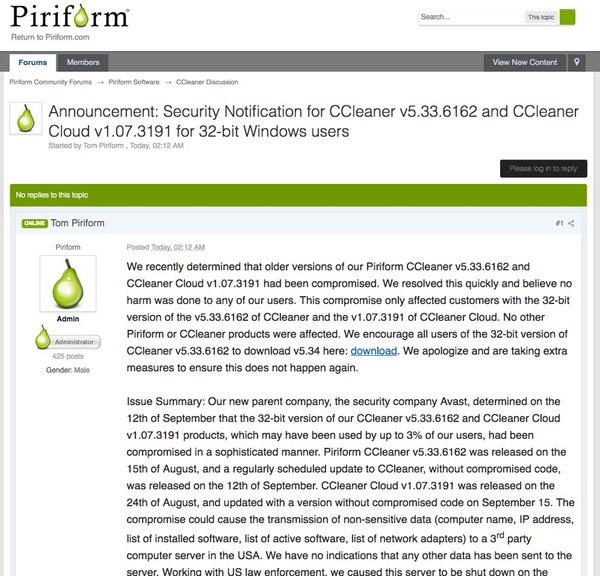
As a security notification on CCleaner’s support forum explains, CCleaner v5.33.6162 and CCleaner Cloud v1.07.3191 were compromised.
Once in place, the malware would wait five minutes, determine if the user had admin privileges, and then steal information from PCs, such as the computer’s name, a list of installed software and Windows updates, running processes, MAC addresses of network adapters alongside additional information.
The stolen data was then sent to a US-based server under the control of a hacker.
Researchers at Cisco Talos, who first identified the problem, discovered that the installer for CCleaner v5.33 – first delivered to users’ computers by the legitimate CCleaner download servers on August 15, 2017 – was the culprit.
What make things most concerning is that the malicious code was digitally signed using a valid digital certificate issued to the software’s developer Piriform, who were acquired by anti-virus firm Avast just two months ago.
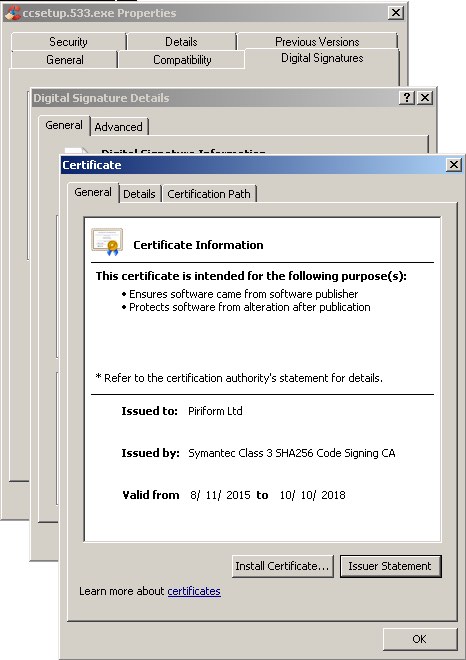
Cisco Talos researchers warn that the fact the binary was digitally signed using the software developer’s valid certificate is of particular concern:
“…it is likely that an external attacker compromised a portion of their development or build environment and leveraged that access to insert malware into the CCleaner build that was released and hosted by the organization. It is also possible that an insider with access to either the development or build environments within the organization intentionally included the malicious code or could have had an account (or similar) compromised which allowed an attacker to include the code.”
Cisco Talos researchers immediately informed Avast of the problem, and offending versions of the CCleaner installer containing the malicious payload are no longer available from the CCleaner download website. Law enforcement agencies have also been informed of the situation, and the third-party server that was set up to receive stolen data has been taken down.
It goes without saying that anyone still using version 5.33 of CCleaner needs to update to the (safe) version 5.34 as soon as possible. This message needs to especially get out to users of the free edition of CCleaner, as it does not feature automated updates and requires them to manually download updates. (Of course, the lack of automatic updates for the free edition of CCleaner may actually have reduced the total number of users put at risk by the compromised version.)
It’s worth pointing out that you may want to go one step further than just downloading a fixed version of CCleaner. After all, if you ran version 5.33 of CCleaner your PC may have been compromised. It might be sensible to roll-back your computer to a backup created before you installed that poisoned version of CCleaner.
And, if you’re in any doubt as to the scale of the potential threat, cast your mind back a few months when ransomware spread around the world after being seeded through a malicious automatic update to a popular Ukrainian accounting software, or when in late 2016 attackers hijacked Ask Toolbar updates to install suspicious code.
For more discussion of the CCleaner security incident, be sure to listen to this episode of the “Smashing Security” podcast:
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
So we recorded the podcast that people are about to hear on Tuesday because I was over in New York and it's now Wednesday evening.
It looks like a whole bunch of Deloitte's corporate VPN passwords, usernames, operational details—you can read all about this on The Register—were posted on a public-facing GitHub repository, which isn't good news.
And one of their employees was also, it appears, posting VPN passwords and login credentials to his public Google+ page.
Because obviously we do business with companies, all of us, and those companies may well be sharing information with Deloitte.
The joke that's going around on Twitter, although it's not really funny, is that maybe Deloitte needs an auditor.
They need someone to audit their security themselves, but people can hear what the situation was as of Tuesday in the following podcast. And we hope that you all enjoy it.
And it's good to be back in the UK. Yay!
Recorded Future arms threat analysts, security operators, and incident responders to rapidly connect the dots and reveal unknown threats.
Their patented technology automatically collects and analyzes threat intelligence from technical, open, and dark web sources. Why?
To provide invaluable context for faster human analysis and real-time integration with your existing security systems.
Sign up to their Cyber Daily newsletter and get the latest insights from Recorded Future at recordedfuture.com/intel.
Hello, hello, and welcome to another episode, Episode 45 of Smashing Security. My name is Graham Cluley, and I'm joined as always by my good chum and co-host, Carole Theriault.
I can't tell you. It was so— it's so high-tech and trendy, this hotel. But I've had a good time here. I've been speaking at the FraudForce conference hosted by IOvation.
That's been good fun. And then I'm going to catch the plane straight after this podcast back. But it's not just you and me, Carole. We are joined by our special guest.
So I'm here to talk to you about malware and other such nasties that you can find.
Each week we're going to look back on what's been happening over the last 7 days from the world of computer security, things which have tickled our nostrils and that we want to share our opinion about.
And I'm going to go first because bad news, chaps.
I'm afraid Deloitte, one of the so-called Big Four accountancy firms and one of the largest private businesses in the United States, has been hacked. Yeah.
Confidential emails, plans of its corporate clients, all kinds of guff have been exposed and put at risk by the hackers.
And the breach was revealed by The Guardian, who say that it went unnoticed for months.
Brian Krebs, the Krebsmeister himself, has been looking into this and good old Krebster, security blogger extraordinaire, has been suggesting that the breach may date back well into 2016.
He notes that there was a company-wide mandatory password reset back then. An anonymous source has told him that Deloitte has brushed the scale of the attack under the carpet.
Several gigabytes of data, according to his source, have been exfiltrated to a UK server.
But what happened was this: It looks like Deloitte, who of course work in a number of industries, right? They do auditing and tax consultancy and cybersecurity. Yes. Yes.
They give cybersecurity advice to multinational banks and pharmaceuticals, government agencies, and all the rest of that.
It looks like that one of their administrator accounts got broken into. A hacker managed to gain access to, well, unrestricted access to just about everything.
And that cloud-based account didn't have any two-factor authentication or two-step verification in place.
So maybe it was just a simple phish and before you know it, out came tumbling passwords, usernames, IP addresses, sensitive documents, you name it, which have all been entrusted to Deloitte by their clients.
So it's not just Deloitte's information. Yeah. This is information held by their blue-chip clients as well.
So it is rather insane that sort of protection wasn't in place and that this information wasn't properly defended.
And now, according to the Guardian, there's been an internal inquiry inside the company which they've codenamed Windham. Now, which made me instantly think of Triffids, actually.
You remember John Wyndham's book, Day of the Triffids? That isn't a dolphin, that's a Triffid attacking. It's my Triffid impression.
But no less apocalyptic, is it really, if something like this begins to breach out could be very damaging to the company, although it is downplaying the scale of the breach. Yeah.
Some reports are saying 5 million emails exposed maybe, but Deloitte are saying, oh, very few.
Their investigation, they say, has demonstrated that no disruption has occurred to client businesses or to Deloitte's ability to continue to serve clients or to consumers.
So it's saying it's taking security terribly, terribly seriously.
But let's face it, you know, if something like this happens, the damage which could be done is quite considerable because you sort of have this chain reaction.
It's not just damage to Deloitte, but all of those FTSE and big companies out there, which could be subsequently breached as a result.
And it wouldn't necessarily be possible to tell that those other subsequent hacks might be connected to this one.
I think people get so bombarded by this kind of thing that you just think, oh, another day, another big data breach.
But you know, maybe we should be feeling a little bit, you know, cross about these sort of things because why, why on earth wasn't there some two-factor or multifactor authentication in place on those admin accounts?
Those god-style attacks. Why didn't they have a whitelist of IP ranges which could access the account and anyone trying to access from anywhere else? Why wasn't that being blocked?
Why are there no defenses in place to spot anomalous behavior as millions of emails are being accessed as well?
I think companies can't afford to be complacent about this kind of thing.
But you know, it feels like they're trying to say small potatoes.
But as I mentioned, go and read Brian Krebs because he appears to have a source who is sharing more information and suggesting that this was on a much bigger scale than Deloitte is currently saying.
Now, whether that's true or not, who knows?
But history has shown that sometimes companies start off by saying something isn't that big a deal and then later have to admit actually it was worse than we imagined.
I mean, the threat here isn't just of data loss, but also phishing, business email compromise. So be careful.
And bad news for those many, many big companies who have Deloitte as a supplier, who they've trusted their information.
I think this is a message I'm hearing time and time again, is that businesses and individuals are entrusting their private information with others who aren't doing a good enough job of defending it, and something's got to be done.
I mean, I have two-factor authentication on all sorts of things that really don't matter. So that does seem quite a slip-up, but here's the thing I would think about on this.
Let's say they did have a lot more defense in place. Are they going to have all their defenses in place? Is there going to be no holes? No, not really.
It's really not about keeping a breach out, it's how you respond to one.
And I think that's really perhaps where Deloitte will prove their worth, or not, you know, their ability to deal with this situation.
Because you've got to assume that you can always be breached. You hope that it won't happen and you do a lot to try and prevent it, but that's got to be part of the assumption.
So how they deal with this breach, that's, I think, going to be— that's the pudding they're proving, if that's not extending the metaphor too far.
I think you're right that we shouldn't focus too much on how, although there's obviously a lesson there for other companies who may not have the simplest defenses in place.
And response is so important when you deal with these sort of incidents.
We saw the complete shambles, the omni-shambles that was occurring at Equifax, for instance, and has continued ever since then.
But I also think, oh yeah, okay, so yes, a company will always get breached if someone's determined enough.
But what you want to do, as most companies, is you want to be that little bit better protected than the other guys, because most of the hacks which take place aren't focused on your particular company.
It'll be a hacker who'll think, oh, this is too difficult. They've got these defenses in place, therefore I'm gonna find a weaker target instead. And there they failed.
And I think their customers would say, this information is pretty effing valuable to us. And what were you doing, Deloitte?
You successfully defend against all the opportunists, but I think, you know, it is about what they do in response to this and how are they protecting the data?
How are they ensuring that even if people do get hold of it, it's of no use to them?
So encryption and that kind of thing, which wouldn't necessarily protect you against an administrator, but it seems it was mostly email.
I think perhaps people think about email as being, well, it's just email, but attachments.
I think that would be— that's a big part of this, I think, is really how they respond to the breach.
And I think that's where companies are failing because, you know, at the end of the day, if you get breached and nothing bad happens because you've responded quickly or you responded effectively, then okay, then fair enough, you got breached, but, you know, no harm, no foul.
I would imagine there's probably still quite a lot of headless chickens going on. I don't know.
So you would think that they had a better coordinated response by now, but we will have to see. So I think Deloitte, watch out because maybe you're going to go down the to-loit.
So it's supposed to help you out, but unwittingly, users of CCleaner have been royally infecting themselves through its use.
It was actually discovered by my colleagues at Cisco, as well as actually, it has to be said, Morphisec. Essentially, good guys found it. And that's good.
Now, what's unusual in this particular case is that someone malicious got into the supply chain, as it were, and managed to digitally sign an update to CCleaner which had malware in it, right?
And then of course that rolled out around the world.
So any kind of security products that you're using that kind of evaluate signatures or certificates, that's going to pass that test because it all looks legit.
It's all signed by a trusted source. And that's really going to help your malware spread.
Now, all of those websites, as we speak today, those are under the control of Talos, which is Cisco's threat intelligence organization.
Kind of the back end of it has been taken down now.
But I mean, we have seen some evolution in the malware in that it seems to be also targeting high-profile companies, Cisco being one of them, as well as some others.
I think, you know, it's interesting that we're actually seeing this referenced in the source code of malware, but yeah, that is pretty common.
Again, digitally signed, I think it was, of an accountancy program. Yeah, Medoc. Which was, you know, yeah, that's it, Medoc.
And it does feel like this is a growing problem, the supply chain attacks.
So software which you've already approved, which you're allowing to update inside your environment, which may be antivirus software as well, is saying, oh, this piece of software, this is digitally signed by XYZ company, therefore it's less suspicious.
Actually can be a method by which the attackers can crawl onto your network.
You know, attacks are campaigns. You know, we're seeing strings of compromised servers being used to proxy command and control traffic.
And obviously you've got to compromise a lot of organizations to actually, before you even start your real attack. You know, it's big business, isn't it?
And obviously now people are able to make a lot of money out of it.
They're able to invest a lot of money back in the technology and that's, you know, that's a big part of the problem.
Carole, I imagine you've got something similarly uplifting to entertain us with for your section.
And I want to talk about Twitter finding itself in a spot of bother this week.
So the problem reared up in response to yet another inflammatory tweet from Donald Trump, once again aimed at North Korea. Sorry, Donald who?
So on the 22nd of September, the person you've never heard of, Graham, tweeted 'Kim Jong-un of North Korea, who is obviously a madman who doesn't mind starving or killing his people, will be tested like never before!' And then, and just two days ago, Donald Trump said, 'I just heard Foreign Minister of North Korea speak at the UN.
If he echoes the thoughts of the little rocket man'— that's a reference to Kim Jong-un— 'they won't be around for much longer.' So this is all getting very heated.
North Korea's foreign minister has taken these tweets as a declaration of war. What? Yes.
Quote, since the United States declared war on our country, we will have every right to make countermeasures, including the right to shoot down United States strategic bombers even when they are not yet inside the airspace border of our own country.
So, right. So this is all scary stuff. And it's all done with this weird air of WWE SmackDown, right?
It's— Phil, you were a big WWF fan in the old— that's what it used to be called, right? WWF?
That's going back some.
This is the problem I kind of want to talk about today. So these tweets from Donald Trump are arguably breaking the rules of conduct for Twitter.
And when I say arguably, I'm saying, yeah, they definitely break the rules of conduct for Twitter. So I had to go, I went and had a little look.
And in the abusive behavior section of the Twitter rules, there is sections on violent threats, direct or indirect harassment, and hateful conduct are all listed as big no-nos.
So a bunch of folks who most likely find Trump's use of his personal account for presidential communications/threats inappropriate started reporting the tweet as a breach of the Twitter rules.
Reporting Donald Trump's tweets. Reporting Donald Trump's tweets that we've read out earlier in my segment, right?
Saying basically these need to be removed because they're inciting violence. And yes.
So many people complained that Twitter actually issued a 6-part tweet to explain why Donald's message was not going to be going anywhere anytime soon. So let me read this to you.
So it starts, some of you have been asking why we haven't taken down the tweet mentioned here. Link in show notes.
We hold all accounts to the same rules and consider a number of factors when assessing whether tweets violate our rules.
Among the considerations is newsworthiness and whether a tweet is of public interest. This has long been internal policy. Okay, this is the bit I love.
This has long been internal policy and will soon update our public-facing rules to reflect it. We need to do better on this and will.
Twitter is committed to transparency and keeping blah, blah, blah, blah. So this is a really aggravating and loopy response to my mind, because this is how I read it.
And I'd love to know your opinions. Okay. So I'm seeing this as, hey, Twitter users, you're all the same. So your account is as important to us as Trump's account. Hmm. Okay.
But if you get a lot of traffic, it probably means that you're newsworthy. And then I guess we can treat you a Twitter VIP.
And you can break whatever rules and we're going to look the other way, no questions asked. That's what I'm reading.
Yeah, maybe not as a great advert for it, but he's increased its profile because I'm here in the States at the moment, I turn on the news and there's a constant ticker up there basically saying, and he's just tweeted— this morning, for instance, it said he's just tweeted 2 minutes ago about, you know, the TV ratings for the NFL going down, right?
Because that's really what matters. But, you know, there's constant commentary about it.
Where does the man separate from the responsibilities of the President of the United States?
However, there is this extra private consideration of newsworthiness, which basically means if you have 10 million followers on Twitter, then you can just do what the heck you.
So I imagine that can just grow over time as is appropriate to their requirements. I don't know, I just feel they should do better.
What occurred to me about how he tweets presidential business from his own account, I wonder if he's not too good at swapping between accounts.
He's just not really— his thumbs aren't really— so we're going to get a bit feeble for him. He's old, he's a dotard. What is this word, dotard?
So it's something that— the Korean— I think it was actually Kim Jong-un himself addressed Donald Trump directly at a kind of what passes for a press conference in North Korea and actually called him a dotard, which I think is an old fool, basically.
Recorded Future is the real-time threat intelligence company whose patented machine learning technology continuously analyzes technical, open, and dark web sources to give organizations unmatched insight into emerging threats.
Sign up for free daily threat intelligence updates at recordedfuture.com/intel.
Doesn't have to be security related— shouldn't be. But, well, you know, doesn't have to be.
And my Pick of the Week this week is the— now I don't know if it's pronounced Wildergon or Wildergon— coloring posters.
I want you to travel back in time and imagine a little boy with bushy eyebrows lying on his parents' carpet with some felt tips and filling in this wonderful, fantastical— actually, Phil, you would love this because you like all that fantasy stuff.
These are really cool. Not that— well, I don't know, maybe you do as well.
But anyway, these are some really cool black and white posters of sort of— it's Tolkien-esque almost kind of stuff.
And you have your little pot of pens and you can draw them in and they're very—
And I can recommend the Wilder Gorn coloring posters, and they have names like this, they have names like The Pog's Defense, Potter's Road, Tower Mine.
One for you too, the Gong Wizards.
And yeah, it's really cool and fun. And so I like doing them. And that is my pick of the week.
You're probably aware that there is very, very soon going to be a new instance of Star Trek hitting the screens.
Star Trek Discovery on Netflix comes complete with Klingon subtitles. No. Throughout. I love Klingon subtitles.
There's a fairly good chance that she has, and you know, fair enough, frankly, because she's enough to put up with as it is. Okay.
Although I'm going to go home and see if I can find it.
You in particular, because you did get Sophos, when we worked at Sophos, to produce a version of Sophos antivirus translated into Klingon.
With YMCA being sung in Klingon in the background over it. That's right.
But as I remember, the way to swear in Klingon is to say, I don't know, you say something like, something like that. But what it means is your mother has a smooth forehead.
I don't mean porn, Graham. What I'm talking about is Rik and Morty. For those of you who know it, yay you, because it's great.
And those of you don't, you should check out Rik and Morty. Rik and Morty. Yeah.
So on one side you have extremely selfish alcoholic genius asshole of a grandfather who's dragging around his nervy, morally centered grandson across space and getting caught into loads of intergalactic adventures.
Okay, so that's kind of one. Sounds brilliant so far.
Now it's also set against the backdrop of this really painful everyday family dark domestic drama that's going on, where there's some drinking and there's divorce talk and there's fighting and there's in-laws and there's kids running away from home and school dances and girls and all this stuff.
And I don't know, the characters are just good. The story's dark, it's smart. And season 3 so far, wow. Anyway, so you can see it on streaming service.
I think Hulu and Netflix have it.
And if you're already totally caught up with Rik and Morty, as I have, you may want to go back to the beginning, which I have, or I will put a few more really good animations inside the notes you guys can check out.
Okay.
He's the one who said you might this and it's great.
Well, thank you very much, Carole, for that pick of the week. Maybe we'll go check that out. So, that just about rounds up the show, doesn't it? It does. Yeah.
If you want to find out more about us, go on to Twitter. We're at Smashing Security without a G, and we've got a Facebook group which you can get to smashingsecurity.com/facebook.
And maybe you want to support the show by buying a t-shirt before that imminent global thermonuclear war begins at smashingsecurity.com/store.
All that remains is we need to thank Phil Wood for joining us today. Thank you very much, Phil. My pleasure.
If you know someone else who might like the Smashing Security podcast, please tell them about us and go to smashingsecurity.com for past episodes to get in touch.
Until next time, cheerio, bye-bye.
It's, you know, you can't— there's no nuance in 140 characters, and I think a lot of people get very cross when they aren't able to, you know, hear a full explanation.
And I find it of little use. So, yeah. Do you know what the real reason is? I don't get it. I'm too old.
I looked at it and, as I say, it just bewildered me and I thought, you know what? Dotard.




Typo : "Bad unfortunately, that's precisely what appears to have occurred."
Yoy must have meant to say: "But unfortunately,"
Thanks – I thought I had fixed that hours ago, but clearly I forgot to press the "Update" button in my CMS.
You see, manual updating can lead to failure for us bloggers too… ;-)
Avast did make Ccleaner
Ah, you updated it.
A report on a significant security breach, and you're concerned about the grammar! Too funny.
<wags head>
3% of 2 billion downloads, is still a lot – but no where near 2 billion.
The backdoor was only in the 32 bit version. If you have the 64 bit version you were not effected.
Affected.
Just delete your own history and run disk cleanup – all baked into your web browser (s) and windows.
This is the standard nightmare of every antivirus company.
The timing is suspicious, in that, it was done not long after Avast took over. One has to wonder whether a disgruntled, or perhaps fired, ex-employee was behind this. Especially in light of the digital signed cert. Surely law enforcement will be looking in that direction first.
They say the problem is fixed and it only affected the 32 bit version. I wonder if the hacker may already be working on hacking the 64 bit version next.
Piriform was bought by anti-virus firm Avast just two months ago. Seems strange that this happened soon after this transaction. I kind of wonder about the credibility is Avast software after this. Maybe a disgruntled employee at Piriform did not like this sell out and sabotaged the CCleaner software.
Thank God I didn't run mine. I have the free version and just updated it. They send out a stern warning. The paid version of Malware Bytes also blocks almost every page unless you allow the page to run. Since I only have a few days left on the trial, I'm not going to bother. An then there's Bitdefender at the end of the month. Their videos on the lack of privacy are really eyeopening.
"We fixed it. Trust us. No other versions were affected." Prior to this discovery, they would have assured us all that NO versions were affected by Malware. My first thought is that their entire Quality Control team should be relieved of their duties.
How can we ever trust this company again?
Oh crap, I'm still using v5.32.6129 and the 64bit version at that. I miss all the fun.