 A new whitepaper reveals that a hacking gang known as Black Vine shared certain zero-day exploits with other digital espionage groups.
A new whitepaper reveals that a hacking gang known as Black Vine shared certain zero-day exploits with other digital espionage groups.
In a blog post introducing the report, security firm Symantec provides some background on Black Vine.
Black Vine is known to have used two zero-day exploits, Microsoft Internet Explorer ‘CDwnBindInfo’ Use-After-Free Remote Code Execution Vulnerability (CVE-2012-4792) and Microsoft Internet Explorer Use-After-Free Remote Code Execution Vulnerability (CVE-2014-0322), as part of watering-hole attacks, which the groups members used to deliver malware to visitors to legitimate websites.
In the event that their attacks proved successful, the attackers then dropped their own custom malware, including Hurix and Sakurel – both of which are detected as Trojan.Sakurel – and Mivast, onto the victim’s machine.
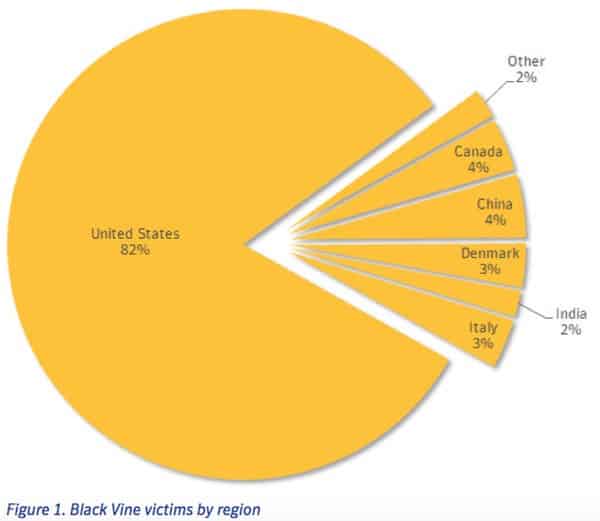
Symantec goes on to note in its report that Black Vine has conducted numerous campaigns against the military, defense, energy, and agriculture sectors, though its primary targets have been companies in the aerospace and healthcare industry.
The threat group is believed to have been responsible for the hack against US health insurance company Anthem earlier this year, an incident which may have compromised the sensitive information of as many as 80 million people.
According to Vikram Thakur, senior security researcher with Symantec, the Anthem breach and other incidents might reflect only a secondary interest in stealing people’s information.
“If someone just has Vikram’s healthcare records, overall there’s very little gain,” Thakur told Ars Technica. “But then you get healthcare information about a Vikram working for a government entity or a defense contractor, there is substantial value in that. This is the kind of data that’s used in combination with something else to reach an entirely non-healthcare related goal.”
 Many of the zero-day exploits used by Black Vine were integrated into the campaigns of other digital espionage groups at around the same time.
Many of the zero-day exploits used by Black Vine were integrated into the campaigns of other digital espionage groups at around the same time.
For instance, Symantec’s paper says that Black Vine was using its zero-day exploits at the same time as the Hidden Lynx hacking group was using the same vulnerabilities to successfully target security firm Bit9, as well as a range of corporate and government targets around the world.
According to Symantec, this confirms the existence of the Elderwood Project, a zero-day exploit-sharing framework on which numerous threat actors rely to conduct their attacks.
While these campaigns included the same zero-day exploits, they delivered different payloads unique to each attack group. The fact that these different adversaries simultaneously used the same exploits suggests that they all have access to a common zero-day exploit distribution framework.

It is all too easy to subscribe to the mindset that malicious actors act according to self-interest and would therefore never cooperate with like-minded nefarious individuals. But Black Vine and the Elderwood Project contradict this expectation.
We need to come to terms with the fact that in order to enhance the effectiveness of their attacks, hacking groups will collaborate together and share exploits.
This development further emphasizes the need for us to approach security as a community and to meet these threats together as a united front.


