September 23, 2015
Category: Apple
September 21, 2015
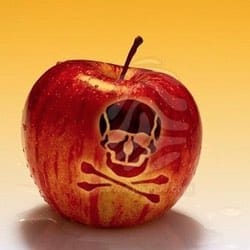
Tell us how to infect an iPhone remotely, and we’ll give you $1,000,000
Tell us how to infect an iPhone remotely, and we’ll give you $1,000,000
September 19, 2015
XcodeGhost malware sneaks into the App Store, spooks millions of iOS users
September 17, 2015
How to block ads and prevent tracking in iOS 9 Safari
September 16, 2015
AirDrop bug could let hackers silently plant malware on your iPhone or Mac
AirDrop bug could let hackers silently plant malware on your iPhone or Mac
September 10, 2015
Visual hacking and the iPhone 6s’s new camera
August 13, 2015
How to stop pervy pics popping up on your iPhone