Researchers have spotted an ongoing tax-themed malicious email campaign that is delivering the NanoCore remote access trojan (RAT) as its malware payload.
Anthony Kasza and Tyler Halfpop, malware researchers at Palo Alto Networks, write in a blog post how they recently spotted the campaign after coming across a number of emails with malicious attachments and with subject lines featuring the words “tax”, “pin”, and “report”:
- [Attention] Your 2014 Tax Report
- [Urgent Attention] Your 2015 Secure IP PIN
- [ATO: URGENT] Your 2014 Tax Return Report!
- [URGENT ATTENTION] Your 2014 Tax Return!
- [ATO: ATTENTION] Your 2015 Tax Return PIN!
- [IRS ATTENTION] Your 2015 Secure IP PIN!!!
- [HMRC ATTENTION] Your 2015 Tax Report PIN!
- [ATTENTION] Your 2015 Tax Return PIN!!!
The researchers shared details of the scale of the malware campaign:
“Within the final sample set, we were able to identify 70 unique malware samples distributed through 2,062 email sessions between September 2, 2015 and January 28, 2016.”
In this attack, the email senders use addresses such as “2015-autax-return[at]ato[dot]gov[dot]au,” “2015autaxreturn[at]ato[dot]gov[dot]au,” and “2015tax-return[at]irs[dot]gov” to enhance the legitimacy of their messages.
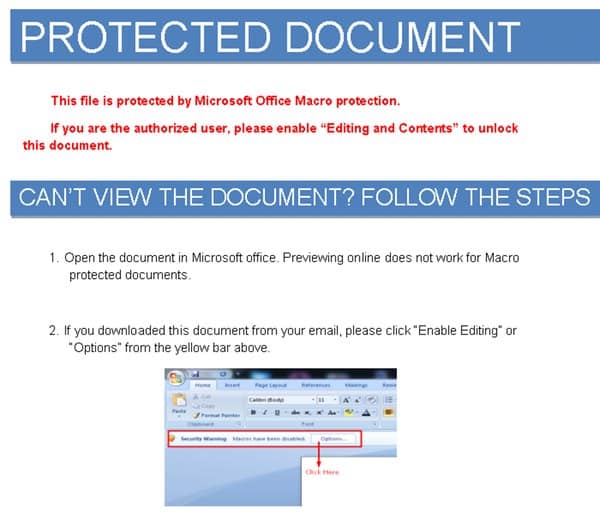
Of course, these addresses are only meant to lull users into a false sense of security and entice them to open the attachment – either in the form of an .EXE executable file or a Microsoft Word document containing malicious macros.
Audaciously, the boobytrapped Word documents contain a guide for its intended victims on how to ensure that macros are enabled, in order that their computers can be easily compromised.
Regardless of the form of each attachment, the malware’s payload consists either of the NanoCore RAT or a macro downloader that can execute the trojan.
According to Symantec, NanoCore dates back to at least 2013, when a cracked alpha version of the trojan first appeared online.
The malware went through at least four beta versions after that before the full version (1.2.2.0) finally made an appearance. That version was also eventually cracked and leaked online, which resulted in an increase in targeted and non-targeted attacks using the tool in March of last year.
In its current incarnation, NanoCore is a modular RAT that derives its capabilities from a number of plug-ins. These add-ons allow the malware to log keystrokes, download and install other software, edit the registry, modify the firewall, and assume control of the infected PC’s webcam.

Clearly, NanoCore can wreak some serious havoc if it gets its hands on a user’s machine. To prevent that from happening, users should always stay on the lookout for suspicious emails and attachments, especially those that pertain to their tax reports.
For added details of how to protect your computers, please view Palo Alto Networks’ article, which includes a number of indicators to look out for, including email attachment names commonly used by NanoCore in this campaign.



NanoCore is not malware, it is a legit tool that bans anybody that uses it maliciously.
The cracked version is a modified version of the official release.
https://blog.pagefair.com/2015/halloween-security-breach/
http://boingboing.net/2015/11/08/the-economists-anti-ad-block.html
http://www.theverge.com/2015/11/6/9681124/pagefair-economist-malware-ad-blocker
Here are the responses after a similar attack, the general acceptance is that NanoCore is legit software. All users caught in this attack were banned and the NanoCore team worked with every website effected in order to sort it out, the end result being that the attack was banned and the victims were safe.
This attacker is using a modified crack version meaning they cannot be banned from using it.
Saying NanoCore is malware is like saying Window RDP is malware because it can be used maliciously, it's just nonsense.
I really do hope you update this post to better reflect what NanoCore actually is.
You need to think about this a bit differently. Whether or not it is cracked is irrelevant: there is a remote access trojan version of Nanocore and that is what the article is about. But I'll humour you. Amusingly on their website:
'Build with stability in mind.
NanoCore aims to be the most stable and reliable Remote Admin Tool on the market, and trust me, there are no other RATs are as stable as NanoCore. '
You know what is amusing about that?
They change the A to be 'admin' and the T to mean 'Tool' but you could argue that indeed it is a tool (but definitely not an administrator tool or at least not for a legitimate admin here) to those attacking. You can also say that a sniffer is 'bad' and a 'traffic analyser' is good (even though they're the same thing) but it's the use that matters; it doesn't matter how it's done so much as it is done.
Cracked or not it's being used as a trojan and therefore it is malware (whether IT is the official version or not is only relevant if you're arguing semantics). But there is another amusing thing. People that are terrible liars (not saying they're lying here but it does say some other things about them) tend to say things like 'Believe me…'. In addition, as a long time programmer I find it rather hilarious that anyone would say there are no other [whatever] that are as stable as [us]. Why is that? Because many things can be completely stable but that doesn't mean they are of the same quality, have the same features, are better or worse or anything else. Stability can also change over time. In addition, it's only the most stable currently (and only of those they know about!). I'll humour them also: even if it is the most stable it clearly isn't the most secure, is it, when there is a cracked copy that is being used as a trojan horse. The fact all software is vulnerable to this or that is simply ignoring the points.
So the article doesn't need to be updated and in fact shouldn't be because it is discussing the software being used as a trojan horse and that is Nanocore. Cracked or not it's still nanocore just like cracked Windows is still Windows.
Just curious. I've been using Linux since 2004 (Fedroa….rock solid baby!) And to date?…I haven't gotten infected with ANYTHING, not ot mention that almost ALL ".exe" files DO NOT RUN in Linux….can this Nanocore RAT affect me at all? just wondering….i mean between the Root Kit Hunter…..ClamAV…..Chkrootkit….iptables…..UFW…..and all the other nifty tools that exist to keep my machine safe…..wil this particular menace harm my machine?……just wondering is all…
Looking at the paper http://researchcenter.paloaltonetworks.com/2016/02/nanocorerat-behind-an-increase-in-tax-themed-phishing-e-mails/ :
I see references to socks proxy which is very much a Microsoft thing. I also see references to a Microsoft routine Assembly.Load. In addition I see references to DLLs. It's true that Linux has dynamically loadable libraries but they're typically called share objects (hence the extension: .so) or shared libraries. This makes me think it's the Windows DLLs.
You're right to be concerned (only very ignorant people say things like Linux is immune to malware) but you're probably OK. I would caution you don't disregard it completely though: is your network completely segregated from Windows machines that have been exploited? Is your mail server securely configured (not an open relay for one example)? I grant you that some of those are more like backscatter (closest thing I can think of at this time) but they're still things to consider. There are other things to consider too but you're probably OK.
I'd also like to point out that in Linux (and Unix generally) extensions don't exactly matter when running a binary file (also called 'text files' but I'll not get into that) and it's more like the file header that matters (actually Windows uses headers too but I'm talking about Linux). See also file /etc/magic (as I remember it from years ago.. seems in more recent Linux releases it's now a system specific file like files you might find under /etc/sysctl.d where /usr/share/magic is the file in question). You can also see magic(5).
My point is that referring to extensions in files mostly is irrelevant in Linux (though there are of course some de facto standards like .pl, .sh and others). But yet you should never say: Okay, this file ends with .exe so it must be a Microsoft PE exe file and it is somehow harmless. For instance (and I hope I got the html escape sequences all right):
$ cat > rat.exe << "EOF" #!/bin/bash echo All rats are brats EOF $ chmod +x rat.exe $ ./rat.exe All rats are brats If you were to run the file command on it you'd see that despite the extension it is something else. Something ot keep in mind. If you were to cat the file you'd see what I typed in (without the blank lines).
Typically the html escape codes went afoul. If I could edit…
Anyway, change the > to be > and the < to be < and it's then right.
Maybe it now properly converts it? Testing but if not the above should hopefully explain it (or maybe you know it already).
$ cat > rat.exe << "EOF"