Microsoft security experts claim to have uncovered the latest trick being used by Android ransomware.
In a blog post, the Microsoft 365 Defender Research Team details how a new ransomware variant has found a new way to subvert Android’s built-in protection mechanisms to lock devices and hold them to ransom.
The ransomware, which Microsoft Defender for Endpoint detects as AndroidOS/MalLocker.B, is not unusual for Android ransomware in so much as it doesn’t actually encrypt a victim’s files. Instead Android ransomware typically blocks access to an infected device by overlaying a ransom note which blocks out everything else on the device’s display – effectively making it unusable.
Often the ransomware attack will pose as a fake police notice or supposed notification that illegal images have been found on the device, and that a payment must be made to unlock the phone.
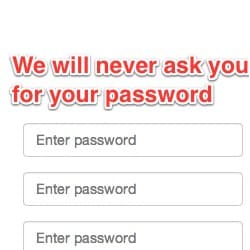
Banking malware on Android has used a similar – but transparent – overlay technique in the past to trick users into entering data into what they believe is a legitimate webpage.
Android 10, released in September 2019, went some way in eliminating these so-called “overlay attacks” but, according to Microsoft, cybercriminals have waltzed around the protections by hooking into how the operating system handles incoming call notifications.

Microsoft says that the MalLocker family of ransomware has a long history of being enhanced, and that it expects new variants to include ever more sophisticated techniques in an attempt to avoid interception.
More technical details about the ransomware and its new functionality can be found in Microsoft’s blog post.