A vulnerability that left millions of AirDroid users vulnerable to phone data hijacking attacks has been patched.
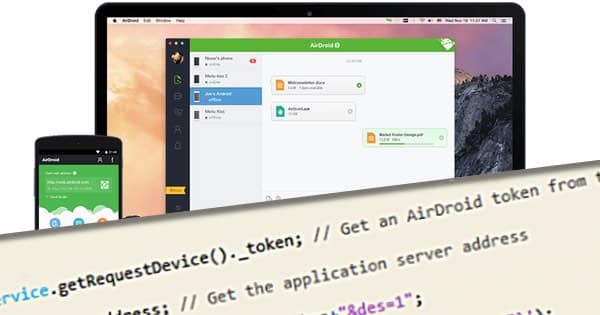
AirDroid is a device manager app that grants Android users access to their devices through their computers, allowing them to manage their Android SMS messages, calls, notifications for other mobile apps including WhatsApp and Facebook, and more. The app is available on Android, Windows, Mac OS X, and via the web.
Approximately 50 million Android users from all over the world have installed AirDroid onto their devices.
According to researchers, each and every one of them was recently vulnerable to a flaw that (if exploited) could have enabled an attacker to steal their devices’ information.

On Wednesday, Oded Vanunu, group manager of security research and penetration at Check Point, published a blog post in which he explains how one of his researchers discovered a flaw (CVE-2015-8112) that allowed an attacker to execute malicious code during an AirDroid session.
Exploitation of this vulnerability was child’s play, according to Vanunu:
“To exploit the vulnerability, a potential attacker simply needs to send the target a text message from a saved contact that is ‘inserted’ inside the AirDroid interface. Attackers can send their targets a seemingly innocent contact card (vCard) containing malicious code via any service (MMS/WhatsApp/email/etc.). All an attacker needs is the phone number associated with the targeted account.”
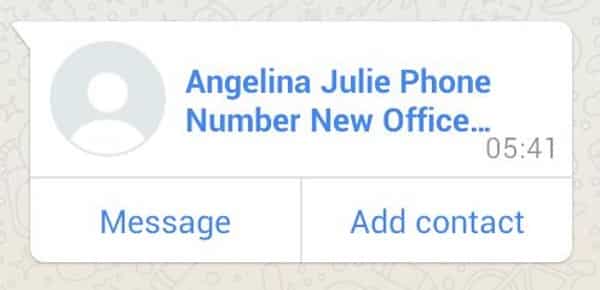
As is evident in the sample malicious contact card above, there’s nothing to tip off an AirDroid user about the request’s malicious intent.
But rest assured, if a user approves the request, all it takes is a text message from the fake contact card for the malicious code to execute on the victim’s device.
At that point in time, the attacker can then get a valid session token and exploit the AirDroid API.

“The AirDroid attack flow provides cybercriminals with a very easy way to target users: sending a contact card and an SMS message to execute the attack. The main threat is a complete theft of private information – imagine, for example, that just receiving an SMS message can result in all of the user’s data being stolen. Another threat is that an attacker could control the content of the target’s device.”
On January 29, 2016, AirDroid released an update that contained a fix for the vulnerability. But as Vanunu is careful to point out, many other flaws that could result in phone data hijacking attacks have yet to be patched or even discovered.
Users are therefore urged to exercise caution when approving a contact request from an individual they might not know or may not be expecting. They should also run a mobile anti-virus solution on their device at all times and be careful to download apps from reputable providers only.