Imagine that you want to infect someone else’s Android smartphone, but you cannot get physical access to the device.
The normal method would be to attempt to trick the phone’s owner into installing a malicious app, or fool them into clicking on a link that points to a webpage that exploits a vulnerability that silently installs malware onto the device.
That would be the normal method.
But Joshua Drake, a security firm with Zimperium, has found a serious vulnerability that does away with all that, and requires no interaction at all by the user. In fact, the vulnerability could allow a hacker to infect your mobile phone, while you’re fast asleep.
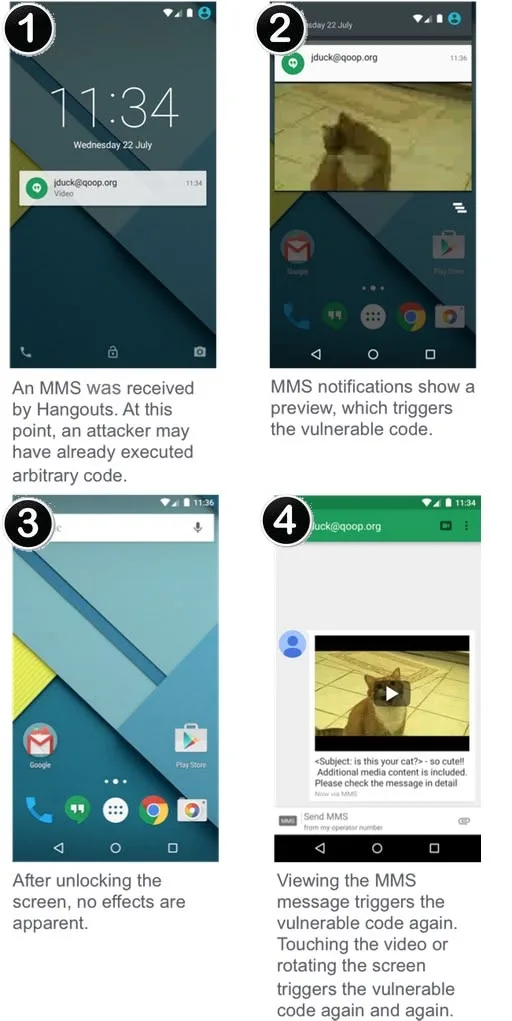
What Drake has uncovered is a way of breaking into an Android user’s phone, and hijacking control of it, just by sending a MMS message with a maliciously-crafted movie file.
Once in place, the malware could secretly steal information and spy on your conversations without your knowledge.
The attack, which the researcher describes as “much worse” than Heartbleed, exploits multiple remote code execution vulnerabilities found in version 2.2 of Android and later.
Most vulnerable, according to Zimperium’s report, are versions of Android prior to Jelly Bean (version 4.1) which account for something like 11% of the Android population.
The weak point of Android being exploited is “Stagefright”, a code library used to process popular media formats.
A fully weaponized successful attack could even delete the message before you see it. You will only see the notification. These vulnerabilities are extremely dangerous because they do not require that the victim take any action to be exploited. Unlike spear-phishing, where the victim needs to open a PDF file or a link sent by the attacker, this vulnerability can be triggered while you sleep. Before you wake up, the attacker will remove any signs of the device being compromised and you will continue your day as usual—with a trojaned phone.
The problem doesn’t end there, however, as the vulnerability can also be exploited via other vectors, including the more traditional attack method of luring users to a boobytrapped webpage.
As CNET reports, the precise nature of the attack may change depending on which applications your Android device is using – for instance, the built-in messaging app or Google Hangouts:
Those using the standard Messenger app built into Android would need to open the text message (but not necessarily watch the video) to fall victim to the trap. Those who are running Google’s Hangouts app to handle text messaging, however, need not even open the application, according to Zimperium. As soon as Hangouts receives the text, it processes the video and the hacker is in. (The Google’s Play app marketplace says Hangouts has been downloaded between 1 billion and 5 billion times.)
Fortunately, Josh Drake believes in responsible disclosure and not only informed Google’s security team of the serious security hole but also provided patches for their code at the same time.
But, unfortunately, the problem doesn’t end there. Because even if Google patches Android, that’s very different from the estimated 950 million Android devices around the world *receiving* updates to their vulnerable devices.
Over-the-air updates for Android are notoriously hard to get hold of for some devices.
Even if you *want* to upgrade the operating system on your Android phone or tablet you might not be able to, because an update is only going to be available for those devices with the assistance and goodwill of Google, the device’s manufacturer and your mobile phone carrier.
History, sadly, has often shown us that older Android devices are left stranded without an easy path for OS updates. This is a serious problem which, bearing in mind the regularity that critical security vulnerabilities are found in versions of Android, really needs to be fixed.
The only silver lining is that, so far at least, there is no evidence that the flaw has been exploited by malicious hackers in the wild. Nonetheless, if you are one of the lucky Android users who finds themselves able to to install an update, I would recommend that you did as soon as possible.
Drake is planning to present his research at Black Hat and DEF CON next month, where more details of the vulnerabilities will be shared.
This article originally appeared on the Lumension Security blog.