How hunting for an aubergine could be all it takes for you to hand your credit card details over to a scammer, and just how good is a podcast entirely built by AI?
All this and more is discussed in the latest edition of the “Smashing Security” podcast by cybersecurity veterans Graham Cluley and Carole Theriault.
Warning: This podcast may contain nuts, adult themes, and rude language.
Listen on Apple Podcasts | Spotify | Pocket Casts | Other... | RSS
More episodes...
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
God, your life, man. Our listeners are crying for you. Their tears are just spilling down their faces as their hearts break at how hard your life is.
Smashing Security, Episode 344, What's Cooking at Booking.com, and a podcast built by AI. with Carole Theriault and Graham Cluley.
Hello, hello, and welcome to Smashing Security episode 344. My name's Graham Cluley.
And I'm Carole Theriault. Hello, Carole.
That's very kind of you. Hi, Graham. How are you? I didn't say anything kind. I just said hello. I'm all right. Thanks. Not too bad. It's
all it takes. It's all it takes, Graham.
I'm particularly pleased, by the way, to our listeners this week. Yes. Last week on the Pick of the Week, I spoke about my friend Ali, one of our old colleagues. And she is raising money for Mind on her JustGiving page. And can you believe when we recorded that, Carole, Ali had raised £500. And in the space of a week, thanks in no small part to the generosity of Smashing Security listeners, she's now raised over £800. Wow. Isn't that incredible? Isn't that fantastic?
You know, that's so nice that we have a good community. Yeah. If you're one of those people, high five.
I know it means a lot to her. And it means a lot to us as well. So thank you to everyone for being so generous supporting Ali's JustGiving. You're amazing. Shall we get on with the show? Let's do it.
But before we kick off, let's thank this week's wonderful sponsors, Collide, Devo and Vanta. It's their support that help us give you this show for free. Now, coming up on today's show, Graham, what do you got?
I'm going to be looking at booking.com. What was that a play on words of? Just a little rhyme.
Okay, right. Okay. And I'm going to be asking a very important question. Are we out of a job? All this and much more coming up on this episode of Smashing Security.
Now, let me take you back in time to last Friday night. I was at home with my partner and we had to, you know, we were going to do a bit of cooking. And she said, what do you fancy eating? I said, I don't know. What do you reckon? Did you say hamburger filled pizza crust pizza? No, I've never. Have you seen that? It's fucking unbelievable. Jesus. Well, hang on. Well, you stuff hamburgers into the crust. Yes. It's so gross.
I think it's from Domino's or Papa John's or one of these. But yeah, you have these burgers. There's 12 burgers around in your crust. What? Yes. Tiny burgers. What are those things called? Americans are listening or yelling at me right now. Yeah, the little burgers you get them on a plate, you get five of them. Yep. I'm waiting for the emails and the tweets.
Anyway, we came up with an idea which was ratatouille. I love a bit of ratatouille. It's not only a fantastic animated movie, it's also a wonderful dish as well. So I was sent to go and hunt and gather the ingredients for a ratatouille. And so I went to my local supermarket with my little shopping bag and I was going up and down the vegetable aisle. And of course, one of the key ingredients for a ratatouille is an aubergine, right?
Eggplant for our North American listeners. Is it? Is an eggplant?
I know the Americans call something an eggplant.
Eggplant and aubergine are the same, yeah. They're the same thing.
Courgette and zucchini are the same thing as well.
Okay, right. Stop right there. Stop right there. Okay. Because that is my mental block. You have identified it. It's the aubergine. It's the courgette. It's the zucchini. It's the eggplant. In my head, they are all one vegetable. I know they look different, but in my head, I can't picture them differently.
I can't picture how you're gonna get this story onto technology. That's where I'm stumped. I'm trying. I'm trying to find an aubergine. And I haven't, you know, oh my goodness, where am I gonna find aubergine?
You don't know what you're looking for. You don't even know that they are actually aubergine coloured. Do I? Well, it's kind of a big giveaway on that fruit, an orange, you know?
And it's not an orange at all. It is. An orange is orange and aubergine is aubergine. Oh, I see. Okay, but it's not an orange in the other way. Anyway, the point is that normally when I am stuck with this sort of challenge, I might reach for my phone because heaven help me, I'm not going to go and ask an assistant, right? That's far too embarrassing.
Yeah, or God, it seems because.
I can't. So normally I would reach for my phone. I think I'll just do a quick Google image search to remind myself of what I'm looking for here. Oh, that's what I know, right? But I can't because I've got lousy cell phone coverage in my supermarket. There's no cell phone coverage. So I can't use my phone. There's only one little bit where there's the tiniest sliver of a bar on my mobile phone. You don't want to use their Wi-Fi or something? What kind of supermarket are you going to where they have Wi-Fi for shoppers? They want people buying things, not playing Candy Crush. No, they don't have Wi-Fi. God, where do you live? Anyway, so if I'm by the tills, there's a sight of sliver of cell phone coverage, just a tiny little bit, a bit like you're in the middle of Alaska. That's the kind. Imagine that. Imagine you're halfway. It's not that hard. I'm with you. Anyway, right. Okay. So I head over there thinking, oh, maybe I'll be able to just see, you know, if I get there. And at that point, my watch, right, I've got a smartwatch. Of course you do. It gives me a little notification.
Do you have smart earrings as well?
I don't have, no, I don't have anything. Just have a watch, which normally reminds me of my calendar where I'm supposed to be. Am I recording a podcast at three o'clock or four o'clock today? That kind of thing. And it pops up and I'll take a look at it. And it is a notification from the Booking.com app, right? Which is the online travel agency where you can book your hotel. So you have the app
installed on your phone and it pings you.
Well, it came up on my watch, which I didn't even know. I've never seen anything before. Right. But I think it's because I had the app on my phone, it synced up with my watch. And so I got the notification on my watch that Booking.com says there's a message for you. And I'm thinking, oh, well, I do have an upcoming hotel trip. Right. Because I'm doing a talk in London in November and I had to book a hotel. And it was a real pain and for one reason or another I had to use Booking.com which I don't normally use and I installed the Booking.com app onto my phone blah blah blah did it do this and yada yada yada etc etc and I booked it as normal and I got a notification at the time of booking from the hotel saying thank you very much Mr. Cluley you know we have booked you in and all the rest of it and there's this little messaging facility so I could chit chat back and forth with the hotel if I wanted to, saying, oh, can you make sure that, you know, my pajamas are creased, or whatever it is that I want to. I never use that thing, ever, ever. Right. It's how can I help you, sir? Not a bot. That kind of thing. But it's actually a communication from the hotel. So this is a way for the hotel to talk to me without sending me an email, which is kind of good, because that's all happening inside the Booking.com app.
Right. Okay, that's fair. Rather than via email. Right, right, right. Because if it did come via email, you might think, aha, what is this? Is this some kind of phishing email, right? But if it's coming from inside the Booking.com app, you think, well, I have booked this via Booking.com. Therefore, I get a message from Booking.com.
And you're oh, FFS. I just want my hotel room. I've already sorted it out,
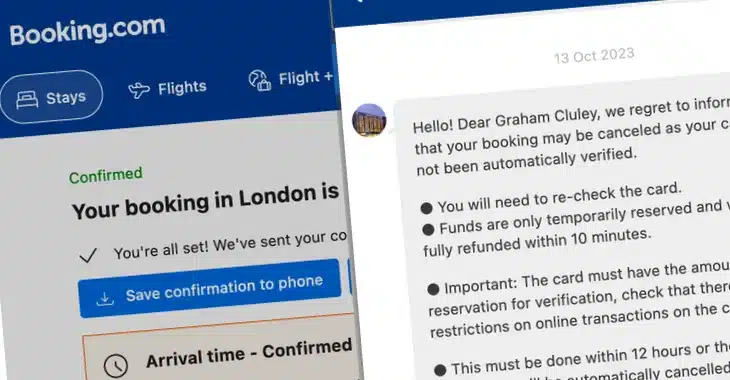
I thought. I just want an aubergine, right? I just want an aubergine. And it includes a link. And the link goes to booking.com-id334-112.com slash p slash 965664712. Right. Very useful. Yeah, yeah. And this has arrived via the Booking.com app.
It feels very legit. Except, you know, you've got a booking in your mind that you've tried to do. It's come through the app and they're saying no. And this is a message and it says it's from the hotel where I have indeed booked this. And I can scroll back and see previous messages from the hotel that they have legitimately sent me. And the link looks kind of legit, at least on my mobile phone. And so I think, oh, crumbs, I've got to keep that hotel room because it's going to be a nightmare if I have to try and book another one again. So I click on the link, but the link doesn't work because by now I've walked back into the vegetable department of the superstore.
Every week, our listeners are crying for you. Their tears are just spilling down their faces as their hearts break at how hard your life is.
So, exactly. I know. So, I wait until I get home. I'm a bit, but you know, because of my lack of connectivity, I haven't been able to act on it on impulse. I've had a little bit more time to think about it. And I think well I wonder what this is about so I managed to eventually find the aubergine and I get back home and we eat ratatouille and it was delicious thank you very much for asking but having done that I then thought well I better look into this thing because they said I only had 12 hours but now I'm suspicious and I'm looking again at the link but why are you suspicious Well, because what I noticed was the URL said booking.com. This is how it looked anyway, booking.com-id334112.com. So the actual domain name was not booking.com. Slash 1255. Yeah, yeah, yeah. It was com-id334112.com. But the way it appeared on just casually looking at it and in the context of inside the Booking.com app, it looks like it was a legitimate link. And it turned out, of course, that it wasn't. So me with my cybersecurity hat on thought, oh, what is this? This seems all actually this seems kind of fishy. And when I went to the link, it looked like the real booking.com site, which had pre-filled in on it some of my details regarding the hotel I was staying at, regarding my name, yada, yada, yada. So I thought, I wonder how the bad guys have done this. So
The only thing that gave it away to you was the crazy URL. So it was like a, yeah. I
Mean, it was a bit strange that they were asking me to re-verify my card. But because that hadn't arrived via email or an unsolicited text or something like that, because it was inside the app, inside the actual booking app I had used, I was, I have to say, I was, you know, tricked. Not tricked so much that I actually entered my data, because thankfully my spider senses kicked in. Yeah, but you
Looked into it. You thought, let me just see if this is.
But I could well understand how anybody else would fall for something like this. So is this a screw up from Booking.com? Well, this is what I wondered. I thought, what's going on here? How has this happened? And so I think I need to contact Booking.com. That must have been easy. First thing I do.
I bet that was a cinch. No problemo. They pick up right away.
So there is this thing called a security.txt file, right? Which websites are encouraged to create, put on their website. I've got one on my website. So there's a standard place you can go to on a website to get the contact details to tell people about a vulnerability or a bug or something like that, how to make contact. So I look for one on Booking.com site. There is not one there. Right? There's not one there. So I post up on Mastodon and Twitter and some other sites as well. X. People who follow me. I'm not calling it X. People who follow me saying, has anyone got a security contact at Booking.com? And then, of course, you've got all these replies going, oh, I bet they've had a data breach. You know, people jump into conclusions as to what's happened. Oh, outrageous of them. You know.
The humans. On a platform where there's 300 characters and you're supposed to have an opinion. How dare they? You know,
It's anyway. So people are making that assumption, which seems a reasonable assumption to me. Right, exactly. As to why would I be asking. And I tag Booking.com, by the way, in my tweet. And I get a reply from Booking.com. Not the real Booking.com, of course. I get a reply from a fake Booking.com on Twitter. And trust me, I've found out since that there are numerous ones because they've been tweeting me ever since, trying to help with my Booking.com issues. So it's a freaking... I'm reaching out on LinkedIn as well, trying to find security contacts in my network. And I find a couple. I do eventually get a reply from one of them who tells me basically to bog off. Do you
Know, why not just call a hotel directly from now on? There's wonderful people, concierges that are there to help you and just go, hello, I would like to book a room. Eventually, I get an email address, thesecurityteam at booking.com. Okay, so I email them. I give them the details, I give them screenshots. Say, hey, this seems pretty serious. I imagine if this is happening to me, it's happening to other people as well. Yeah, it's not fair. I mean, how can people do that? I'm wondering whether we should say, hey, if you work in the hospitality industry and use booking.com, I don't know, maybe it's a good time to change password. Just see what happens.
Absolutely. And I don't know if a two-factor authentication is available with those accounts, but if it is, turn it on.
Yeah. You know, the problem I bet is, though, is that there's going to be multiple people having access to it to manage it. And somehow the technology industry has not figured out a way to have...
So you are right. When you've got a team of people logging into the same account, then two-factor authentication can be a bit of a pain. What I've experienced is if you use a good password manager, you can now get the password manager to generate the time-sensitive one-time password. And if you're sharing those details inside your password manager in a secure way, they can also access the two-factor token as well. That's a super good point. In order to enter it. So maybe another reason to get a good password manager inside your organisation. Loads of good advice. Interesting. Anyways, Ratatouille. Great. Love it.
Great. Now you know what an aubergine is. Don't ever use the emoji, though, unless in an iMessage.
I think I'm more of a chipolata man. If I'm lucky. With a good wind behind me. Carole, quickly, moving on. What have you got for us this week?
Graham, I don't even know how long it's been. Five years, almost 350 episodes worth. We've been creating this award-winning podcast. It's actually longer than that. Do you know our first episode was in December 2016? 2016. We are coming up to our seventh birthday. Jesus God. Is that not right? I have no idea. I think that's correct. Is it fair in saying that we can boast about 10 million downloads or listens? Is that about right?
Oh, I haven't been keeping count, but yes, it's something like that. Yeah, it's pretty impressive, you know, more than a million a year. Anyway, I thought we could work out roughly how many hours we have spent so far on Smashing Security, just for fun. Okay, so I've done a little breakdown. You just correct my numbers here and see what I think.
Okay, so combined, yeah, combined, I guess we come up to about two hours. Eight minutes, I suppose, yeah. Oh, you only do eight minutes. But I think it's obvious, isn't it?
And then in the editing side, and all that stuff, reviewing, listening to your half, you listening to my half, all the stuff, I would say that's about four hours on average for me.
Yeah, I think it's probably a bit more for me.
Yeah, you probably have five. Okay, so we add all that up, what, we've got 9, 10, 11, basically 12 hours, right?
Yeah, we've wasted a large chunk of our lives doing this, yeah.
12 hours times 2, because 12 hours for me, 12 hours for you each week. 24 times 345. You could do the calculator, because I'm doing the story. Oh, okay. It's actually episode 344 today, I think. There we go. Yeah, don't exaggerate our numbers. So I've got 24 times 344. Okay. So that is 8,256 hours. Jesus. If we were a two-headed beast, Graham, we're almost there. Divide that by 24 just to get a number of days. 24-hour days that we've been doing this stuff.
I think it's divided by 24. 385.
385 24-hour days so for more than an entire year no sleep.
No, no, going to the loo, no.
Going to the loo, well let's take your phone and do some editing, no eating ratatouille. Yeah, it's a lot of time, it is a lot of time. That's a lot of time. Listeners, I'm not trying to say poor us, right? We have amazing wonderful sponsors that help make this all worthwhile and they're great and thank you and our Patreon supporters and everybody. But imagine, Graham, imagine if we could just sit on our cute little tushes and get someone else to do all the work for us virtually for free, right? There'd be a lot more profit at the end of that. We'd be quits in. That would be wonderful. Eat our cake and... What's that expression, get your cake and eat it too? I've never understood that. Why would you want a cake and not eat it? Anyway. Worry not, Graham, because get ready, because we found a podcast that has been entirely AI generated, or so Develop AI claim. This is a company that reports on AI in Africa, trains African journalists to code, to work with AI tools. And I'm guessing this was a bit of a PR stunt to get some eyeballs. And it worked because look at me today, I'm talking about it. I looked into this, right, and I wanted to see what the plan was. And they wanted to get a working script that would spit out a complete 10-minute podcast episode recounting the daily news, in this case from Johannesburg where he's based, in a discussion format between three trained imaginary voices.
Oh, so it's not just coming out with a script. It's actually then got AI bots reading it. Yeah, basically I'm giving you the highlights of his article. The link is in the show notes if you want to read more about it. Guy's name is Paul McNaley. Paul has a dream. He has a dream. He writes he says he has a dream of building an application that could produce a podcast episode from scratch without even needing to record a human voice. That was the big plan, right? At making up stuff. Yeah, exactly. So I love that he's, instead of just creating a podcast full of shit, he's we're gonna do the news. We're gonna do the news with something that's really good at creating imaginary narratives. This is awesome, right? Oh my goodness. Don't you feel they slightly copied our idea? Because we have a synthetic robot voice at the start of the Smashing Security podcast. You're welcome, Paul. There's no reason why we couldn't get the chap who goes "episode 300," you know what he does, all that stuff with Graham, to tell a whole story, to do the whole thing. I mean, we could take a holiday. We can just get him to do it. Would anyone even notice?
What's his name again? I always forget his name.
Let's call him Dave. I don't know.
Maybe Dave will close the show today with something. We'll see what he can do. And we've been doing that since when, 2017? So put that in your hat, Paul. Okay, so the snags in this project of his. The cost of synthetic voices charged per character, he says, was too high because he says in his mind he envisioned this kind of dystopian factory of 100 podcast episodes a day being produced, right, with no one even listening to the content before it's published. And he says the costs make that impossible. And I'm thinking, okay, they may be expensive now, but I imagine in a few years' time it'll be a dime a dozen. Don't you think?
And is it really? I mean, maybe it's expensive if he's using some sort of cloud-based service to do this, but surely he's got some old Bitcoin mining rigs down there in Johannesburg which he could adapt to get to work on this project instead.
The other thing was his issue was the speed of production for each episode wasn't as quick as he anticipated or hoped.
Oh, how long does it take?
So what he had budgeted for, what do you think was for a 10-minute three-character blah blah about the news?
Is he thinking he could do 20 minutes in an hour? He's budgeted two minutes per episode. So what? Two minutes to produce 10 minutes of audio. I'm actually impressed by that. I thought it would take longer than that. Well, there's a third snag and this is maybe the most important for us. He says is it libel, lawyers? Yeah, but he's publishing it, isn't he? He's saying it's AI produced, though. He seems to be pretty clear on it, although yes, he should probably review the content before he's published, never mind. Yeah. Do you want another third snag?
Go on. I'm going to quote him here. Quote, unforgivingly boring. Unforgivingly we all know about that and he says because as someone who creates podcasts for him it was a relief.
Captivating indeed, but just to temper the excitement a bit, let's remember Alice operates on X. She uses a traditional newsreader's voice to deliver news bulletins. Sounds like a glorified radio to me. SPEAKER_02. You have a point, Will, but isn't the level of technical advancement astonishing? I think it's pretty impressive. And you said, it's just going to get better and better, isn't it? Even if the jokes don't.
You have a point, Graham. Thank you to Smashing Security sponsors Vanta, where you can shortcut compliance without shortchanging security. Expand the scope of your security program with Vanta's market leading compliance automation. Vanta's 5,000-plus global customers report saving over 300 hours in manual work and up to 85% of cost for SOC 2, ISO 27001, HIPAA, GDPR, custom frameworks, and more. And with Vanta's 200-plus integrations, you can easily monitor and secure the tools your business relies on. From the most in-demand frameworks to third-party risk management and security questionnaires, Vanta gives SaaS businesses of all sizes one place to manage risk and prove security in real time. As a special bonus, Smashing Security listeners get a whopping 20% off Vanta. Just go to vanta.com slash smashing. That's V-A-N-T-A dot com slash smashing. And we thank Devo for sponsoring the show. SOC analysts are often overworked and underappreciated. In fact, many consider leaving their jobs or changing careers altogether. Devo is hosting the third annual SOC Analyst Appreciation Day. This year's program includes presentations and discussions from some of the InfoSec community's most prolific thought leaders, including the likes of YouTube creator John Hammond, CISO Olivia Rose, and unpopular opinion guy Joss Copeland. This event will cover everything from real-life use cases to SOC automation, managing your mental well-being, and more. You won't want to miss it. Join Devo and other cybersecurity industry professionals on October 18, 2023 for sessions and panels focused on de-stressing, SOC career development, and more. Visit smashingsecurity.com slash Devo to register. That's smashingsecurity.com slash Devo. If you work in security or IT and your company has Okta, this message is for you. For the past few years, the majority of data breaches and hacks you read about have something in common. It's employees. Hackers absolutely love exploiting vulnerable employee devices and credentials. But imagine a world where only secure devices can access your cloud apps. Here, credentials are useless to hackers, and you can manage every OS, even Linux, from a single dashboard. Best of all, you can get employees to fix their own device security issues without creating more work for IT. The good news is, you don't have to imagine this world. You can just start using Collide. Collide is a device trust solution for companies with Okta. And it makes sure that if a device is not trusted or secure, it can't log into your cloud apps. Visit collide.com slash smashing to watch a demo and see how it works. That's K-O-L-I-D-E dot com slash smashing.
And welcome back. Can you join us at our favorite part of the show? The part of the show that we like to call Pick of the Week. Pick of the Week. Pick of the Week. Pick of the Week. Pick of the week is the part of the show where everyone chooses something. It could be a funny story, a book that they've read, a TV show, a movie, a record, a podcast, a website or an app. Whatever they like. It doesn't have to be security related necessarily. Better not be. Well, the real rule, Carole, is it doesn't have to be security related. Not that it better not be security related. Only if you think a man's rule is more important than a lady's rule. I think whoever speaks first sets the rules in this particular case. So you start the podcast. Doesn't have to be. Look, my pick of the week this week is security related. Is that all right with you?
Thank you very much for asking. It is fine with me. Thank you. Go ahead. Please proceed.
My pick of the week this week is something which has been made by Ryan Kovar. He is the distinguished strategist at Splunk. And he has put together an online map where he's coloured different countries according to whether it is legal to pay ransomware gangs or more specifically cyber extortion gangs or not.
Oh my God. So this is used by corporations everywhere. So instead of asking their legal team, they can go, I can find out. Don't worry, don't worry. I'll just check this.
We'll work out where to make the payment from, which country. Have we got a division in Mongolia? Right, they're the ones who are going to pay it. Oh, my God, the world. So if you go to isitlegaltopay.com. Oh, my God. Okay, I'm going right now. The first thing you will notice is it isn't protected with HTTPS. So it's HTTP, which means your browser. Well, you're not putting any information in, are you? Yes, but come on. This is Ryan Kovar, a distinguished strategist at Splunk. Surely he can get Let's Encrypt to produce a SSL certificate free for his little website. I felt embarrassed linking to it in the show notes.
Well, then don't. I'm not sure he'll care. You don't have to give him a lecture. Well, I just found it. Anyway, that's the first thing that you'll stop. You were surprised to see that it's on HTTPS. Although, actually, I'm seeing right now it's HTTPS. My site's HTTPS. Is it? Yes. Are you sure? Well, I'm looking at it and it says HTTPS. So he's just got a tiny little niggle. No problem. So I've made a big thing about this. Yep. The aubergine. Ryan now hates me. Just exactly the same thing. So he's building out the database.
Yeah. Exactly. And you can contribute to this via a GitHub page. It's linked to from the site. Because some countries do say it's a bad idea to pay ransomware gangs because you could be funding terrorism. Others simply say, no, you cannot, full stop, do it. The only place marked in red at the moment where you definitely cannot pay your ransomware is in North Carolina, where apparently state agencies and local government are prohibited by law for paying ransomware demands. In some other places, you have to report it. But I think this is kind of interesting, and I think it will grow over time. Canada, do what you like. UK, do what you like.
Yeah, France, do what you like. Australia, do what you like. South Africa, do what you like.
Although, if you click on some of these countries, you will find a little bit more granularity. So they may say, although it's not illegal, it's strongly discouraged or you have to, in some places, you know, there may be additional rules. There's certain criminal. What the website says is, look, I'm not a lawyer. I'm not Judge Judy. Do not take this website. If you are thinking of paying a ransom demand, go and consult proper legal advice regarding whether what you're doing is right or not, because otherwise you could end up in a bit of a pickle.
I'm just having fun while I have, you know, cereal.
Yeah. So one other thing, Carole, which ties in with your story just now, is I went to the about page for isitlegaltopay.com. And it says that the entire website was written with ChatGPT. So the data is being collected, outsourced from the, you know, people are contributing the data. But the actual website is written by AI, which might explain, if you do go to the About page, it sort of glows in this menacing green. It pulsates a bit like a giant maggot, which has been infected by some sort of mutation. But anyway, that might be ChatGPT, which has chosen that. But anyway, isitlegaltopay.com is my pick of the week. All right. Nice work, Ryan. And remember to use HTTPS. Such a bobo. Carole, what is your pick of the week?
My pick of the week this week is a movie. Oh, yeah. It is called Licorice Pizza. It was created by the creator of Boogie Nights and Magnolia, Paul Thomas Anderson. And it came out last year, November 21, but I really think it's destined to be a cult classic of a genre, the coming of age movie. I saw it last night. So I got it on BBC iPlayer where it's available at the moment. And it kind of underscores the sweet pleasures, but also the nasty heart wrenching pains associated with infatuation at a tender age. So we're in 1973 and you have this 15 year old kid. And he reminded me a bit of you, Graham.
Is this the character of Gary I'm looking up right now?
Yeah. There is a physical resemblance.
I don't know. Not about looks. No, not about looks. Not about looks.
Not about looks. Listen, just listen first, right? So he's been killing it as a child acting star, child acting star. But he's getting old. He's 15. Right. You know, and he doesn't fit into that world anymore. And you can see the writing on the wall. But this is where he meets Alana. And Alana is the photographer's assistant or something, but is 10 years his senior, Graham. So she's 25.
I'd have quite liked that when I was 15.
I know. And he's kind of got all completely swoony over Alana. And he's also a very determined kind of person, a bit like you are. Like, you know, when you say, I'm going to do this, you just go for it. So rather than wallow or fight back about his acting career, he changes tacks completely and embarks on a little venture, flogging water bed mattresses. And it's crazy. And he's got charisma and charm, which means his mates and siblings are all involved in his venture as he navigates the world of marketing and buying and selling for the first time with all these adults around. And then there's more ventures that happen when there's a bill that's reversed. He seizes the opportunity to capitalize, right, to be the first person in town to offer a specific type of service. And so we have this zany, determined, savvy kid. And she's kind of curious about him, but kind of can't believe he's 15, but just is also kind of intoxicated by him because he's kind of fascinating.
That's a little bit awkward feeling, though, if she's 25, if she's. Well, you know, that's kind of my issues. They called it puppy love, but a mature one. I've just been looking at it. According to what I'm reading here, you can't stream it anywhere at the moment. So maybe BBC iPlayer is the place for now. I guess you can pay for it on somewhere like Amazon Prime Video. So, you know, but you can't stream it for free at the moment. Anyway, he's made some other good movies, hasn't he, Paul Thomas Anderson? Boogie Nights. Magnolia.
Yeah. Magnolia.
Yeah, that was... Magnolia was very long. God, that was long. Thom Cruise, wasn't it? It was like three and a half hours or something. Anyway, that just about wraps up the show for this week. You can follow us on Twitter at Smash Security. No G, Twitter on NLWG. We also have a Mastodon account as well. Don't forget to ensure you never miss another episode. Follow Smashing Security in your favourite podcast app, such as Apple Podcasts and Overcast. Massive thank yous to this episode sponsors, Devo, Vanta and Collide. And of course, to our wonderful Patreon community.
Until next time, cheerio. Bye bye. Bye. All right. Excellent. Very good. Fun story. Well done, Carole. You should watch it with Miss Amanda as well.
Yeah. Maybe we shall. I think you're going to want to hide a bit. A bit close to home. It'll be a little close to home, but it's not embarrassing. He's very sweet. He's a really, he's actually, he's kind of the star character. He is a really good character. And you're going to be waiting for something awful. There's nothing awful. He's just, but it's just, anyway, it's really great. I really love it.
Here's a cyber security joke that uses AI. Why did the AI cross the road to get to the other side of the firewall? Ha ha ha. I hope that made you chuckle.
Hosts:
Graham Cluley:
Carole Theriault:
Episode links:
- Support Alie Hothersall’s fundraising for Mind – JustGiving.
- Fraudsters target Booking.com customers claiming hotel stay could be cancelled – Graham Cluley.
- Security.txt – A proposed standard which allows websites to define security policies.
- Develop AI launches a completely synthetic podcast – Develop AI.
- Develop AI podcast.
- Is It Legal To Pay – The err.. https version of a map of which countries allow you to pay ransom demands.
- Licorice Pizza – BBC iPlayer.
- Smashing Security merchandise (t-shirts, mugs, stickers and stuff)
Sponsored by:
- Kolide – Kolide ensures that if your device isn’t secure it can’t access your cloud apps. It’s Device Trust for Okta. Watch the demo today!
- Devo – Register now to join Devo and other cybersecurity industry professionals on October 18 for sessions and panels focused on de-stressing, SOC career development, and more!
- Vanta – Expand the scope of your security program with market-leading compliance automation… while saving time and money. Smashing Security listeners get 10% off!
Support the show:
You can help the podcast by telling your friends and colleagues about “Smashing Security”, and leaving us a review on Apple Podcasts or Podchaser.
Become a supporter via Patreon or Apple Podcasts for ad-free episodes and our early-release feed!
Follow us:
Follow the show on Bluesky at @smashingsecurity.com, or on Mastodon, on the Smashing Security subreddit, or visit our website for more episodes.
Thanks:
Theme tune: “Vinyl Memories” by Mikael Manvelyan.
Assorted sound effects: AudioBlocks.