 The Shellshock bug in Bash being actively exploited online.
The Shellshock bug in Bash being actively exploited online.
According to reports, malicious hackers are exploiting the flaw to spread malware, open backdoors, and launch denial-of-service attacks.
Which means that it’s important that vulnerable devices are patched as quickly as possible.
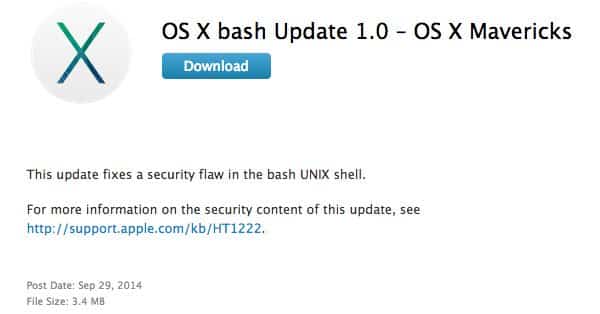
So it’s good to see that overnight Apple has rolled out what it is calling “OS X bash Update 1.0” for users of Mavericks, Mountain Lion and Lion.
The good news is that the vast majority of Apple’s Mac OS X users probably weren’t at risk from having their computers exploited by the Shellshock vulnerability because they wouldn’t have configured their systems in such a way as to allow the Bash shell to be accessed remotely. The better news is that Apple hasn’t used this as an excuse not to patch the bug regardless.
So, if you use Mac OS X, make sure you download and install the patch.
If you’re not sure whether you are running a patched version of Bash on your Mac, here’s how you check.
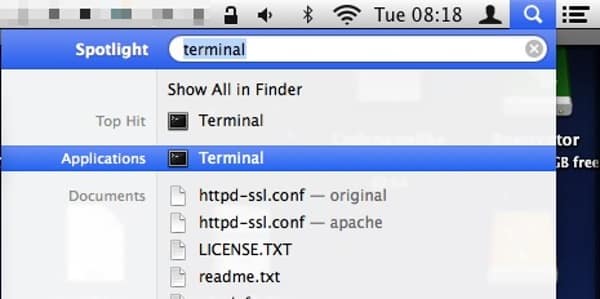
Open the Terminal application (which you can either find via Spotlight search, or by navigating to the Applications / Utilities folder).
Enter the following command at the $ prompt:
bash -version

If you’ve done that correctly, you should be shown a version number for Bash.
On Mavericks, it should now say GNU bash, version 3.2.53(1)-release (x86_64-apple-darwin13).
On Mountain Lion it should say GNU bash, version 3.2.53(1)-release (x86_64-apple-darwin12).
And on Lion it should say GNU bash, version 3.2.53(1)-release (x86_64-apple-darwin11).



Very Timely and Useful Bash/Mavericks info from you Graham.
Needless to say Apple aren't as quick off the mark as you are, but the info you supplied enabled me to find and download the update; WITHOUT having to wait for Apple to tell me about it, if they ever did.
Thanks again
Jim Goodyear
Here is a great Video on it
https://www.youtube.com/watch?v=jmqCXUa7zOs
i run lion, and the update seems to be only for maverick….this is my bash version "version 3.2.48(1)-release" now what do i do?????
k
ok, thanx to your site, i found the lion link for the patch…..thanx so much….all is good
k
For the Mavericks fix, open URL http://support.apple.com/kb/DL1769
I also found this from http://support.apple.com/downloads/
If that does not work, open URL in their image above: http://support.apple.com/kb/HT1222
Ray