Many thanks to the great folks at Orca Security, who have sponsored my writing for the past week.
You’re probably familiar with the shared responsibility model. The basic idea is that public cloud providers such as Amazon Web Services (AWS), Microsoft Azure, and Google Cloud Platform keep their platforms secure, but customers are still responsible for securing the workloads, data, and processes they run inside the cloud – just as they do in their on-prem world.
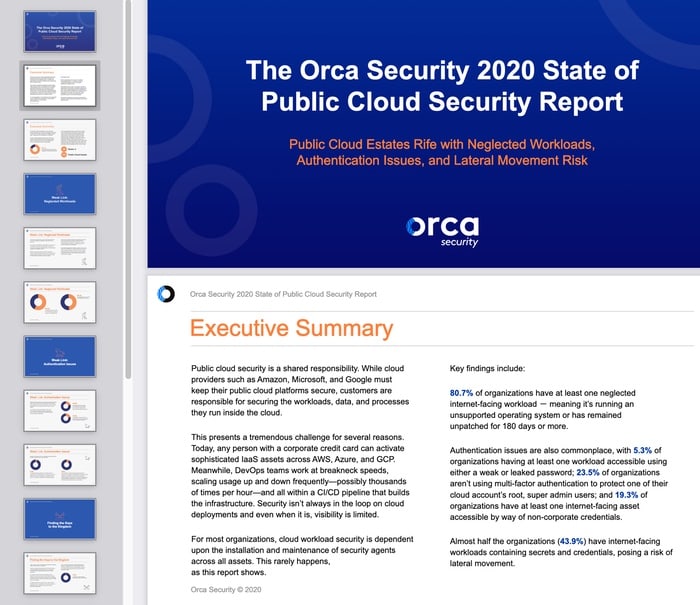
The world of cybersecurity isn’t fair. Security teams need to secure everything, but attackers need only find one weak link. For most organizations, cloud workload security is dependent upon the installation and maintenance of security agents across all assets. Something that rarely happens, as Orca Security’s new report reveals.
For instance, 81% of organizations have at least one neglected internet-facing workload.
Download the free report now (no registration required) to:
- Find out how your public cloud security posture benchmarks against your peers
- See the weak links and exploitation paths attackers are looking for
- Identify the most common authentication issues hiding inside public cloud estates
- Get four key recommendations to avoid a major breach
Orca Security provides cloud-wide, workload-deep security and compliance for AWS, Azure, and Google Cloud Platform - without the gaps in coverage, alert fatigue, and operational costs of agents.
Connect your first cloud account in minutes and see for yourself. Try the demo for free today.
If you’re interested in sponsoring my site for a week, and reaching an IT-savvy audience that cares about cybersecurity, you can find more information here.