So far in 2016 Android users have seen malware intercept and change URLs in mobile browsers, use Google Talk to call Chinese numbers, and take advantage of steganography to find malicious code to run.
Now they are seeing a new Android trojan load up advertisements and install paid applications on victims’ devices.
On 4 August, researchers at the Russian IT security firm Doctor Web published a description of the virus:
This Trojan, named Android.Slicer.1.origin, is usually installed by other malware programs on a device and executes functions specific to popular service utilities and SEO software.
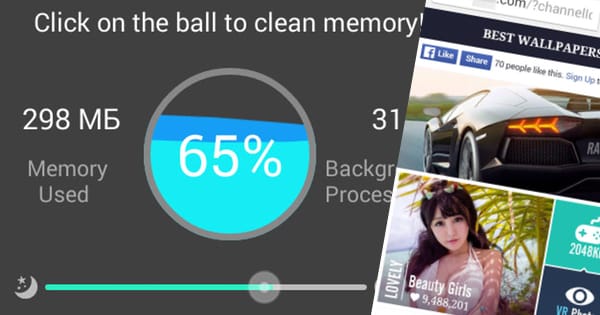
In particular, Android.Slicer.1.origin can show RAM consumption information and terminate running processes. In addition, it allows Bluetooth and Wi-Fi modules to be enabled or disabled. This Trojan does not create a shortcut on the screen, so the user cannot independently launch the application.
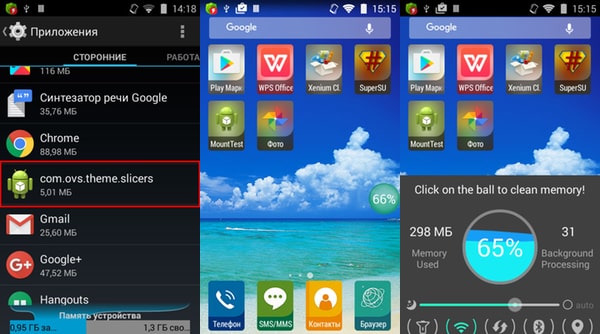
Once it launches, or once the home screen is turned on/off or the Wi-Fi module disabled, the trojan collects the device’s IMEI identifier, the MAC address of the Wi-Fi adapter, and other information and sends it to its command-and-control (C&C) server.
That server in turn instructs the malware to display advertisements and open up advertising pages in a Google Play application or web browser.
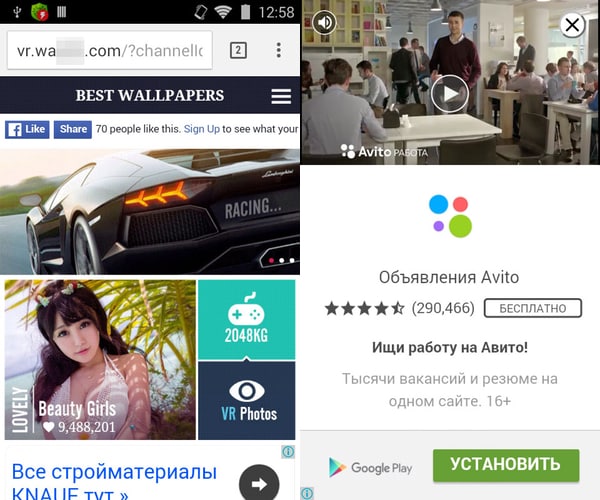
But that’s not all the trojan can do. It can also install other applications, including paid ones, with the help of another virus known as Android.Rootkit.40.
As the researchers explain:
Android.Slicer.1.origin opens a section in one of the specified applications and, using the root privileges of Android.Rootkit.40, runs a standard uiautomator utility. Thus, the Trojan gets information about all the windows and interface elements displayed on the screen at that moment. Then Android.Slicer.1.origin searches for information about the buttons having the identifiers com.android.vending:id/buy_button (“Buy” and “Install” buttons) and com.android.vending:id/continue_button (“Continue”), determines their middle coordinates, and starts tapping them until they disappear from the screen. Therefore, Android.Slicer.1.origin can obey hacker commands to automatically purchase almost any paid software program and download free versions of applications, without the user’s knowledge.
There’s just one catch. The button identifiers needed by the Android.Slicer.1.origin trojan are only found in Android versions 4.3 and later, whereas Android.Rootkit.40 doesn’t work on versions Android 4.4 and later. That means a victim must have Android version 4.3 installed on their device for the trojan to successfully install paid applications.
To protect against this malware, users should download applications only from trusted developers found on the Google Play Store, and consider running a security product on their Android phone.



Dear Mr. Bisson:
Wouldn't it be nice if the only Trojans that existed in the world were the condoms?
Oh well, the earliest computers which could talk to each other had a virus inserted in the punch cards! that said, "have a nice day." I forgot if they were Eniacs Or Univacs. It's morphed into something evil. As some rabbi said in The Talmud: "Satan is constantly digging Hell deeper and wider since so many more people are going there." It is really a shame that this harmless prank morphed into Evil. New credit card comes out with holograms destroyed by exposure to oxygen–don't worry they'll be taken apart in a nitrogen atmosphere using waldoes. Never underestimate the power of the criminal mind which doesn't want to work and hear the the foreman say,"do this, do that, blah, blah, blah."
Sincerely,
Michael Ponzani