 Adobe has released 69 security updates to address multiple vulnerabilities found in its Flash, Reader, and Acrobat applications.
Adobe has released 69 security updates to address multiple vulnerabilities found in its Flash, Reader, and Acrobat applications.
On Tuesday, the United States Computer Emergency Readiness Team (US-CERT) released a statement urging users and administrators to refer to APSB15-24, one of two security bulletins issued by Adobe in this round of patches.
In that document, Adobe reveals security fixes to approximately 56 vulnerabilities affecting Acrobat and Reader for Windows and Macintosh.
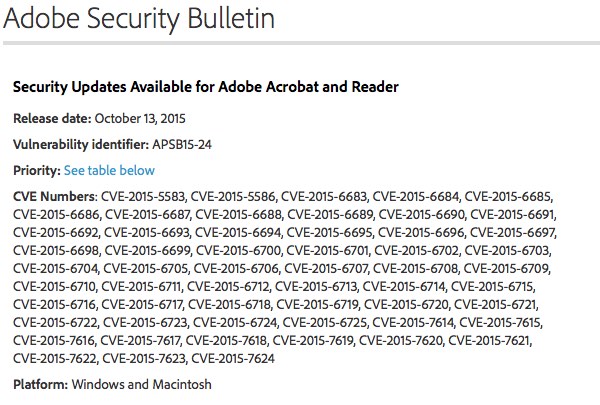
These security holes were discovered primarily by researchers working with HP’s Zero Day Initiative, though experts from Cure53, Vectra Networks, VeriSign iDefense Labs, Trend Micro, MWR Labs, and the Nanyang Technological University in Singapore were also acknowledged by Adobe.
All of the flaws are labeled “critical” because of their potential to allow an attacker to assume control of an affected system.
According to SecurityWeek, approximately half of the bugs constitute various methods whereby a malicious actor can bypass restrictions on Java API execution. Others are security bypass vulnerabilities that could lead to information disclosure, memory leaks, and memory corruption bugs, all of which an attacker can exploit to produce arbitrary code execution.
At the same time, Adobe has released APSB15-25, a bulletin that addresses 13 security vulnerabilities in Flash Player that could lead to information disclosure and code execution.
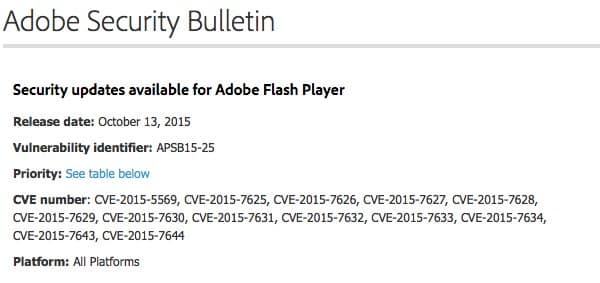
The newly patched version of Flash (19.0.0.207) comes with a defense-in-depth feature in the Flash broker API.
Adobe Flash has had a tough past couple of months.
Back in July, the data dumps that followed the Hacking Team leaks revealed several zero-day vulnerabilities in Flash.
This led Mozilla to temporarily block all forms of Flash before Google’s Project Zero and Adobe outfitted the application with new exploit mitigations.
Adobe has since fixed the Hacking Team bugs in a large patch last month, but as this current patching cycle illustrates, researchers continue to find vulnerabilities in Flash by the dozens.
I would therefore urge you to implement these updates ASAP before an attacker begins exploiting the vulnerabilities in the wild. It might also be worth enabling Click-to-Play for Flash, or disabling Flash altogether.


John Warnock left Xerox PARC and founded adobe in 1982. Postscript was a revolutionary product. I remember struggling to understand what it was as I printed documents on my Epson dot matrix printer.
One does wonder how after 33 years, Adobe cannot fix its products. They are now security cess-pools.
It is time for the world to move on, and abandon all these products…
I understand your meaning but it is unfortunately not even close to simple. You need a replacement and you need all web developers to not use it but the replacements. You also might have to train those people. You then have to have browser support. Oh, and then those programs that use Flash but aren't on websites? Yes, those have to be updated (quite possibly major refactoring) too. All of this comes with a cost (financial) and if one vendor is unwilling to do this, it is difficult for those affected (and much like DNSSEC, too many don't do it because no one else does it – except some DO implement it, of course; I have qualms with DNSSEC but I still have deployed it in any case because it is needed). And we all know security gets far too little concern especially when it comes to finances. Thus we all suffer with this pathetic excuse of software. Oh, and likening it to security anything – even if a cesspool – is far too kind. It is easily one of the examples of software that demonstrate what NOT to do when developing software.
Thanks for the reminder of dot matrix printers! I always loved the sound those make (much like the older keyboards – like the one I'm using at this time). The same goes for modems (though I don't miss the limited bandwidth from them, admittedly). Not that dot matrix printers didn't get jammed – they of course did but printers are problematic regardless of what kind they are (and I frequently feel nostalgic about old computer devices as well as older electronics).
Get used to it. This pile of garbage is responsible for more breaches than can be counted. Both Android and Apple moved on from Flash and the internet didn't blink.
Maybe if we held Adobe financially accountable for every PII record their shitty software exposes, they might get their act together. Until then, it's blocked at the IPS and zero fuch's given.
Specifically with Flash… Trying to 'put out it's fires' is a waste of time for all people concerned.
I suppose you could say it is flammable and often on fire (maybe one of the eternal fires?) but I think it is more like a firestorm (or if you prefer a fire tornado – and yes they exist). Firestorm seems more correct to me (of the two) in that it has its own weather system, but then if you think of one of the alternative names for fire tornadoes – fire devils – then you could maybe say Flash is that too. Whatever you call it, Flash is a complete mess and the sooner it goes the better. But it can't go fast enough and yet sadly it isn't going at all. This affects the security of the Internet as a whole and I find that completely unacceptable. Try telling that to the web developers that rely on it and try telling that to developers of 'software' (I use the term software very loosely; even with the quotes it seems a very poor word to use – it is actually insulting to all real programmers, including myself) relying on Flash. There is no legitimate excuse but they don't care to give an excuse at all.