
Graham Cluley Security News is sponsored this week by the folks at Teleport. Thanks to the great team there for their support!
You’re woken up at 3 am, only to discover your worst nightmare. The new intern just deleted the production database during routine maintenance by accident. You quickly restore from a backup. During the retrospective, you discover that while onboarding, access was provided to all databases, but with full permissions and very similar Postgres URLs, it quickly became apparent that this was an elementary mistake.
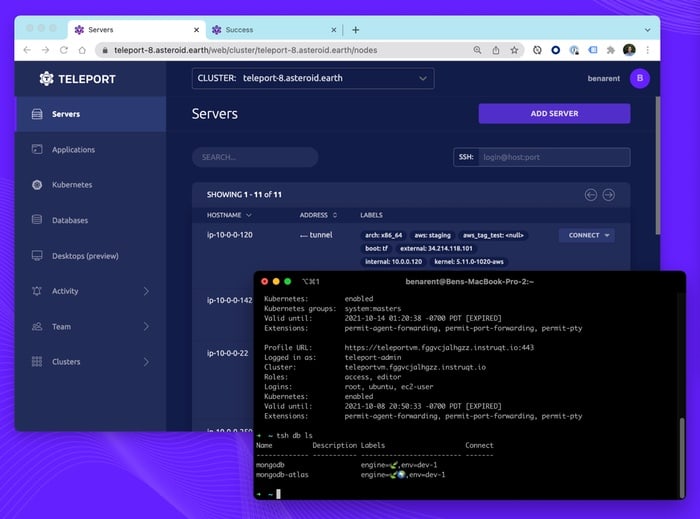
At Teleport, we help people solve these problems. First, we start with making it easy to connect the right resource securely, baking in best practices for bastion hosts and securing endpoints, and making sure to never expose a DB to the internet instead of going through the Teleport proxy. Next up, Teleport Authenticate makes it easy to onboard and offboard users, and Teleport Authorize makes sure that users and machines can perform specific tasks. E.g., Only let the intern read the production DB, but don’t let them drop it. Lastly, Teleport Audit Log provides a stream of structured events that make monitoring and early detection of issues a breeze.
All of this might sound expensive, but all of the above features are available in our free & open-source community edition. At Teleport, we believe the strongest security should be available to all, and if your company has specific compliance requirements or needs advanced workflows, Teleport can help with its Enterprise edition.
Try Teleport
We have a few options to try Teleport. You can start with one of our many getting started guides, or try an interactive demo track for Teleport Server Access & Teleport Kubernetes Access.
If you’re interested in sponsoring my site for a week, and reaching an IT-savvy audience that cares about cybersecurity, you can find more information here.