Since this article was first published we have released a revised and more complete history of Mac malware. Make sure to check out that version!
There’s been a lot of discussion in the media recently about the threat that malware poses on the Mac OS X platform. It’s clearly an emotive subject, with strongly held views on both sides.
To help some of the discussions, here’s a brief overview of some of the malware we have seen infecting Apple computers. From the early 1980s, right up until the present day, here are some of the highlights in the history of Apple Mac malware.
Mac virus timeline
1982
The first virus to affect Apple computers wasn’t written for the Macintosh (that iconic computer wasn’t set to appear until 1984) but is of historic interest none the less.
 In 1982, 15-year-old student Rich Skrenta wrote the Elk Cloner virus, capable of infecting the boot sector of Apple II computers.
In 1982, 15-year-old student Rich Skrenta wrote the Elk Cloner virus, capable of infecting the boot sector of Apple II computers.
On every 50th boot the Elk Cloner virus would display a short poem:
Elk Cloner: The program with a personality
It will get on all your disks
It will infiltrate your chips
Yes, it’s Cloner!It will stick to you like glue
It will modify RAM too
Send in the Cloner!
What may surprise some Apple fans is that the Elk Cloner boot sector virus predates IBM PC viruses by some years.
1987
 The nVIR virus began to infect Macs, spreading mainly by floppy disk. Source code was later made available, causing a rash of variants.
The nVIR virus began to infect Macs, spreading mainly by floppy disk. Source code was later made available, causing a rash of variants.
1988
HyperCard viruses emerged that could run on early versions of Apple’s Mac OS. One HyperCard virus showed the message “Dukakis for President” before self-destructing.
1990
The MDEF virus (aka Garfield) emerged, infecting application and system files on the Mac.
1995
Microsoft accidentally shipped the first ever Word macro virus, Concept, on CD ROM. It infected both Macs and PCs. Thousands of macro viruses followed, many affecting Microsoft Office for Mac.
1996
Laroux, the first Excel virus, was released. Mac users were unaffected by this new strain of macro virus until the release of Excel 98 for Mac meant they could become victims.
1998
It was in Hong Kong, in 1998, when the next significant Mac malware outbreak was first spotted. A worm – dubbed AutoStart 9805 – spread rapidly in the desktop publishing community via removable media, using the CD-ROM AutoPlay feature of QuickTime 2.5+
David Harley of Macvirus tells me that he remembers watching with interest as reports of Autostart spread from Asia to the rest of the world.
In the same year, Sevendust, also known as 666, infected applications on Apple Mac computers.
Big changes to the Mac malware scene were just around the corner, however, with the release of Mac OS X – a whole new version of the operating system which would mean that much of the old malware would no longer be capable of running. In the future, Mac-specific malware would have to be written with a new OS in mind..
2004
 The Renepo script worm attempted to disable Mac OS X security, downloaded hacking tools to affected computers, and gave criminals admin rights to the Apple Macintosh.
The Renepo script worm attempted to disable Mac OS X security, downloaded hacking tools to affected computers, and gave criminals admin rights to the Apple Macintosh.
Hackers also wrote a proof-of-concept program called Amphimix which demonstrated how executable code could be disguised as an MP3 music file on an Apple Mac.
2006
Leap-A, the first ever virus for Mac OS X was discovered. Leap-A can spread via iChat.
The Inqtana worm and proof-of-concept virus soon followed.
A buggy proof-of-concept virus called Macarena appeared, written in Xcode. Every infected file contained the phrases
“MachoMan – roy g biv”
and
“26/10/06”
2007
 Sophos discovered an OpenOffice multi-platform macro worm capable of running on Windows, Linux and Mac computers.
Sophos discovered an OpenOffice multi-platform macro worm capable of running on Windows, Linux and Mac computers.
The BadBunny worm dropped Ruby script viruses on Mac OS X systems, and displayed an indecent JPEG image of a man wearing a rabbit costume.
The first financial malware for Mac was discovered. The gang behind the attacks developed both Windows and Mac versions of their OSX/RSPlug-A Trojan horse.

The Trojan posed as a codec to help users view pornographic videos, but in fact changes DNS server entries to direct surfers unwittingly to other websites.
2008
Cybercriminals targeted Mac and PC users in equal measure, by planting poisoned adverts on TV-related websites. If accessed via an Apple Mac, surfers would be attacked by a piece of Macintosh scareware called MacSweeper.
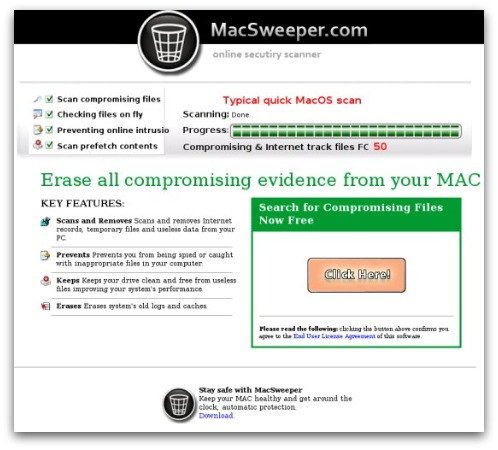
Close relatives of MacSweeper followed shortly afterwards, including Imunizator – another example of scareware for the Apple Mac, which claimed to find privacy issues on the user’s precious computer.

In June, the OSX/Hovdy-A Trojan horse was discovered that could steal passwords from Mac OS X users, open the firewall to give access to hackers, and disable security settings.
Troj/RKOSX-A was discovered – a Mac OS X tool to assist hackers create backdoor Trojans, which can give them access and control over your Apple Mac computer.
 In November, Sophos warned of the Jahlav Trojan. Like in other malware campaigns, cybercriminals created a bogus webpage claiming to contain a video. Visiting the site produces a message saying that you don’t have the correct codec installed to watch the video – whereupon the site offers you an EXE if you run Windows, and a DMG (Disk Image) file if you are using an Apple Mac.
In November, Sophos warned of the Jahlav Trojan. Like in other malware campaigns, cybercriminals created a bogus webpage claiming to contain a video. Visiting the site produces a message saying that you don’t have the correct codec installed to watch the video – whereupon the site offers you an EXE if you run Windows, and a DMG (Disk Image) file if you are using an Apple Mac.
Controversially, Apple issued a support advisory urging customers to run anti-virus software – but after media interest, rapidly deleted the page from their website.
2009
 In January 2009, hackers began to distribute the OSX/iWorkS-A Trojan horse via BitTorrent inside pirated versions of Apple’s iWork ’09 software suite.
In January 2009, hackers began to distribute the OSX/iWorkS-A Trojan horse via BitTorrent inside pirated versions of Apple’s iWork ’09 software suite.
In the same month, a new variant of the Trojan was distributed in a pirated version of Adobe Photoshop CS4.
In March, Sophos reported on how hackers were planting versions of the RSPlug Trojan horse on websites, posing as an HDTV program called MacCinema.
https://youtube.com/watch?v=RTeSYmQS820
In June, SophosLabs discovered a new version of the Tored email worm for Mac OS X, and hackers planted a version of the Jahlav Mac Trojan horse on a website posing as a portal for hardcore porn videos.
Shortly afterwards, the Twitter account of celebrity blogger Guy Kawasaki had a malicious link posted onto it, claiming to point to a sex video of Gossip Girl actress Leighton Meester. In reality, however, the link lead unsuspecting users to malware which could infect Mac users.
https://youtube.com/watch?v=dpnWncJH-bk
Meanwhile, Apple finally began to introduce some rudimentary anti-malware protection into Mac OS X.
Although it wasn’t really equivalent to a true anti-virus product (it only protected against a handful of Mac malware, doesn’t defend you if you try to copy an infected file from a USB stick for instance, and doesn’t offer clean-up facilities), it was still encouraging to see some attempt to offer more protection for Mac users.
https://www.youtube.com/watch?v=rCKciRQQ_8o
2010
The OSX/Pinhead Trojan (also known as HellRTS) emerged.
The backdoor Trojan horse can allow hackers to gain remote control over your treasured iMac or MacBook.
Once again, the malware was distributed disguised as a legitimate application – in this case, iPhoto, the photo application which ships on modern Macs.
More recently, the Boonana cross-platform worm appeared, using a Java applet to target not just Windows computers for infection, but Mac OS X and Linux too.

Sophos detects various components of the attack as Troj/Boonana-A, Troj/KoobStrt-A, Troj/KoobInst-A, Troj/KoobCls-A, Troj/Agent-PDY, Troj/DwnLdr-IOX, and Troj/DwnLdr-IOY. In addition, Sophos’s web protection blocks access to the malicious webpages.
https://www.youtube.com/watch?v=I7RcKVwoNME
Also in 2010, Sophos issued a free home user version of its anti-virus for Macs. We have been protecting business customers who have Macs for years, and now there was a chance for home Mac users to protect themselves against the threat too.
Early reports indicate that there are plenty of Mac users with malware on their computers – some of it is Windows malware, some Mac OS X, and some cross-platform.
There’s no doubt that the Windows malware problem is much larger than the Mac threat – but that doesn’t mean that the danger of malware infection on Mac OS X is non-existent.

