 If you are using file-sharing systems like Dropbox and Box without proper care and attention, there is a risk that you could be unwittingly leaking your most private, personal information to others.
If you are using file-sharing systems like Dropbox and Box without proper care and attention, there is a risk that you could be unwittingly leaking your most private, personal information to others.
And the risk isn’t theoretical. It’s happening right now – exposing tax returns, financial records, mortgage applications and business plans.
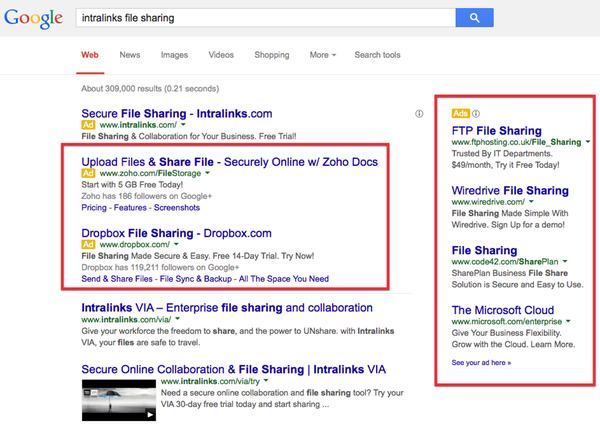
Enterprise file-sharing company Intralinks discovered the serious security issue by accident, when examining its Google Analytics web traffic data and Google Adwords reports.
Like many other companies, Intralinks has webpages, content and – yes, they admit it – Google Ads which are designed with the intention of appearing when users search for the names of their competitors.
Lots of companies do this. It’s the reason why if you Google a phrase like “dropbox secure file sharing” you’ll see ads and links not just for Dropbox, but for competitors too.
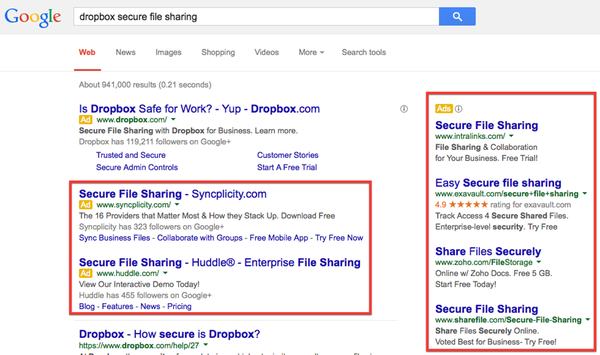
Similarly, if you Google “Intralinks file sharing” you’ll see ads for Dropbox and others.
No-one is saying that this is a bad thing – the sites concerned aren’t pretending to be something they’re not, and it’s just a healthy competitive marketplace at work, informing you of your choices as a consumer.
But, when Intralinks looked at the data from Google Adwords campaigns that mentioned its competitors Box.com and Dropbox, they found something which shocked them: the fully clickable URLs required to access documents stored on the services, including some containing clearly sensitive information.
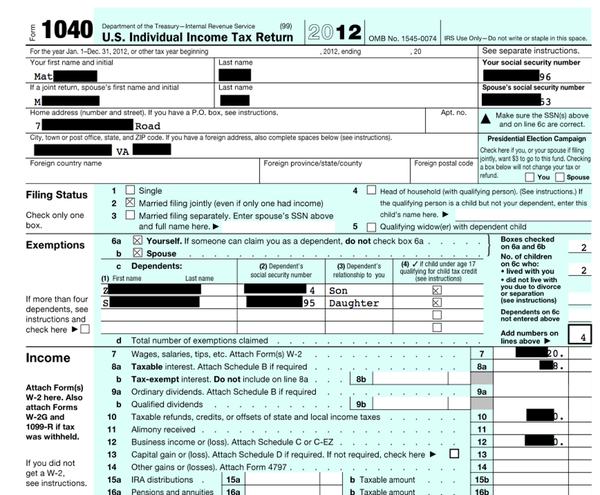
For example, here is one person’s income tax return scooped up from Dropbox. (The image has been redacted below to preserve the individual’s anonymity.)
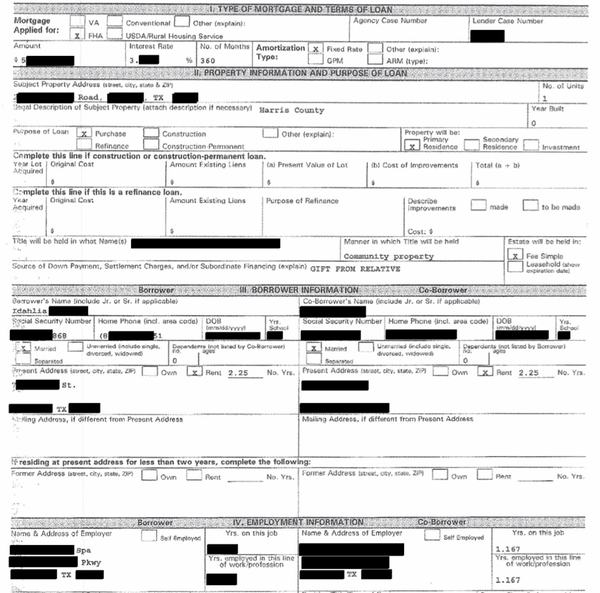
And here is another individual’s mortgage application:
Richard Anstey, Intralinks’s CTO for the EMEA region provided some insight into the scale of the problem:
In one short and entirely innocently designed ad campaign alone, we found that about 5 per cent of hits represented full links to shared files, half of which required no password to download. This amounted to over 300 documents from a small campaign, including several tax returns, a mortgage application, bank information and personal photos. In one case, corporate information including a business plan was uncovered. We also found evidence that many people are mingling their personal and professional files, potentially presenting privacy and security concerns for organisations.
The obvious question then follows: How are Google Ad campaigns receiving these private and highly sensitive URLs, and opening the possibility for unauthorised parties to access confidential data?
Well, here are two paths through which a user can accidentally leak the URL to a folder on Box or Dropbox.
Share link disclosure vulnerability
 Many cloud data storage services provide users with a method to share links with others. For instance, when a user creates a shareable link on Dropbox or Box, anyone with that link can access the data. You don’t even have to be a registered user of the service to access a shared link.
Many cloud data storage services provide users with a method to share links with others. For instance, when a user creates a shareable link on Dropbox or Box, anyone with that link can access the data. You don’t even have to be a registered user of the service to access a shared link.
If a user, attempting to access the document that has been shared with them, puts the Share link into a search engine rather than their browser’s URL box (an easy finger fumble to make) then the advertising server receives the Share link as part of the referring URL, if the user clicks on an ad.
The problem lies in Dropbox and Box not requiring users accessing a shared link to authenticate themselves. It’s clear that for a higher level of security this should be a default way in which the services should work.
As it currently stands, Dropbox and Box share links that were intended for a limited, controlled audience may be disclosed to third-parties.
Hyperlink disclosure vulnerability
 Similarly, if a document stored on Dropbox contains a clickable link to a third-party site, guess what happens if someone clicks on the link within Dropbox’s web-based preview of the document?
Similarly, if a document stored on Dropbox contains a clickable link to a third-party site, guess what happens if someone clicks on the link within Dropbox’s web-based preview of the document?
The Dropbox Share Link to that document will be included in the referring URL sent to the third-party site.
Again, if users had to authenticate themselves in order to access a shared link, this would be less of a problem. But when services do not require authentication by default, users can all too easily begin to leak information.
In summary, share links that were intended for a limited, controlled audience, containing sensitive information may be disclosed to third-parties.
Solving the problem
There is some good news amid all this gloom.
For instance, the Box platform warns users that anyone with the Share Link can access the data. Similarly, Dropbox has a similar message if users review their Share Link settings.
But how many people are aware of the risks?
Advice for Dropbox users
If you’re using the Business version of Dropbox there’s some good news – there is a security setting available to restrict access to Share Links. Unfortunately, there is no such option for the free version of Dropbox used by the vast majority of the company’s users.
As a result, the recommendation for Dropbox users has to be to use the Business version of Dropbox rather than the free one if you share sensitive data via the system. Then, set up the appropriate Share Link security settings to protect your data.
If you use the free version of Dropbox, you should not use the Share Link facility as it could be leaked to a third party.
And, finally, don’t forget to delete or disable Share Links after they are no longer required.
Advice for Box users
Both personal and business accounts on Box have the ability to prevent unauthorised access via Share Links. But these options are not enabled by default.
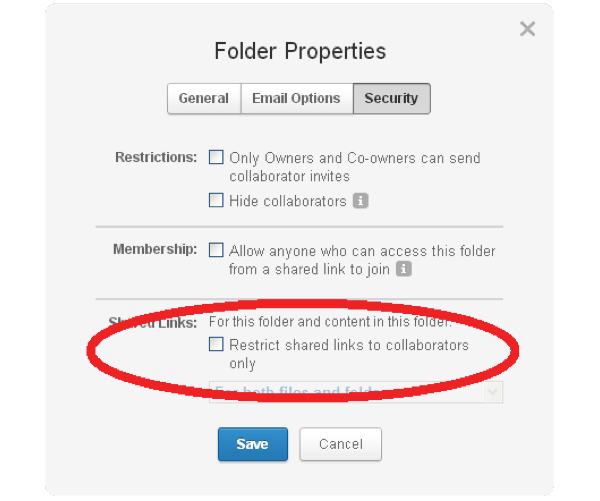
All Box users should change their Share Link security settings to ensure data privacy.
And, finally, don’t forget to delete or disable Share Links after they are no longer required.
Summary
The web is called the web for a reason. It’s a mass of digital strings, connecting sites and information together via links.
As users, corporations and service providers we need to be careful about how we interact with the rest of the web – or risk making it too easy for unauthorised parties to crawl their way into the places we would rather remain private to others.
Further reading:
- Your Sensitive Information Could Be at Risk: File Sync and Share Security Issue
- Dropbox told about vulnerability in November 2013, only fixed it when the media showed interest
Update:
Dropbox has published a blog post overnight about the issue, saying it has taken action against the hyperlink disclosure vulnerability.
In other words, Dropbox has fixed one of the problems, but not the one which revealed the private documents to Intralinks.


Time for Syncthing then http://syncthing.net/ :)
It'd have been nice if Dropbox had told users what they'd done, or better still asked before breaking links – I've just found out about this out from my students who're unable to follow links to their teaching resources (which are not remotely sensitive documents)
Breaking news! If you share sensitive information stored in cloud storage using a link, and a third party somehow receives the link, they can see your sensitive information!!!!!
Really? Is this really news?
Obviously it was news to some people. And the components of URLs are probably way past most users' understanding.
How fortunate I am that so far I've used my DropBox account very rarely and never for sharing links.
The real lesson is that sensitive data should never be shared without being encrypted as well. Yes, that means people need to learn how to use encryption. Welcome to the insecure Internet.
Hi my friend, where can I learn encryption of data?
Many thanks
Sincerely
Dr LAZIN
You mean for encrypting your files before putting them in Dropbox?
Read this article here https://grahamcluley.com/dropbox-privacy/ where I mention some of the tools available, including the likes of BoxCryptor.
Hope that helps
I work for a hosting company, and we've seen something very similar happen with support ticket URLs. The ticketing system we use adds a random series of characters to the end of the ticket URL, so that even if someone wrote a script to try different combinations to find the ticket number, they still wouldn't be able to see the ticket.
However, users accessing the ticket system from a mobile device (in one case a Samsung Galaxy Tab), when they click the ticket link in their email, Google Chrome puts the URL into Google Search, rather than just going directly to the URL. I've confirmed this only happens on a mobile device, and also confirmed with/reported to Chrome Developers.
I realize your view is going to be "security at all cost", but that's far from realistic. We promote user education and security at every opportunity, but when a customer needs support they need to be able to get it without jumping through hoops. Many of our hosting customers struggle with every day things like sending email, a few don't seem to be able to click on a link in an email. Logging into a system is beyond frustrating for some of them, and we end up spending 30 minutes walking them through the process. This is compounded by too many users trying to access services from mobile devices they don't full understand how to use.
We counter this by having a script that monitors the server logs for any access to a support ticket, or a support ticket URL being seen as a referrer (which is how we tracked down the issue with Chrome mobile in the first place). Also all connections are encrypted, though if someone gets a hold of a support ticket URL, encryption really doesn't matter.
It's probably time to reconsider requiring users to login in order to view/reply to support tickets…
Personally I have never trusted Dropbox's security, and only sync and/or share files in it that I would be OK with being public.
I don't think it's just accidentally pasting the link into Google search. You can expose your links to analytics software too simply by clicking from the Dropbox URL to another site where they capture the referral.
Box users who have Enterprise accounts will likely find their default settings are already different: options for the enterprise can set links to default to 'Open', 'Company Only' or 'Collaborators Only'. Obviously the first of these would be a bad choice but changing the default to either of the other two means that links can only leak if the user makes a deliberate decision to share them publicly.
Enterprise admins can even tie the links down even further to block public sharing altogether though this probably negates a lot of the power of the system.
Box and Dropbox by default should have the "No crawl" URL option for their users' account.
Right?
Dropbox and Box are fine for sharing things you don't care if they were stolen. For sensitive info and business records or customer data, I would never trust those services. CertainSafe won the recent Editors' Choice Award for PCMag because its MicroTokenization technology makes data virtually unhackable. I use it to store my passwords and transmit info that I simply would never want a third party to get their hands on. It also is comforting that the former Chairman of the House Intelligence Committee is on their board. Full disclosure, we are the agency for CertainSafe, but it's something I feel passionately about after having used the product as well as others over the years – http://www.certainsafe.com
It is essential to protect our important data from the snooping eyes of hackers even if it is stored it in cloud storage. Therefore it is essential to protect our data with nice encryption software like Data Protecto and AxCrypt.