
Security firm Webroot drops a clanger when it declared Windows was malicious and borked customers’ PCs, millennials are streaming a lot of movies illegally, and blackmailers are targeting members of the Ashley Madison cheating site again.
All this and more is discussed in the latest edition of the “Smashing Security” podcast by cybersecurity veterans Graham Cluley and Carole Theriault, joined this week by special guest Michael Hucks from PC Matic.
Listen on Apple Podcasts | Spotify | Pocket Casts | Other... | RSS
More episodes...
Show full transcript ▼
 This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
This transcript was generated automatically, probably contains mistakes, and has not been manually verified.
Before we begin the show this week, I want to give a quick shout out to our sponsor, Recorded Future, a threat intelligence company, and they really sort out the signal from the noise. There's so much information out there in so many places about what's going on in the world of cybersecurity. You need some experts to sift through it and find out what's important, what is trending, and deliver that information to you in a timely fashion. Well, if you're interested in that, the latest information on the hackers, the exploits, the vulnerabilities, if you want that information delivered to you in a meaningful way every day, then sign up for the free Recorded Future Cyber Daily Newsletter. All you have to do is go to recordedfuture.com slash intel. That's recordedfuture.com slash intel. And thanks very much to Recorded Future for sponsoring the show. Hello, hello and welcome to another episode of Smashing Security, episode 18. As always, I'm joined by my good buddy, Carole Theriault. Hello, Carole, what have you been up to?
Hi, Graham. I do have some news. I was last week at St. George's School. So hi to the girls at St. George's School in Harpenden. I was giving them a talk, trying to get them to consider tech as a career path. It was quite cool. Actually, a special shout out to Bernie, Sarah and Zoe. These are three girls from the school who did the latest Cyber First Girls competition. And they thought it was really great fun. So it was really cool meeting them. It was good. It's a really fun experience.
Sounds terrific. What about you? I've just come back from Paris. I was given a little talk. Yeah, mais oui. How's your French coming along? Ah, après le déluge. Ce sont les mots qui vont très bien ensemble. C'est horrible. Anyway, yes, I actually managed to tweet under the English channel. I was quite impressed that the Wi-Fi worked. Really? Of course, I was using a VPN tunnel when I was using the Wi-Fi. Ground. Sorry about that. And if you heard any other sign in the background, that is our special guest this week. Michael Hucks from PCmatic. How are things, Michael?
Things are great. Things are great. I'm out here in Oxford for my first time. Actually, first time in England. And Carole's been showing me around, and we've been having a great time. It's been awesome. God blimey, Governor. It's your first time in England. My first time.
Are you going to edit that out? I hope not. Let's pick Van Dyke. I just want to make him feel at home. Yeah, perfect. That's how it sounds, right? All right. Okay. Well, you know the score. What we do is we all bring a story, something which has caught our attention in the last week, something which we thought was interesting from the world of computer security and hacking and malware and vulnerabilities and threats and data breaches and all of those sort of things. And there's an old joke, isn't there? There's this joke which goes around, which is that, Windows, isn't that a virus? Isn't that malware? And people go, ha, ha, ha, ha, very jolly. Well, unfortunately, an antivirus product has made a bit of a clanger this week. Yep. By misidentifying Windows as being a virus. That seems rough. It does, doesn't it? Yeah. WebRoot. You can't do that. The people responsible for causing this havoc. They released a bad update. I think it was on Sunday or Monday. All of those computers, all of the computers relying on the companies, the organizations, the home users. It caused them serious issues. What it was doing was it was misidentifying various essential Windows operating system files as w32.trojan.gen.
So anyone that was running this software, the security software, and had it up to date would ping and say that they had this Trojan, quote unquote, on their machine?
Not just ping. Because what it then would do was it would quarantine those files. effectively cutting the legs off the computer so it could no longer run. And, you know, it shoved them in the sin bin, and your computer obviously became unstable and wouldn't work properly. Any files digitally signed by Microsoft were whisked away. Now, fortunately, you could reboot and you could restore the quarantined files, but it was causing mayhem. And I saw one Twitter user, a guy called Bob Ripley, he tweeted, I seem to have installed a nasty ransomware app. It's called WebRoot. They've already got... They already have my money. Should I contact the FBI? And you can kind of understand the frustration. I mean, let's put our hands up here, right? We work in the antivirus industry or have done in the past. And I think we've probably all worked for vendors where occasionally a small snafu might happen. Sure, it happens. Yeah, it happens.
I've seen one. I've experienced a few.
I think during our days at Sophos, we experienced a particularly bad one. But we're not the only company who've suffered from them. And obviously, WebRoot aren't having a great week this week. And they've had bad experiences in the past. In February, as the register reports, they shafted corporate PCs in a separate instant, causing them to display the dreaded blue screen of death. But this one has hit particularly badly. And it's affected all versions of Windows. It's also affected their managed service providers, other people who are using their engine. And even though the update apparently was pulled after about 15 minutes, too late, the damage was done. Because, of course, the onus these days is on getting out those updates to protect people's computers as quickly as possible, to protect against threats. And somehow or another, this particular update clearly shouldn't have passed quality control, should it? It shouldn't have got out.
Yeah. I mean, oh, God, the regrets must be going on and the blaming that must be going on and all the energy trying to fix this. I mean, they are under severe stress, I bet, over there.
Well, you know, I'm glad you said that because I think we all know it's obviously painful for their customers. We know it's painful for corporate customers, the users affected by this kind of snafu. But it's also horrible for the people manning WebRoot's tech support and managing their community forums. And, you know, you can imagine a customer feeling absolutely furious if hundreds of their computers have gone on the blink because of this. But, you know, it's hard. But don't lose your rag with the poorly paid guy in the support call centre who's probably, you know, you're the 900th person who's been screaming at them about this problem.
If he's lucky, he's maybe making time and a half to try and do the 80 hours this week to try and keep the customers happy. Right? Exactly.
So instead, you know, bottle your fury, vent it next time the sales guy comes around trying to sell you something, or you can negotiate a better deal, or speak to the company as X and say, what are you going to do to make up for this disaster? And how are you going to, most importantly, ensure that this never, ever happens anything like this again? Because it's so disastrous.
Have they actually fixed this problem yet? Has a fix come out and been delivered and everything's fine now, or is this still being dealt with?
Well, at the time of recording, so we're recording this on Tuesday afternoon, a fix isn't completely out there. They have posted up on their support forums some methods by which people can protect the systems, but they're still kind of working on exactly how to rectify this in the easiest way for everybody. And clearly, this is going to be something which is going to cause problems for some customers for a little bit of time until they've recovered. It wasn't just that they were misidentifying some Windows files. There were also users on Twitter and on WebRoot support forums saying, you know, this faulty update you've pushed out, it's also incorrectly blocking access to websites like Facebook, saying that they're phishing websites. So our users can no longer get onto Facebook. So to be honest, not all bad news then. Some good has come from this instead. That's a nice way of looking at it. Yeah, maybe some of the corporate clients will think, actually, can we keep that bit? We'd like to carry on blocking Facebook, but just
Fix all that stuff. Somehow with all of our computers being down, we've somehow managed to boost productivity at the same time. I can't imagine how that could work.
But, you know, I mean, Carole, you and I, we've hinted that we've had a problem before. I remember there was a massive Sophos false alarm a few years ago. Oh, it was longer than that, but yeah. And it was where an update actually knocked out Sophos' own updating system. Which meant that even though we had a fix, we couldn't update it. We couldn't update people's computers with the fix.
It was the worst catch 22 ever.
Yeah, an antivirus detecting itself. So if that's any constellation at all WebRoot, possibly Sophos shot itself even more in the foot. And I'm
Sure I did at least 100 hours that week, you know, working there that week. So anyway, yeah, be nice to the staff. Go after the executives if you want, but be nice to the staff. They're getting it in the neck right now. Exactly.
And they're trying to help you. And as with all these things, it's not worth losing your rag on the phone. It's not going to help anything. Of course, you have to answer to your bosses as well and explain why the computers are down. And, you know, there may be serious discussions which have to take place as to, you know, what you're going to do about that in future. But right now
We have to solve the problem.
Exactly. That's the important thing. So, you know, we feel sorry for WebRoot users and we feel sorry for WebRoot as well. Let's hope these kind of things happen less in the future. Michael, I hope you've got something more cheery for us.
I do, sort of, I guess. But let me start by asking you, both of you, a question. How many millennials do you think illegally stream movies and TV shows online in the US?
About a quarter, I'd say, probably.
How many millennials? Oh, no, I'd think more than a quarter. I would think 70%. Stream illegally. Yeah, 70% or something like that, don't you think? Because they're all addicted to, I don't know, Game of Thrones or something like that. I mean, everyone streams, but then, of course, you want to see it as quickly as possible. And I'm not sure, because most TV shows come out of the States. If it was from a country outside the States, went on an American show, maybe it's higher. Sorry, this is a very long answer I'm giving you.
Yeah, no, it's a detailed answer. Okay, I'm going to say I'm sticking. It's 25%. Okay, well, you were both off, but right in the middle of the two of you. You're both as right as the other one. I can say that. A new study found that more than half of 53% specifically of all North American millennials regularly use pirate streaming services to watch TV shows and movies.
Do they not have Amazon and all that stuff?
According to this, the preferred method is legal streaming. But in the age of not wanting to wait for anything and instant gratification, if that thing is not there, it's very accessible to go and just grab something for free online. And so most people are doing that.
Because there are these naughty sites these days where you don't have to go through all the effort of downloading a 1.3 gigabyte torrent or something like that. Where you can, it's like Netflix, right? You can just stream a movie. But it's illegal. I have encountered these sites where the movie might be released on DVD or something like that, and it isn't on Netflix yet. And you can just click and watch it.
And Graham, did you ever get in trouble for that?
I didn't say I've done it. Yeah, someone he knows did that once. It's not something actually I regularly do. But I have done it once or twice in the past. I must admit, hands up. Sorry about that. But my preference would normally be to go to BBC iPlayer or to Netflix or Amazon Prime. But there's a few issues with those. Just because it works.
Yeah, yeah. So let's talk BBC iPlayer. I use it. However, I have trouble using it when my VPN is turned on and I'm in the country. And I have trouble using it if I'm traveling because even though I'm a licensed user and a licensed payer, I can't watch it when I physically am outside the country.
Yeah, well, that is a problem. Some of these legitimately streaming sites, they do try and prevent the use of VPNs, which obviously runs contrary to what we would normally recommend in terms of security. But of course, when we are overseas, I've got a young child. If I'm overseas and he wants to watch his favourite TV show, I would quite like to be able to log into iPlayer or one of the others and show it to him because I'm a licence payer and I'm a registered user of that particular site. I think those sites will begin to provide a mechanism for doing that.
I think so too. And that's one thing you can see here across the board is it seems like the streaming services are kind of making it difficult for people to access the things they want, especially when that's what we're used to. And when it comes to these things, if you're with the BBC, if you're out, you can't watch it. If it's not on Netflix, but it's on Hulu or it's in Netflix in the UK, but not in the US. And there doesn't seem to be this perfectly aggregated program that's been made to do it. And so when people are having a hard time finding what they want there, two links down from that is an ad saying, well, here's you can watch it for free. Yeah. Can't really blame people for clicking on it, I guess.
But it is interesting how annoying it is, because like you live in the States, for example, and I remember I watched that documentary. I think I recommend it to both of you. I watched that documentary called Tickled. Everyone out there totally watch it. And I think you watched it, right?
Yes, I have. It was pretty good.
Yeah, it was great. So I obviously told Michael about it, and he can't. It's not available for him on Netflix because they have a different version of Netflix for the UK and US. Right. And he doesn't have access to it yet. So, yeah.
Well, I know what you two are doing tonight, then. You can get a cup of cocoa and watch Tickled. Yes, that's exactly what you can do. Soak it all in while I'm here.
Yeah, while he's in the UK. Go blimey, Governor. That's what you need to be doing, isn't it?
Now, imagine the reason why you're raising this issue, however, is not just because we care about the movie industry, but because of the potential security implications.
Way to go steal his thunder. Well... I'm just saying. He invited guests. It was coming around to it. Yeah, he invited guests over and then just steal his story. Is that right, Michael? Is that something we should be concerned about?
Because if I was a bad guy. Yeah, which if, if. Thank you. I might disguise my malware as a video codec which you need to download in order to stream the latest episode of Lord knows what. Or it's a natural thing to do. And just as we've seen, for instance, apps which have been malware infected and pirated and put up onto torrents, equally, there's no reason to think that a stream insider, an illegitimate stream insider, we want to call it that, might attempt to trick you into installing something or have some booby-trapped, malformed flash player, what's-it, just ready to infect your computer.
And I guess, yeah, you have recourse with the big boys, right? Like if you go to Netflix and there's a problem, at least there's a place for you to complain if something goes wrong. Yeah, and Netflix, of course, you know, if anything were to go wrong on Netflix, it would go wrong for millions and millions of people worldwide and be very obvious. So hopefully nothing like that will happen. But certainly these other sites you have to be a little bit more cautious about. I wonder if it's naive to assume that a lot of people don't know what the difference between free and illegal is. What is allowed to be free?
So what advice should we be giving people to protect them better against these sort of things? Don't do it. Okay, so say someone absolutely must stream something from a site that, we're assuming it's legal, and they have to stream a site they do not know, and therefore can't trust. I'll tell you what you might want to do. I mean, first of all, you've set this example, Carole, where you've said you've absolutely got to watch something. First of all, let's question that. Is there anything you've absolutely really got to watch?
Yes, definitely.
But if you absolutely do have to watch something for some reason, then you might be an awful lot safer maybe using an iOS device. So using your iPhone or your iPad rather than Android or using Windows.
So you're in the walled garden concept?
Yeah, because generally they're more secure. And there's less opportunities to exploit it. And the hackers are less likely to be attempting to exploit on those particular devices.
Yeah, I agree.
And be very wary of any site which asks you to register or give the email address. And if you are going to do that, give them a throwaway email address instead. Don't give them your personal information in order to watch the movie. And that should avoid most of the threats in that way. But generally, I'd say, you know, get a little bit of patience or look for the video on YouTube or something.
Thanks, Granddad.
Well, you know, that is my role, Carole, on this podcast is to be the curmudgeonly granddad.
You do it so well.
Well, thank you, Carole.
You can wait. People can wait a little bit. And if anyone needs any more reason to not do it, I think that another repercussion just outside of security is how much it can cost you. I mean, people have been charged and ordered to pay upwards of over half a million dollars for illegally downloading 30 songs. I looked at one today.
You are kidding me.
This guy was charged $22,500 per song that he downloaded and shared online. And this is a student in Boston who just downloaded some songs, just as everyone else has always done.
But he's also sharing them online, though, isn't he? He's not just downloading them. I mean, that is obviously the worst bit of it. He's then encouraging others.
Yeah, but how many people don't even realize that?
I think I'm really glad you brought the story. I mean, I think we just have to be aware that if they go after you, it's big bucks.
It can be bad. Well, I'm going to say show a little bit of self-restraint for goodness sake. Wait until it arrives in your iPlayer or Hulu or whatever.
I seem to remember you with Doctor Who chomping at the bit for the next episode.
Carole, that's Doctor Who. That's a whole different story.
Yeah, well, there's certain ones that don't fall within the same category as everything else.
Thank you, Michael. I really you as a guest. You're excellent. Carole, what have you got for us?
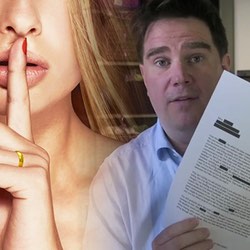
Ah, well, gents, cast your minds back to Ashley Madison. What is the first thing that comes to mind?
I think of someone with collagen implanted lips and a finger up to them going, shh. I can see the logo.
So you're thinking of the website rather than the hack that happened in July 2015?
Oh, sorry. No, I was thinking of the hack. Obviously, I was thinking of the hack.
Oh, I was just thinking of my homepage. So, yeah, we went to different places. But that's all right. Yes, you did. Well, yes. Okay. So onwards, onwards. So do you remember, just to recap, so it was the Impact Team that stole just shy of 13 gigs of user data from the adulterist paradise.
It was a great one. I thought that was fantastic. Yeah, it was such a
Great story. So we can't really tell you how many of the people that is, but I think we can say most of the men were real. So a lot of people were affected. Now, why did they get hacked? The goal was to shut down this site because it was for moralistic reasons of the fact that they destroyed families and the rest. However, the threat was we're going to publish the identities of all the registered users, regardless of whether they use the services or not. So, of course, we all know what happened. Ashley Madison did not shut down. Impact Team did publish the data on the dark web. And as we remember, the media went bananas. Now, there were obviously horrific consequences. I think there were two suicides in Toronto, and there was a few down south, I think New Orleans. There was a few suicides down there as well. So, yeah, and this is a few years ago, right? So you think that's, no, everyone's forgotten that story. That happened two years ago. Why am I talking about it today? Well, a blackmail campaign has just been launched, and it's using the data from this dump. Oh, saw that coming. So what they've done is they've contacted targeted Ashley Madison users. So from the email addresses that they had collated and published and the email read as follows. So on May 1st, 2017, we are launching our new site, Cheaters Gallery, exposing those who cheat and destroy families. We will launch the site with a big email to all the friends and families of cheaters taken from Facebook, LinkedIn and other social sites. They will include you if you do not pay to opt out. Yeah so the payment is a 0.4 of a bitcoin or 500 US dollars right so what do you do right what do you do if you're on that list if you've received this email like do you play the ostrich and convince yourself that they're bluffing do you pay up and hope that it keeps a lid on everything or do you just tell them to themselves yeah
Tough it's tough without being in the situation i i mean it seems very scary since they say that they're going to launch a site with a big email. So that big email, who knows what that's going to include.
Well, I wouldn't tell them to f themselves. I think that's just like poking an angry bear with a stick, isn't it? I think that's just going to cause trouble. You don't want them to focus any more attention on you. Yeah, you should shy away from the bullies. I don't think you should pay up either. Because if you pay up, you've revealed to them that you're someone who's prepared to pay. Right? The trusted cash cow. Yeah. Yes.
Yeah. You've actually just labeled yourself as a trusted person to actually attack because they know you're going to deliver.
And if you've paid once, maybe you'll pay twice or maybe you'll pay more next time. And it's like you clearly don't want this information to leak out. So I'm going to try and get more money out of you. So don't give in to blackmailers. Sure.
And I would imagine the moral compass of the people putting on this scheme, they'll be like, well, he paid. So let's just call it quits and let him go. Yeah. I mean, what stops them from doing this over and over and over and over until they either wipe you completely clean or just you decide not to pay, but you've already paid 10 times?
Yeah. I also think you need to think about how likely is it that the criminals are actually going to go through with their entire plan? So, okay, they're saying they're going to create this site, Cheaters Gallery. Yeah. And expose people's names. Well, first of all, these people's names are already exposed. The Ashley Madison database has been out there for two years. Yeah. And there have been other attempts to blackmail them in the past. I've received emails and people have forwarded me letters, which they've received because they were members of Ashley Madison. Yeah. And they've been, in some cases, very worried about it. In some occasions, they've even received letters sent to their wives at their homes.
You would think, right, that most of them who were involved in the original hack have come clean about being on the site because they had to go through this already. I mean, maybe a few got through because they deleted the email or somehow was able to hide away from it.
I mean, there's some other aspects of this. The first thing which I want to focus on is put yourself in the point of view of the blackmailer. What have they got to gain from going through that entire database and scouring Facebook and LinkedIn and trying to work out who your partners are and who your family members are and then try and reach them as well? Well, that's an awful lot of effort to go to. And you're not going to make any money out of it.
No, but they, in the email, in the initial email that they send out, just to show they mean business, they included some of the information from the data dump, the original data dump. Yeah,
From the data dump. That's easy. Anyone can get their hands on that within 10 minutes on the internet. Well, and that's what they're Suggesting they're going to do, right? They're saying they're planning to put all this online in a cheater's gallery. And I think there's the extra gravy, if you want, of embarrassment by saying we're going to go after your loved ones and tell them what you've done. Yeah. They might do it in a handful of examples, but they're not going to do it for most people.
Yeah, I'm trying to agree.
And even if they do create a cheater's gallery with everyone's detail up there, well, whoopee-doo, Mr Blackmailer, because there's already plenty of websites where you can enter people's names and see if they occur in the Ashley Madison database. And furthermore, Ashley Madison never bothered to verify people's email addresses. So you could put in, and I believe, for instance, Tony Blair's email address, former Prime Minister of Great Britain, his email address was in the Ashley Madison database dump. But I don't think he was cheating on Cherie.
Yeah, and there are stories of that. It's really, there's stories of people who say that they have been added, which obviously I'm sure that's true in some cases, and I'm sure in other cases that's the story you're using.
I'm sure it's a good go-to excuse. I mean, absolutely, Carole. I'm sure some people will use that excuse. Of course they will. But it's an excuse.
Well, one thing I would say is do not try and seek out the data dump to see if you are on it or not. Check out a service like, for example, Troy Hunt's excellent service, Have I Been Pwned? And you can put in your email address at that location to see safely whether you're on any of these lists and where your name may have been found, your email address and some of your data.
And be more careful in future. If you're going to sign up, it doesn't matter if it's an adultery — I mean, Ashley Madison sold itself and marketed itself a great deal as having an affair and all that kind of business. But even if it isn't that kind of site, even if it's just a regular dating site, if you're signing up for it tomorrow, be careful what details you give it and what email address and so forth. You might give it because in 15 years time, when you are in a healthy relationship and that site gets hacked and your information comes out, your then current partner may think, well, what are you doing as a member of that site? And you'll be there saying, well, I joined it 15 years ago.
But all these sites often require payment. And in order to provide payment, they often require credit card details. Now, obviously, some have PayPal and some have other methods of payment, which can be better to protect your anonymity should the worst happen. But, you know, a lot of these sites demand that you provide legitimate credentials before you go forward.
Not all, but there's a lot to do. And so, you know, caveat emptor, right? Be careful what you're buying and what you're joining. And I think we're all agreed. Don't pay the blackmailers, right?
Absolutely. Please do not pay. Because if everyone didn't pay, if the payback was low, then wouldn't the criminals go, oh, that didn't work. Maybe we should do something else. That data's dead.
Right? And if this works for them, it encourages other people to do this on other things.
We say don't pay. We say don't respond to the blackmailers either. In fact, I would say go one step further and report the blackmail extortion attempt to the authorities, because it may well be that they are investigating the case and that they need evidence.
That's a good point.
If you have any, pass it over to them so that they can try and find out who these blackmailers are. Good call. All righty. Well, on that cheery note, I think we're coming to the end of the show, aren't we? If you enjoyed the show, make sure to subscribe to us on iTunes or on Google Play Music or Stitcher or TuneIn or Overcast.
And if you like us a lot, please leave us a review. It really helps. And a big shout out to Recorded Future, our sponsors this week. You can sign up to their Cyber Daily newsletter and get their latest insights at recordedfuture.com slash intel.
Well, thanks very much for joining us this week.
Thank you, Michael, as well. I hope the podcast wasn't too painful for you.
Thanks for having me. It was a lot of fun. I'll be back someday. If you liked the show, tell your friends, let us know what you think. You can go to www.smashingsecurity.com and you will find an email contact form and a link to our Twitter and all the other places where we hang out online. And until next week, toodaloo, bye-bye.
Bye.
Au revoir.
Show notes:
- Webroot antivirus goes bananas, starts trashing Windows system files – The Register.
- Webroot causes massive headaches after falsely flagging Windows files as malicious – Graham Cluley.
- Tweet by Webroot user Bob Ripley – @M5_Driver.
- W32.Trojan.Gen false positive – advice for home users – Webroot.
- W32.Trojan.Gen false positive – advice for business users – Webroot.
- Most millennials regularly stream pirated content, survey finds – Torrent Freak.
- Malware, data theft, and scams: researchers expose risks of free livestreaming websites – Ku Leuven.
- File sharer hit with $675,000 fine – Digital Trends.
- Ashley Madison blackmail roars back to life – ZDNet.
This episode of Smashing Security is made possible by the generous support of Recorded Future – the real-time threat intelligence company whose patented machine learning technology continuously analyzes technical, open, and dark web sources to give organizations unmatched insight into emerging threats.
Sign up for free daily threat intelligence updates at recordedfuture.com/intel.
Thanks to Recorded Future for their support.
Hope you enjoy the show, and tell us what you think. You can follow the Smashing Security team on Bluesky.
Remember: Subscribe on iTunes to catch all of the episodes as they go live. Thanks for listening!



I hadn't known about the Great Sophos Disaster.
How did they recover from a situation where they can't push out an update? And how did they fail to scan their own software?
Because of the scanning method that DSAV-Findvirus used (single point), I don't think we ever had a false alarm.
Here is how The Register reported the Sophos foul-up: https://www.theregister.co.uk/2012/09/20/sophos_auto_immune_update_chaos/
If I recall correctly, the first fix was a manual one – on every computer that had had its Sophos Anti-Virus update feature borked by umm.. Sophos Anti-Virus.
Later there might have been a tool produced that could be rolled out across the network as users logged in, but that's lost in the mists of time for me.
Regarding "how did they fail to scan their own software"? My understanding is that the false detection was spotted during testing…. and then human error meant that someone overrode the warning and pushed out the update anyway…
But it's five or so years ago now, so that may not be right.
I seem to recall there may have been occasional false alarms (but nothing like what McAfee and others suffered from) when it came to file compressors, Dmitry's heuristics, etc. But they were pretty rare. David Emm probably remembers better than me.
BTW, it's 20 years since we put out this press release. Time files…
http://www.prnewswire.co.uk/news-releases/mcafee-pleads-with-dr-solomons-to-reduce-virus-detection-rate-156451045.html