Officials at Bristol Airport in the UK declined to pay a ransom demand from extortionists who attacked its computer systems late last week.
Computers running public information boards displaying flight arrival and departure times were taken offline on Friday morning, in an apparent attempt to contain a malware infection.
Travellers arriving at Bristol Airport early on Friday morning found that flight information screens were down due to “technical problems”. On its Twitter account, the airport advised passengers to arrive early and allow extra time for check-in and boarding.
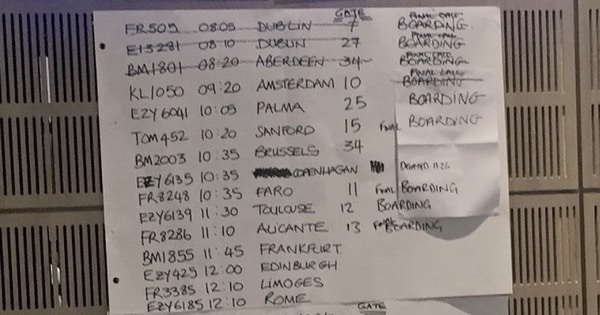
Details of check-in desks. boarding gates and arrival/departure times were made over the public address system, and further information was manually updated on whiteboards.
James Gore, a spokesperson for Bristol Airport, described what occurred to BBC News:
“We believe there was an online attempt to target part of our administrative systems and that required us to take a number of applications offline as a precautionary measure, including the one that provides our data for flight information screens. That was done to contain the problem and avoid any further impact on more critical systems. The indications are that this was a speculative attempt rather than targeted attack on Bristol Airport.”
By 6:30am on Sunday it appeared the airport was returning to normal, and a tweet was posted announcing that the information screens were functioning once again.
Live flight information has now been restored to digital screens in key locations in the terminal. pic.twitter.com/pm4R0sZ4eX
— Bristol Airport (@BristolAirport) September 16, 2018
I’m not just pleased that Bristol Airport felt comfortable not paying a ransom to the extortionists who attacked their network, suggesting officials had confidence in their backup infrastructure and ability to restore compromised systems.
If you have a secure backup, and if you have the systems in place to restore that backup in a safe, prompt fashion, then you shouldn’t need to ever consider paying the criminal who is attempting to extort money from you.
No, I’m also impressed that Bristol Airport clearly had emergency contingency plans in place to keep passengers informed about their flights, to keep inconvenience for travellers to a minimum.
All organisations would do well to consider how well they could survive – even for a short period of time – if some of their computer systems were disabled unexpectedly.