Is your browser’s built-in login manager leaking your username (and possibly your password too)?
Researchers at Princeton’s Center for Information Technology Policy have uncovered two third-party tracking scripts, that can scoop up information provided by your browser’s login manager to create a persistent identifier, tracking you as you move between webpages.
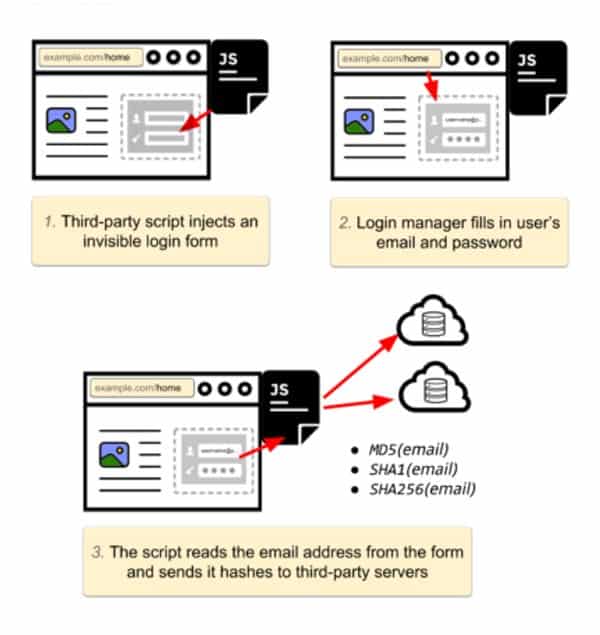
Here’s how it happens:
- You visit a webpage and fill out a login form. Your browser asks you if you want to save the login details.
- Later, you visit a different page on the same website, which includes the third-party tracking script. The tracking script inserts a login form that is invisible to the naked eye onto the webpage, and your browser’s password manager automatically fills in your credentials.
- The third-party script snaffles up your email address from the invisible form’s field and sends a hash to a third-party server.
What’s the solution? Simple. Don’t use a login manager that autofills forms without you giving it explicit permission to do so. You might be wiser using a product like 1Password, whose developers confirmed was designed to always insist on user approval before filling forms.
If you allow your browser to automatically submit your username and password into forms silently and invisibly, there is always the danger that a malicious site or script may steal the information.
The two scripts spotted by the Princeton researchers – AdThink and OnAudience – appear to have been designed to grab hashed usernames to identify web visitors for ad-tracking purposes, but there is no technical reason why the same approach couldn’t also be used to steal autofilled passwords.
The researchers have built an online demo, where you can test whether you might be vulnerable.
It should go without saying – don’t enter real credentials on that demo page!


Shameless plug
1Password has never allowed automatic autofill, exactly because of attacks like this (and even worse).
Cheers,
-j
Chief Defender Against the Dark Arts at AgileBits (the makers of 1Password)
I use Dashlane and, after storing my test information, I tried auto-filling and non-auto-filling my information and neither time did my data get compromised – or, at least, the fields showed nothing on the test page.
I have always been of the opinion, possibly misguided, that the credentials would/should only be presented to a specific URL and not the general domain – i.e. there has to be an exact page name match for the credentials to be provided – if the password manager is any good?
I always use a password manager – I never allow a browser to store passwords, or allow a site to remain logged in (unless I forget…).
Happy New Year!!!! Mozilla Firefox 57. is doing it? Any comments? Thank you
FF57 is vulnerable yes.
FWIW NoScript doesn't currently pick up on this (that or they use a server that is used elsewhere and I have thus whitelisted?). Perhaps this should be reported to them but I have too much going on to deal with that atm. Nevertheless even if they do fix it many people don't like NoScript.
Because of said too much going on do they describe how it works? Let's use example.com and example.net for example. But let's pretend they're on different servers or isolated processes. Is it possible for a script on example.com to attempt to log in to example.net and thus sniff it ? Of course the impossible can become possible but that's for the future.
Right. I just read the summary. I do have a lot going on as I noted.
Something else. There is a semantics thing going on here. At least on the surface. Most people are going to think of it auto-fills only when you are attempting to log in. Also they will think that you have to click 'log in' (or whatever) to do this and thus nothing is sent. But of course it could be working at a different level and/or in addition. It's masquerading it in the end. This is all the more reason to use 2SA/2FA when possible – whether you're using this feature or not. Multiple layers.
To elaborate on my semantics point.
Are you saving the password so you can then click 'log in' without having to type the login/password? Or are you saving it so that you don't have to bother logging in? And if you don't have to log in every time is it because of that or session cookies (I might be mixing that up)?
And therein lies the problem: one might expect you have to click 'log in' but not necessarily.